Fragmente (DPL)[]
Svr [S. 1-111]
025... 017... 019... 016... 033... 064... 123... 124... 128... 110... 130... 131... 132... 133... 136... 137... 139... 140... 085... 086... 074... 001... 002... 002... 109... 002... 001... 078... 033... 014... 072... 013... 082... 083... 043... 045... 087... 101... 027... 059... 060... 046... 051... 110... 066... 005... 009... 011... 012... 013... 092... 093... 053... 052... 051... 050... 049... 048... 020... 055... 002... 095... 097... 098... 032... 102... 077... 082... 081... 080... 074... 099... 103... 104... 111... 088... 085... 018... 019... 023... 024... 025... 027... 041... 019... 030... 030... 026... 029... 022... 023... 024... 025... 026... 028... 029... 013... 003... 033... 038... 039... 040... 110... 102... 008... 104... 066... 067... 073... 094... 069... 070... 058... 055... 049... 065... 047... 045... 044... 032... 031... 007... 008... 006... 007... 059... 060... 048... 028... 059... 028... 110... 015... 109... 071... 046... 056... 057... 054... 055... 054... 032... 034... 035... 036... 037... 040... 042... 043... 096... 097... 036... 032... 035... 037... 034... 074... 077... 021... 048... 049... 071... 072... 054... 041... 106... 050... 087... 100... 102... 099... 075... 075... 067... 068... 002... 027... 029... 032... 042... 043... 046... 047... 056... 060... 063... 064... 061... 062... 050... 051... 021... 022... 022... 023... 015... 031... 055... 014... 059... 064... 065... 015... 011... 030... 031... 088... 089... 090...
209 Fragmente
Dubletten, S.:
6 Fragmente
TO DO[]
004 010
076 079
084 089 090 091
105 107 108
Angelegte Quellen / Fragmente - gesichtet und ungesichtet (DPL)[]
Fragmente[]
| Fragment | S. | Z. | Quelle | S. | Z. | Typus | Status | (Ersteller) Sichter |
|---|---|---|---|---|---|---|---|---|
| Svr/Dublette/Fragment 002 22 | 2 | 22-25 | Bryan 1998 | online | 0 | KeineWertung | ZuSichten | (SleepyHollow02) |
| Svr/Dublette/Fragment 022 12 | 22 | 12-15 | Pitts-Moultis Kirk 1999 | 258 | 10 ff. | KeineWertung | ZuSichten | (SleepyHollow02) |
| Svr/Dublette/Fragment 044 12 | 44 | 12-18 | Weitzel et al 1999 | online | 0 | KeineWertung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Dublette/Fragment 047 02 | 47 | 2-4 | Raman 1998 | online | 0 | KeineWertung | ZuSichten | (SleepyHollow02) |
| Svr/Dublette/Fragment 060 14 | 60 | 14-19 | Raman 1998 | online | 0 | KeineWertung | ZuSichten | (SleepyHollow02) |
| Svr/Dublette/Fragment 085 03 | 85 | 3-7 | Pindyck 1989 | 8 | 6 ff. | KeineWertung | Gesichtet | (Hindemith) Schumann |
| Svr/Fragment 001 02 | 1 | 2-24 | Kobielus 2000 | 57 | left col., 10 ff. | Verschleierung | Gesichtet | (Klgn) SleepyHollow02 |
| Svr/Fragment 001 25 | 1 | 25-29 | Shankar 1999 | 47 | first paragraph | Verschleierung | Gesichtet | (Klgn) Schumann |
| Svr/Fragment 002 02 | 2 | 2-3 | Shankar 1999 | 47 | - | KomplettPlagiat | Gesichtet | (Klgn) Schumann |
| Svr/Fragment 002 05 | 2 | 5-8 | Bakos 1997 | 1 | 11 ff. | Verschleierung | Gesichtet | (Hindemith) Schumann |
| Svr/Fragment 002 08 | 2 | 8-10 | Bailey Bakos 1997 | online | 0 | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 002 11 | 2 | 11-12, 13-15 | Norman 1999 | 44 | 15 ff. | KomplettPlagiat | Gesichtet | (Schumann) WiseWoman |
| Svr/Fragment 002 22 | 2 | 22-25 | Webber 1998 | 38 | right col., 9 ff. | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 003 04 | 3 | 4-8, 21-23, 28-29 | Ritz 1995 | 1, 6, 7 | 1: 28 ff.; 6: last 2 lines; 7: 7 f. | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 005 25 | 5 | 25-27 | Bakos 1998 | 35 | 15 ff. | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 006 01 | 6 | 1-9 | Schmid 1993 | 3 | 3: left col., 4 ff.; center col., 17 ff.; right col., 5 ff., 22 ff.; | BauernOpfer | Gesichtet | (SleepyHollow02) WiseWoman |
| Svr/Fragment 007 01 | 7 | 1-2 | Schmid 1993 | 3 | right col., 51 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 007 03 | 7 | 3-8, 10-13, 101-103 | Zimmermann 1998 | 379 | 29 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 008 01 | 8 | 1-12 | Zimmermann 1998 | 380 | 4 ff. | KomplettPlagiat | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 008 14 | 8 | 14-21, 24-28 | Bakos 1998 | 37, 39, 40, 42 | 37: left col., 13; 39: right col., 17 ff.; 40: left col., 39 ff.; 42: left col., 26 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 009 01 | 9 | 1-5, 9-16, 21-24 | Bakos 1998 | 39, 40, 41 | 39: right col. last paragraph; 40: left col., 1 ff., right col., 4 ff.; 41: left col., 9 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 011 04 | 11 | 4-10 | Enigma 1999 | online | 0 | Verschleierung | Gesichtet | (Schumann) WiseWoman |
| Svr/Fragment 011 12 | 11 | 12-31 | Spider's Apprentice 2000 | online | 0 | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 012 01 | 12 | 1-10 | Spider's Apprentice 2000 | online | 0 | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 013 02 | 13 | 2-9, 11-14 | Lee 1998 | 3 | left col., 34 ff.; right col., 4 ff., 38 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 013 15 | 13 | 15-22 | Lee 1998a | 19, 20 | 19: right col, 41 ff.; 20: center col., 15 ff.; right col.: 1 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 013 29 | 13 | 29-31 | Weitzel et al 1999 | online | 0 | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 014 03 | 14 | 3-11 | Weitzel et al 1999 | online | 0 | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 014 22 | 14 | 22-24 | Berners-Lee et al 2001 | 42 | right col., 14 ff. | KomplettPlagiat | Gesichtet | (Schumann) WiseWoman |
| Svr/Fragment 015 01 | 15 | 1-5 | Murch Johnson 1999 | 71, 72 | 71: 7 ff.; 72: 25 ff. | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 015 101 | 15 | 101-102, 106-112 | Bartlett 1997 | online | 0 | Verschleierung | Gesichtet | (Schumann) WiseWoman |
| Svr/Fragment 015 12 | 15 | 12-13 | Arbortext 1999 | online | 0 | KeineWertung | ZuSichten | (Schumann) |
| Svr/Fragment 016 02 | 16 | 2-10, 15-17, 20-23, 25-32 | Berners-Lee et al 2001 | 36 | 36: right col., 15 ff.; 37: left col., 1 ff. center col., 9 ff., right col., 1 ff. ; 38: left col., 1 ff., right col., 3 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann WiseWoman |
| Svr/Fragment 017 01 | 17 | 1-6, 8-19, 101-114 | Berners-Lee et al 2001 | 37, 38, 39, 42 | 37: right col., last paragraph; 38: left col. 1 ff., right col. 25 ff., 36 ff.; 39: left col. 1 ff., center col. 2 ff., 20 ff., right col., 1 ff.; 42: left col., 9 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann WiseWoman |
| Svr/Fragment 018 15 | 18 | 15-18 | Pitts-Moultis Kirk 1999 | 705 | 14-18 | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 019 07 | 19 | 7-10 | Berners-Lee et al 2001 | 38 | right col., 29 ff. | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 019 11 | 19 | 11-16 | Pitts-Moultis Kirk 1999 | 707 | 21 ff. | KomplettPlagiat | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 019 21 | 19 | 21-27 | Kotok 1999 | online | 0 | KomplettPlagiat | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 020 08 | 20 | 8-21 | W3C 1999 | online | 0 | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 021 01 | 21 | 1-7 | Schwartz 2001 | 200, 201 | 200: last paragraph; 201: 2 ff. | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 021 12 | 21 | 12-32 | Seybold report on internet publishing 1997 | online | 0 | Verschleierung | Gesichtet | (Schumann) WiseWoman |
| Svr/Fragment 022 01 | 22 | 1-4 | Seybold report on internet publishing 1997 | online | 0 | KomplettPlagiat | Gesichtet | (Schumann) WiseWoman |
| Svr/Fragment 022 06 | 22 | 6-20 | DeRose 1999 | online | 0 | Verschleierung | Gesichtet | (Schumann) WiseWoman |
| Svr/Fragment 022 20 | 22 | 20-32 | Funke 1998 | online | 0 | KomplettPlagiat | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 023 01 | 23 | 1-8 | Funke 1998 | online | 0 | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 023 09 | 23 | 9-11, 14-22 | DeRose 1999 | online | 0 | Verschleierung | Gesichtet | (Schumann) WiseWoman |
| Svr/Fragment 023 30 | 23 | 30-32 | Pitts-Moultis Kirk 1999 | 97 | 28 ff. | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 024 01 | 24 | 1-2, 14-15, 17-21, 30-35 | Pitts-Moultis Kirk 1999 | 97, 98 | 97: 6 f., 16 ff., 30 ff.; 98: 5 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 024 24 | 24 | 24-30 | Funke 1998 | online | 0 | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 025 02 | 25 | 2-21 | Pitts-Moultis Kirk 1999 | 98, 99, 100 | 98: 23 ff.; 99: 16 ff., 31 ff.; 100: 1 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 025 23 | 25 | 23-27, 30-32 | Berners-Lee et al 2001 | 42 | right col., 18 ff., 40 ff., 47 ff. | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 025 27 | 25 | 27-29 | Funke 1998 | online | 0 | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 026 01 | 26 | 1-3, 9-27 | Funke 1998 | online | 0 | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 026 06 | 26 | 6-8, 29-30 | Wong 1998 | online | 0 | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 027 06 | 27 | 6-18 | Wong 1998 | online | 0 | KomplettPlagiat | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 027 22 | 27 | 22-26 | Norman 1999 | 49 | 1 ff. | Verschleierung | Gesichtet | (Schumann) WiseWoman |
| Svr/Fragment 027 28 | 27 | 28-31 | Pitts-Moultis Kirk 1999 | 480 | 2 ff., last 3 lines | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 028 05 | 28 | 5-19 | Sanborn Lattig 2000 | 16 | left col., 1 ff. | KomplettPlagiat | Gesichtet | (Klgn) Schumann |
| Svr/Fragment 028 19 | 28 | 19-21 | Johnson 1999 | 81 | left col., 39 ff. | KomplettPlagiat | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 028 22 | 28 | 22-32 | Funke 1998 | online | 0 | KomplettPlagiat | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 029 01 | 29 | 1-10, 18-21, 28-30 | Funke 1998 | online | 0 | KomplettPlagiat | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 029 11 | 29 | 11-17 | Wong 1998 | online | 0 | KomplettPlagiat | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 029 22 | 29 | 22-27 | Norman 1999 | 49 | 7 ff. | KomplettPlagiat | Gesichtet | (Schumann) WiseWoman |
| Svr/Fragment 030 05 | 30 | 5-10, 17-23 | Kotok 2000a | online | 0 | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 030 12 | 30 | 12-16, 23-29 | Kotok 2000 | online | 0 | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 030 30 | 30 | 30-31 | Enigma 1999 | online | 0 | Verschleierung | Gesichtet | (Schumann) WiseWoman |
| Svr/Fragment 031 01 | 31 | 1-2, 8-10 | Enigma 1999 | online | 0 | Verschleierung | Gesichtet | (Schumann) WiseWoman |
| Svr/Fragment 031 02 | 31 | 2-5 | Bartlett 1997 | online | 0 | KomplettPlagiat | Gesichtet | (Schumann) WiseWoman |
| Svr/Fragment 031 12 | 31 | 12-17 | Weitzel et al 2000 | 1 | left col., 21 ff. | KomplettPlagiat | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 032 01 | 32 | 1-2 | Weitzel et al 2000 | 1 | right col., 5 ff. | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 032 03 | 32 | 3-4, 5-11 | Erdmann Studer 1999 | online | 0 | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 032 13 | 32 | 13-20 | Norman 1999 | 43, 44 | 43: last paragraph; 44: 1 f. | Verschleierung | Gesichtet | (Schumann) WiseWoman |
| Svr/Fragment 032 21 | 32 | 21-23 | Parfett 1992 | 5 | 16 ff. | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 032 23 | 32 | 23-32 | Emmelhainz 1990 | 21, 81 | 21: 18 ff.; 81: 7 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 033 01 | 33 | 1-3 | Ritz 1995 | 12 | last 3 lines | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 033 03 | 33 | 3-8 | Weitzel et al 1999 | online | 0 | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 033 09 | 33 | 9-25 | Carroll 2000 | online | 0 | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 034 02 | 34 | 2-11 | Parfett 1992 | 49 | 9 ff. | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 034 13 | 34 | 13-16, 17 | Emmelhainz 1990 | 82 | 21 ff. | BauernOpfer | Gesichtet | (Schumann) SleepyHollow02 |
| Svr/Fragment 035 10 | 35 | (1-3), 10-17, 30-31 | Emmelhainz 1990 | (14), 16, 80, 89 | (14: 31-34); 16: 5 ff.; 80: 28 ff.; 89: 5 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 035 20 | 35 | 9-10, 20-28 | Parfett 1992 | 40, 42 | 40: 20 ff.; 42: 6 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 036 01 | 36 | 1-6 | Emmelhainz 1990 | 16, 89 | 16: 26 ff.; 89: 5 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 036 07 | 36 | 7-14 | Parfett 1992 | 49 | 18 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 037 01 | 37 | 1-6, 8-9, 11-17, 18-21 | Emmelhainz 1990 | 17, 89 | 17: 16 ff., 28 ff.; 89: 11 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 037 17 | 37 | 17-18, 21-29 | Parfett 1992 | 59, 61 | 59: last 6 lines; 61: 7 ff., last paragraph | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 038 01 | 38 | 1-6, 10-23, 28-32 | Ritz 1995 | 51, 52, 53 | 51: 7 ff.; 52: 1, 13 ff.; 53: 1 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 039 01 | 39 | 1-3, 5-32 | Ritz 1995 | 53, 54 | 53: 3 ff.; 54: 1 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 040 04 | 40 | 4-8 | Ritz 1995 | 55 | 23 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 040 09 | 40 | 9-29 | Parfett 1992 | 2, 12, 13, 17 | 2: 13 ff.; 12: last 5 lines; 13: 5 ff.; 17: 2 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 041 02 | 41 | 2-7, 12-13, 17-26 | O'Callaghan Turner 1995 | online | 0 | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 041 09 | 41 | 9-11, 15-18 | Parfett 1992 | 16 | 22 ff., 30 ff. | BauernOpfer | Gesichtet | (Schumann) SleepyHollow02 |
| Svr/Fragment 042 01 | 42 | 1-5, 14-19 | Parfett 1992 | 14, 19 | 14: 19 ff.; 19: 29 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 042 07 | 42 | 7-9, 20-30 | Norman 1999 | 44 | 15 ff. | KomplettPlagiat | Gesichtet | (Schumann) WiseWoman |
| Svr/Fragment 043 01 | 43 | 1-3 | Norman 1999 | 44 | 30 ff. | KomplettPlagiat | Gesichtet | (Schumann) WiseWoman |
| Svr/Fragment 043 10 | 43 | 10-16, 17-24 | Parfett 1992 | 2, 19, 20 | 2: 25 ff.; 19: 22 ff.; 20: 1, 4 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 043 26 | 43 | 26-29 | Weitzel et al 2000 | 1 | right col., 10 ff. | KomplettPlagiat | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 044 10 | 44 | 10-21 | Weitzel et al 2000 | 1, 2 | 1: right col., 20 ff.; 2: left col., 1 | KomplettPlagiat | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 045 17 | 45 | 17-19 | Weitzel et al 2000 | 2 | left col., 25 ff. | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 045 23 | 45 | 23-27, 29-31 | Weitzel et al 1999 | online | 0 | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 046 05 | 46 | 5-14 | Edwards 1999 | online | 0 | KomplettPlagiat | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 046 16 | 46 | 16-17, 23-32 | Norman 1999 | 44, 45 | 44: last paragraph; 45: 26 ff. | KomplettPlagiat | Gesichtet | (Schumann) WiseWoman |
| Svr/Fragment 046 17 | 46 | 17-21 | Raman 1998 | online | 0 | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 047 01 | 47 | 1-4 | Norman 1999 | 45 | 29 ff. | KomplettPlagiat | Gesichtet | (Schumann) WiseWoman |
| Svr/Fragment 047 12 | 47 | 12-18, 21-30 | Weitzel et al 2000 | 2 | left col., 36 ff.; right col., 1 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 048 01 | 48 | 1-14 | Houser et al 1996 | 5, 6 | 5: 22 ff.; 6: 1 ff. | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 048 19 | 48 | 19-21, 23-27 | ECOOP 2001 | online | 0 | Verschleierung | Gesichtet | (Schumann) SleepyHollow02 |
| Svr/Fragment 048 28 | 48 | 28-32 | Webber 1998 | 40 | left col., 2 ff.; right col., 11 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 049 01 | 49 | 1-6 | ECOOP 2001 | online | 0 | Verschleierung | Gesichtet | (Schumann) SleepyHollow02 |
| Svr/Fragment 049 13 | 49 | 13-19 | Peat Webber 1997 | online | 0 | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 049 24 | 49 | 24-30 | Webber 1998 | 40 | left col., 4 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 050 01 | 50 | 1-5 | XML EDI Group 1999 | online | 0 | Verschleierung | Gesichtet | (Schumann) WiseWoman |
| Svr/Fragment 050 11 | 50 | 11-19 | Peat Webber 1997 | online | 0 | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 050 19 | 50 | 19-20 | Norman 1999 | 44 | 11 ff. | Verschleierung | Gesichtet | (Schumann) WiseWoman |
| Svr/Fragment 051 01 | 51 | 1-4 | Norman 1999 | 44 | 12 ff. | KomplettPlagiat | Gesichtet | (Schumann) WiseWoman |
| Svr/Fragment 051 07 | 51 | 7-9, 13-19 | Raman 1998 | online | 0 | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 051 21 | 51 | 21-28 | Peat Webber 1997 | online | 0 | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 052 01 | 52 | 1 ff. (completely) | Peat Webber 1997 | online | 0 | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 053 01 | 53 | 1 ff. (completely) | Peat Webber 1997 | online | 0 | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 054 01 | 54 | 1-4 | Peat Webber 1997 | online | 0 | BauernOpfer | Gesichtet | (Schumann) SleepyHollow02 |
| Svr/Fragment 054 06 | 54 | 6-11, 24-30 | Bryan 1998 | online | 0 | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 054 12 | 54 | 12-23 | Walsh Nelson 1998 | online | 0 | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 055 01 | 55 | 1-4 | Erdmann Studer 1999 | online | 0 | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 055 04 | 55 | 4-10 | Heflin 2000 | online | 0 | Verschleierung | Gesichtet | (Schumann) WiseWoman |
| Svr/Fragment 055 22 | 55 | 22-28 | Webber 1998 | 38, 39 | 38: right col., last paragraph; 39: center col., 8 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 055 29 | 55 | 29-31 | XML EDI Group 2001 | online | 0 | KomplettPlagiat | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 056 02 | 56 | 2-26 | Norman 1999 | 45 | 6 ff. | KomplettPlagiat | Gesichtet | (Schumann) WiseWoman |
| Svr/Fragment 056 28 | 56 | 28-30 | Edwards 1999 | online | 0 | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 057 01 | 57 | 1-13, 15-32 | Edwards 1999 | online | 0 | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 058 05 | 58 | 5-11, 18-31 | Webber 1998 | 39 | left col. 1 ff.; right col. 14 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 059 01 | 59 | 1-4 | Webber 1998 | 39 | left col. last line, center col. 1 ff. | BauernOpfer | Gesichtet | (Schumann) Klgn |
| Svr/Fragment 059 08 | 59 | 8-13 | Ricciuti Wong 1999 | online | 0 | KomplettPlagiat | Gesichtet | (Schumann) SleepyHollow02 |
| Svr/Fragment 059 14 | 59 | 14-18 | Dumbill 2001 | online | 0 | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 059 19 | 59 | 19-31 | Johnson 1999 | 77, 81 | 77: 3rd col., 11 ff.; 81: left col., 50 ff., 2nd col., 5 ff. | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 060 02 | 60 | 2-6 | Johnson 1999 | 80 | third col. 5 ff.; right col. 6 f. | Verschleierung | Gesichtet | (Klgn) Schumann |
| Svr/Fragment 060 07 | 60 | 7-19, 27-32 | Norman 1999 | 44, 47, 48 | 44: 7 ff.; 47: 2 ff.; 48: last paragraph | KomplettPlagiat | Gesichtet | (Schumann) WiseWoman |
| Svr/Fragment 060 22 | 60 | 22-25 | Dumbill 2001 | online | 0 | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 061 01 | 61 | 1 ff. (completely) | Norman 1999 | 45, 46 | 45: 38 ff.; 46: 1 ff. | Verschleierung | Gesichtet | (Schumann) SleepyHollow02 |
| Svr/Fragment 062 01 | 62 | 1 ff. (completely) | Norman 1999 | 46 | 3 ff. | KomplettPlagiat | Gesichtet | (Schumann) SleepyHollow02 |
| Svr/Fragment 063 01 | 63 | 1 ff. (completely) | Norman 1999 | 46, 47, 48 | 46: 18 ff.; 47: 28 ff.; 48: 1 ff., 8 ff., 14 f. | Verschleierung | Gesichtet | (Schumann) SleepyHollow02 |
| Svr/Fragment 064 01 | 64 | 1-7 | Norman 1999 | 48 | 15 ff. | Verschleierung | Gesichtet | (Schumann) SleepyHollow02 |
| Svr/Fragment 064 09 | 64 | 9-16 | Carroll 2000 | online | 0 | KomplettPlagiat | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 064 17 | 64 | 17-19 | Balogh 1999 | 53 | 21 ff. | KomplettPlagiat | Gesichtet | (Schumann) SleepyHollow02 |
| Svr/Fragment 065 01 | 65 | 1-5 | Balogh 1999 | 53 | 22 ff. | KomplettPlagiat | Gesichtet | (Schumann) SleepyHollow02 |
| Svr/Fragment 065 06 | 65 | 6-12 | Weitzel et al 2000 | 1 | left col., abstract | KomplettPlagiat | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 066 02 | 66 | 2-5 | Bakos 1991 | online | 0 | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 066 17 | 66 | 17-20, 23-24 | Strassmann 1985 | 80, 81 | 80: 15 ff., 24 ff.; 81: 24 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 067 01 | 67 | 1-3 | Strassmann 1985 | 80 | 22-24 | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 067 28 | 67 | 28-30 | James 1990 | online | 0 | KeineWertung | Unfertig | (Schumann) |
| Svr/Fragment 068 01 | 68 | 1-10 | James 1990 | online | 0 | KeineWertung | Unfertig | (Schumann) |
| Svr/Fragment 069 11 | 69 | 11-23, 101-104 | Copeland Weston 1992 | 25, 26 | 25: 32 ff.; 26: 10 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 070 02 | 70 | 2-8, 10-15, 17-29 | Copeland Weston 1992 | 27, 28, 29, 36 | 27: 12 f., 19 ff.; 28: 2 ff.; 29: last paragraph; 30: 17 f.; 36: 5 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 071 01 | 71 | 1-5 | Copeland Weston 1992 | 28, 29 | 28: last paragraph; 29: 14 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 071 12 | 71 | 12-13, 17-32 | Schuyler 1992 | 17, 18 | 17: right col., 11 ff., 26 ff.; 18: left col., 3 ff. | KomplettPlagiat | Gesichtet | (Klgn) Schumann |
| Svr/Fragment 072 01 | 72 | 1-3 | Schuyler 1992 | 17, 18 | 17: right col., last paragraph; 18: left col., 1 ff. | KomplettPlagiat | Gesichtet | (Klgn) Schumann |
| Svr/Fragment 072 09 | 72 | 9-12 | Economist 1999 | online | 0 | KomplettPlagiat | Gesichtet | (Hindemith) Schumann |
| Svr/Fragment 073 09 | 73 | 9-12 | Strassmann 1985 | 100 | 11 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 074 03 | 74 | 3-6 | Copeland Weston 1992 | 41 | 18 ff. | BauernOpfer | Gesichtet | (Schumann) SleepyHollow02 |
| Svr/Fragment 074 12 | 74 | 12-17 | Trigeorgis 1993 | 205 | left col., 1 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 074 19 | 74 | 19-21 | Coy 1999 | online | 0 | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 075 08 | 75 | 8-12, 101-102 | Copeland Weston 1992 | 241, 251 | 241: 27 ff.; 251: 17 ff. | Verschleierung | Gesichtet | (Klgn) Schumann |
| Svr/Fragment 075 13 | 75 | 13-20 | Brealey Myers 1981 | 439 | 29 ff. | KeineWertung | Unfertig | (Klgn) |
| Svr/Fragment 077 07 | 77 | 7-18 | Trigeorgis 1993 | 205 | right col, last paragraph | KomplettPlagiat | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 077 19 | 77 | 19-23, 25-30 | Brealey Myers 1981 | 440, 442 | 440: 6 ff.; 442: 2 ff. | Verschleierung | Gesichtet | (Schumann) SleepyHollow02 |
| Svr/Fragment 078 02 | 78 | 2-29 | Luehrman 1998 | online | 0 | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 080 13 | 80 | 13-15 | Trigeorgis 1993 | 206 | left col., last paragraph | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 081 10 | 81 | 10-12, 14-22 | Trigeorgis 1993 | 206, 207 | 206: right col., 29 ff.; 207: left col., 7 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 082 10 | 82 | 10-15 | Economist 1999 | online | 0 | Verschleierung | Gesichtet | (Hindemith) Schumann |
| Svr/Fragment 082 16 | 82 | 16-20 | Trigeorgis 1993 | 207 | left col., 25 ff. | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 083 01 | 83 | 1-21, 101 | Economist 1999 | online | 0 | Verschleierung | Gesichtet | (Hindemith) Schumann |
| Svr/Fragment 085 03 | 85 | 3-7 | Dixit Pindyck 1994 | 28 | 24 ff. | BauernOpfer | Gesichtet | (Klgn) Schumann |
| Svr/Fragment 085 23 | 85 | 23-26 | Coy 1999 | online | 0 | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 086 14 | 86 | 14-17, 27-31 | Coy 1999 | 118, 119 | 118: right col. 1 ff., 39 ff.; 119: right col. 1 ff. | Verschleierung | Gesichtet | (SleepyHollow02) (Klgn) Schumann |
| Svr/Fragment 087 07 | 87 | 7-9 | Taudes et al 1999 | 5 | 101 ff. | BauernOpfer | Gesichtet | (Hindemith) Schumann |
| Svr/Fragment 087 20 | 87 | 20-27 | Rogers 1983 | 1, 13 | 1: 16 ff.; 13: 21 ff. | BauernOpfer | Gesichtet | (Schumann) WiseWoman |
| Svr/Fragment 088 18 | 88 | 18-23 | Benaroch Kauffman 2000 | 209 | ricght col., 30 ff. | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 088 28 | 88 | 28-30 | Benaroch Kauffman 2000 | 210 | left col., 25 ff. | BauernOpfer | Gesichtet | (Schumann) WiseWoman |
| Svr/Fragment 089 01 | 89 | 1-10 | Benaroch Kauffman 2000 | 209, 210 | 209: right col., 39 ff.; 210: left col., 3 ff., 15 ff., 32 ff. | BauernOpfer | Gesichtet | (Schumann) WiseWoman |
| Svr/Fragment 090 08 | 90 | 8-11 | Lucas 1999 | 168 | 19 ff. | Verschleierung | Gesichtet | (Schumann) WiseWoman |
| Svr/Fragment 092 05 | 92 | 5-11, 16-18 | Lucas 1999 | 31, 32 | 31: last paragraph; 32: 1 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 093 01 | 93 | 1-3, 8-10, 13-14, (17-26) | Lucas 1999 | 32, 33, 47 | 32: 16 ff., 31 ff.; 33: 1 ff.; 47: 4 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 094 23 | 94 | 23-26 | Strassmann 1985 | 79 | 3 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 095 16 | 95 | 16-21 | Lucas 1999 | 39 | 21 ff., 28 ff. | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 096 11 | 96 | 11-28 | Sassone Schwartz 1986 | 83, 84, 86 | 83: center col. 3 ff., right col. last paragraph; 84: left col., 1 f.; 86: right col., 3 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 097 01 | 97 | 1-11 | Sassone Schwartz 1986 | 84, 86 | 84: right col., 8 ff.; 86: right col., 11 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 097 18 | 97 | 18-24 | Lucas 1999 | 51, 82 | 51: 6 ff.; 82: 19 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 098 10 | 98 | 10-17 | Lucas 1999 | 169 | 1 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 099 08 | 99 | 8-11 | Reinganum 1981 | 395 | 28 ff. | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 099 27 | 99 | 27-29 | Jaakkola 1996 | 65 | 22 ff. | Verschleierung | Gesichtet | (Schumann) WiseWoman |
| Svr/Fragment 100 18 | 100 | 18-23, 24-28 | Rogers 1962? / Rogers 1983? / Arledge 1986? / Rogers/Scott 1997? | - | - | KeineWertung | Unfertig | (Schumann) |
| Svr/Fragment 101 01 | 101 | 1-8 | Bass 1969 | 215, 216, 226 | 215: 8 ff.; 216: 1 f.; 226: 23 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 102 01 | 102 | 1-7 | Mansfield 1961 | 763 | 4 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 102 08 | 102 | 8-19 | Rogers 1983 | 15, 16 | 15: 6 f., 15 ff., 24 f., 33 f.; 16: 3 ff. | BauernOpfer | Gesichtet | (Schumann) WiseWoman |
| Svr/Fragment 102 25 | 102 | 25-30 | Fisher Pry 1971 | 75 | 30 ff. | KeineWertung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 103 18 | 103 | 18-28 | Reinganum 1981 | 395 | 21 ff., 31 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 104 01 | 104 | 1-2 | Reinganum 1981 | 395 | 34 f. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 104 03 | 104 | 3-6, 8-11, 13-18, 21-27 | Quirmbach 1986 | 33, 34 | 33: abstract, 21 ff.; 34: 9 ff., 29 ff. | BauernOpfer | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 106 10 | 106 | 10-16 | Götz 1999 | 679, 680 | 679: 22 ff.; 680: 1 f. | Verschleierung | Gesichtet | (Schumann) WiseWoman |
| Svr/Fragment 109 21 | 109 | 21-30 | Shankar 1999 | 47, 48 | 47: left col., 22 ff.; 48: last paragraph | Verschleierung | Gesichtet | (Klgn) Schumann |
| Svr/Fragment 109 30 | 109 | 30 | Webber 1998 | 38 | 2 ff. | KomplettPlagiat | Gesichtet | (Klgn) Schumann |
| Svr/Fragment 110 02 | 110 | 2-5 | Ritz 1995 | 1 | 20 ff. | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 110 05 | 110 | 5-9 | Murch Johnson 1999 | 73 | 30 ff. | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 110 10 | 110 | 10-14 | Carroll 2000 | online | 0 | KomplettPlagiat | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 110 27 | 110 | 27-32 | Bakos 1991 | online | 0 | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 111 09 | 111 | 9-14 | Benaroch Kauffman 2000 | 209 | right col., 30 ff. | Verschleierung | Gesichtet | (SleepyHollow02) Schumann |
| Svr/Fragment 123 20 | 123 | 20-26 | Walsh 1998 | online | 0 | Verschleierung | Gesichtet | (Hindemith) |
| Svr/Fragment 124 01 | 124 | 1-6 | Walsh 1998 | online | 0 | KomplettPlagiat | Gesichtet | (Hindemith) Schumann |
| Svr/Fragment 128 27 | 128 | 27-31 | Walsh 1998 | online | 0 | KomplettPlagiat | Gesichtet | (Hindemith) Schumann |
| Svr/Fragment 130 24 | 130 | 24-26 | Walsh 1998 | online | 0 | KomplettPlagiat | Gesichtet | (Hindemith) Schumann |
| Svr/Fragment 131 14 | 131 | 14-20, 26-29 | Walsh 1998 | online | 0 | KomplettPlagiat | Gesichtet | (Hindemith) Schumann |
| Svr/Fragment 132 16 | 132 | 16-18 | Walsh 1998 | online | 0 | KomplettPlagiat | Gesichtet | (Hindemith) Schumann |
| Svr/Fragment 133 05 | 133 | 5-7 | Walsh 1998 | online | 0 | KomplettPlagiat | Gesichtet | (Hindemith) Schumann |
| Svr/Fragment 136 25 | 136 | 25-27 | Walsh 1998 | online | 0 | KomplettPlagiat | Gesichtet | (Hindemith) Schumann |
| Svr/Fragment 137 04 | 137 | 4-5, 10-15, 24-28 | Walsh 1998 | online | 0 | KomplettPlagiat | Gesichtet | (Hindemith) Schumann |
| Svr/Fragment 139 24 | 139 | 24-27 | Walsh 1998 | online | 0 | KomplettPlagiat | Gesichtet | (Hindemith) Schumann |
| Svr/Fragment 140 20 | 140 | 20-21 | Walsh 1998 | online | 0 | KomplettPlagiat | Gesichtet | (Hindemith) Schumann |
| Typus | Gesichtet | ZuSichten | Unfertig | Σ |
|---|---|---|---|---|
| ÜP | 0 | 0 | 0 | 0 |
| KP | 50 | 0 | 0 | 50 |
| VS | 79 | 0 | 0 | 79 |
| BO | 74 | 0 | 0 | 74 |
| KW | 3 | 5 | 4 | 12 |
| KeinP | 0 | 0 | 0 | 0 |
| Σ | 206 | 5 | 4 | 215 |
209 Fragmente
| [1.] Svr/Fragment 001 02 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 1, Zeilen: 2-24 |
Quelle: Kobielus 2000 Seite(n): 57, Zeilen: left col., 10 ff. |
|---|---|
| [0. Introduction]
Companies today are trying hard to find a way to link their internal business processes with those of trading partners without plunging themselves into a maze of technical headaches and integration costs. No robust standards have yet emerged to support interoperable, cross-platform e-business. The typical e-business software products today cover topics as customer relationship management (CRM), electronic data interchange (EDI), enterprise application integration and enterprise resource planning (ERP), but the industry is nowhere near delivering anything resembling plug-and-play technical integration at the Business-to-Business (B2B) level. Yet the basics of e-business are quite simple. They revolve around two familiar technologies that companies have known for years: EDI and workflow, where EDI stands for structured document routing between companies, and workflow for structured document routing within each organization. But, EDI and workflow have been separated by their divergent spheres of application. The virtual business is constantly repositioning itself through dynamic alliances with an ever-changing set of trading partners. Therefore, an Internet-based trading community can only be reality where all participants share a common process model, an agreed-upon set of business rules that govern structured transactions. Just as important, all participants will have to implement a common B2B interoperability framework that allows them to enter easily into new trading relationships without the need for costly, time-consuming, (bilateral) or multilateral coordination of legal agreements and technical interfaces, as is the case with classic EDI. |
Enterprise customers are scratching their heads trying to figure how to link their internal business processes with those of trading partners and not plunge themselves into a vortex of technical headaches and integration costs. No robust standards have yet emerged to support interoperable, cross-platform e-business. The industry is nowhere near delivering anything resembling plug-and-play technical integration at the B2B level.
E-business is also a conceptual mess. E-business software vendors are trying hard to help customers sort through all the integration issues, but vendors are still groping for a conceptual handle on it all. The typical e-business software vendor’s product roadmap invokes such familiar, but vague, topics as customer relationship management, electronic data interchange, enterprise application integration and enterprise resource planning (ERP). Yet the basics of e-business are quite simple. They revolve around two familiar technologies that companies have implemented for years: EDI and workflow. [...] EDI and workflow have been separated by their divergent spheres of application: EDI for structured document routing between companies; workflow for structured routing within each organization. [...] The virtual business is constantly repositioning itself through dynamic alliances with an ever-changing set of trading partners. An Internet-based trading community can thrive only where all participants share a common process model — an agreed-upon set of business rules that govern structured transactions. Just as important, all participants will have to implement a common B2B interoperability framework that allows them to enter easily into new trading relationships without the need for costly, time-consuming, multilateral coordination of legal agreements and technical interfaces. |
No source is given. |
| [2.] Svr/Fragment 001 25 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 1, Zeilen: 25-29 |
Quelle: Shankar 1999 Seite(n): 47, Zeilen: first paragraph |
|---|---|
| Traditionally, EDI has been effective for communicating transactions between companies, but only large enterprises performing a high volume of transactions have realized significant benefits using it. Now the XML standard promises an open standard for cost-effective B2B Internet commerce that will enable midsize and smaller companies to use EDI. | TRADITIONALLY, electronic data interchange (EDI) has been effective for communicating transactions between companies, but only large enterprises performing a high volume of transactions have realized significant benefits using it. Now the Extensible Markup Language (XML) standard promises an open standard for secure, cost-effective business-to-business Internet commerce that will bring midsize and smaller companies into the fold. |
No source is given. |
| [3.] Svr/Fragment 002 02 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 2, Zeilen: 2-3 |
Quelle: Shankar 1999 Seite(n): 47, Zeilen: - |
|---|---|
| Nevertheless, XML's pledge of better data portability among trading partners is the wave of the future. | Nevertheless, XML’s pledge of better data portability among trading partners is the wave of the future. |
This fragment continues from the previous page. No source is given. |
| [4.] Svr/Fragment 002 05 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 2, Zeilen: 5-8 |
Quelle: Bakos 1997 Seite(n): 1, Zeilen: 11 ff. |
|---|---|
| The costs for participating in an electronic marketplace are lowered by emerging public and private standards for access and information exchange over the Internet, such as the HTTP protocol, technologies for secure information exchange like SSL and standards for electronic commerce. | This trend is further amplified as the cost of participating in an electronic marketplace is lowered by emerging public and private standards for access and information exchange over the Internet, such as the hypertext markup language (HTTP) protocols, the secure sockets layer (SSL) architecture for secure information exchange, and CommerceNet’s (www.commerce.net) suite of standards for electronic commerce. |
The source is not given. |
| [5.] Svr/Fragment 002 08 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 2, Zeilen: 8-10 |
Quelle: Bailey Bakos 1997 Seite(n): online, Zeilen: 0 |
|---|---|
| While EDI and the Internet have very different origins, they are the most ubiquitous infrastructures for electronic markets, and recently the boundary between them seem [sic] to be blurring. | While EDI and the Internet have very different origins, they are the most ubiquitous infrastructures for electronic markets, and recently the boundary between them seems to be blurring. |
No source is given. |
| [6.] Svr/Fragment 002 11 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 2, Zeilen: 11-12, 13-15 |
Quelle: Norman 1999 Seite(n): 44, Zeilen: 15 ff. |
|---|---|
| The idea behind EDI is a good one, unfortunately it has not worked out so well in reality. [After almost 30 years, only 2% - 5% of the companies today in Europe and the US make use of EDI (Segev et al. 1997).] One of the major problems with the current implementations of EDI is that they often require a unique solution for each pair of trading partners, making EDI costly and time-consuming to implement.
[Segev, A., Porra, J., & Roldan, M. 1997, Internet-Based EDI Strategy, working paper 97-WP-1021, [Online]. Available: http://haas.berkeley.edu/~citm/wp-1021.pdf |
The idea behind EDI is a good one, unfortunately it hasn’t worked out so well in reality. One of the major problems with the current implementations of EDI is that they often require a unique solution for each pair of trading partners, making EDI costly and time-consuming to implement. |
The actual source is not given. Segev et al. (1997) does not contain that content. |
| [7.] Svr/Fragment 002 22 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 2, Zeilen: 22-25 |
Quelle: Webber 1998 Seite(n): 38, Zeilen: right col., 9 ff. |
|---|---|
| The vision of XML/EDI is to allow organizations to deploy smarter, cheaper and more maintainable systems to a global audience. Thus, XML/EDI shall be equally accessible to small business as to large corporations. | The vision for XML/EDI is to allow organizations to deploy smarter, cheaper and more maintainable systems to a global audience. XML/EDI is thus equally accessible to small business as to large corporations. |
No source is given. |
| [8.] Svr/Fragment 003 04 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 3, Zeilen: 4-8, 21-23, 28-29 |
Quelle: Ritz 1995 Seite(n): 1, 6, 7, Zeilen: 1: 28 ff.; 6: last 2 lines; 7: 7 f. |
|---|---|
| 0.2. Motivation for Research
Companies that trade electronically with their business partners are said to enjoy strategic benefits such as a higher responsiveness to customers resulting from the higher speed of internal processing, and an optimization of inter-organizational business processes through electronic integration with customers and suppliers. [...] 0.3. Research Objectives and Target Audience The overall objective of the research is to contribute to the theoretical understanding of the XML standard and its applications, in particular XML/EDI, [as well as to develop a framework for the assessment of the value of an XML/EDI investment project.] [...] The target audiences of the thesis are academic scholars as well as business practitioners. |
[page 1]
Moreover, companies that trade electronically with their business partners are said to enjoy strategic benefits such as a higher responsiveness to customers, resulting from the higher speed of internal processing, and an optimization of interorganizational business processes through electronic integration with customers and suppliers (e.g. Kimberley 1991). [page 6] 0.3 Research objectives and target audience Against that backdrop, the overall objective of the present study is to contribute to the theoretical and practical understanding of EDI network start-up by: [...] [page 7] The target audience of the thesis are academic scholars as well as business practitioners. Kimberley, P. (1991) Electronic data interchange. New York, etc.: Mc Graw Hill, 1991. |
No source is given. |
| [9.] Svr/Fragment 005 25 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 5, Zeilen: 25-27 |
Quelle: Bakos 1998 Seite(n): 35, Zeilen: 15 ff. |
|---|---|
| Markets have the economic function of facilitating the exchange of information, goods, services and payments. Thus they create an economic value for buyers, sellers, market intermediaries and society as a whole. | Markets play a central role in the economy, facilitating the exchange of information, goods, services, and payments. In the process, they create economic value for buyers, sellers, market intermediaries, and for society at large. |
No source is given. |
| [10.] Svr/Fragment 006 01 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 6, Zeilen: 1-9 |
Quelle: Schmid 1993 Seite(n): 3, Zeilen: 3: left col., 4 ff.; center col., 17 ff.; right col., 5 ff., 22 ff.; |
|---|---|
| [Traditional market theory defines a market as a place of exchange, where aggregate-demand meets] aggregate supply, by allocating resources, skills and products. Coordination is the key factor for optimizing allocation and to yield maximum economic welfare.
Schmidt [sic] (1993) defines 3 phases that are substantial for any process of market coordination, thus also for electronic markets: (1) Information Phase: information on available products and services, their specifications, and delivery terms. (2) Agreement Phase: after evaluating all information, contacting potential transaction partners and negotiation of terms and conditions, as well as establishment of a legal basis. (3) Settlement Phase: physical exchange of goods and/or services and flow of financial transactions and information. Schmidt [sic], B. 1993, "Electronic Markets," Electronic Markets, No.9-10, pp. 3-4 (October 1993). |
[left col.]
According to traditional market theory, markets are defined as economic places of exchange, where aggregate demand meets aggregate supply. They serve to allocate resources, skills and products. Coordination is the key factor to optimize allocation and to yield maximum economic welfare. [...] Traditional market theory, however, does not reflect the real world: [...] [center col.] Three phases, which are substantial for any process of coordination, can be distinguished: Phase 1: Information gathering. On the input side, information on available products and/or services, their specifications, suppliers and delivery terms are required. [right col.] As soon as all information has been evaluated, we can proceed to contact potential transaction partners. Terms and conditions have to be fixed (terms of payment and delivery, warranties, additional service etc.). [...] Phase 3: Settlement. [...] The physical exchange of goods is accompanied by flows of financial transactions and information. |
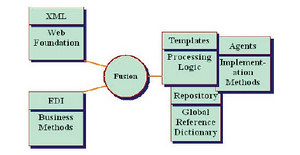
The source is given, although the author's name is misspelled here and in the reference list. It is not made clear how close the text is to the original. Figure 1, which immediately follows this text, is attributed to Schmidt [sic] 1993, however the figure in Schmid only vaguely resembles the one in the dissertation. |
| [11.] Svr/Fragment 007 01 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 7, Zeilen: 1-2 |
Quelle: Schmid 1993 Seite(n): 3, Zeilen: right col., 51 ff. |
|---|---|
| [ ... Schmidt 1993 defines .... In and [sic] broader sense he defines Electronic Markets as] information systems supporting one or more phases and functions of coordination within market systems.
Schmidt, B. 1993, "Electronic Markets," Electronic Markets, No.9-10, pp. 3-4 (October 1993) |
EMs in the broader sense may be understood as information systems supporting one or more phases and functions of coordination within market systems. |
The source is given on the previous page, but misspelled as Schmidt. However, the definition is not set off with quotation marks. |
| [12.] Svr/Fragment 007 03 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 7, Zeilen: 3-8, 10-13, 101-103 |
Quelle: Zimmermann 1998 Seite(n): 379, Zeilen: 29 ff. |
|---|---|
| Zimmermann (1998) splits the three basic phases of a market transaction, in four different views: The community view, process view, transaction view, and infrastructure view (see Figure 2).
[Figure] Figure 2: The Business Media Framework (Zimmermann 1998) The community view defines the relevant business community1 and its underlying, basic business model. Electronic Markets constitute the space for an exchange of goods within the community. [...] The process view defines the inter-organizational business procedures and processes along the value chain of the respective business community. These processes enable the business community to realize their defined business models. 1 Zimmermann (1998) defines Business Communities as the quantity of agents (e.g. people, organizations, computers), whose rights and duties of agents are defined through the assignment of roles. Zimmermann, H.D. 1998, Business Media: A new Approach to Overcome Current Problems of Electronic Commerce. In: Proceedings of the forth Americas Conference on Information Systems (AIS´98), S.378-380. |
The basic model distinguishes on the vertical axis the three basic phases of a transaction: the information, agreement and settlement phase. On the horizontal axis we define four different views of Business Media: The community, process, transaction, and infrastructure view (see Figure 1). This basic setting is derived from the model described in [10].
The community view defines the relevant business community and its underlying, basic business model. Business communities are understood as a quantity of agents (e.g., people, organizations, computers). Rights and duties of agents are defined through the assignment of roles. [...] Media constitute the space for an exchange of goods within the community. [...] The goal of the process view is to define the inter-organizational business procedures and processes along the value chain of the respective business community. These processes enable the business community to realize their defined business models. [10] Schmid, B.F.; Lindemann, M.A.: Elements of a Reference Model for Electronic Markets, Proceedings of the 31. Annual Hawaii International Conference on Systems Science (HICSS), Vol. IV, pp. 193-201, Hawaii, January 1998 |
The source is given twice, but it is not made clear that the text is so extensively similar. There are no quotation marks used. |
| [13.] Svr/Fragment 008 01 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 8, Zeilen: 1-12 |
Quelle: Zimmermann 1998 Seite(n): 380, Zeilen: 4 ff. |
|---|---|
| At the transaction view level generic services have to be defined that enable the realization of the defined business processes. The offered services support the different functions in the three distinguished phases. Examples are intelligent electronic product catalogs including search functions, services supporting the negotiation of contracts, logistic and payment systems to settle the transaction. The overall goal is to enable a continuous settlement of business transactions without incompatible interfaces and to provide an infrastructure of services that is available to different business communities.
The infrastructure view defines the necessary network services and other technical components to realize the settlement of the transaction from a technical point of view. Examples are message handling-, EDI Networks, and clearing center services. |
At the transaction view level generic services have to be defined that enable the realization of the defined business processes. The offered services shall support the different functions in the three distinguished phases. Examples are intelligent electronic product catalogs including search functions, services supporting the negotiation of contracts, logistic and payment systems to settle the transaction. [...] The overall goal is to enable a continuous settlement of business transactions without incompatible interfaces and to provide an infrastructure of services that is available to different business communities. The infrastructure view defines the necessary network services and other technical components to realize the settlement of the transaction from a technical point of view. Examples are message handling-, EDI-, and clearing center services. |
No source is given. |
| [14.] Svr/Fragment 008 14 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 8, Zeilen: 14-21, 24-28 |
Quelle: Bakos 1998 Seite(n): 37, 39, 40, 42, Zeilen: 37: left col., 13; 39: right col., 17 ff.; 40: left col., 39 ff.; 42: left col., 26 ff. |
|---|---|
| [1.2. How do Electronic Markets affect traditional Market Structures?]
The Internet affects markets by changing the structure of product offerings, as for example: (i) Aggregation and disaggregation of information based product components. With electronic markets in place the role of intermediaries will be reduced or even eliminated, leading to disintermediation. It will become easier to match buyers and sellers, reducing the costs or market transactions. (ii) The costs of logistics are decreased when electronic marketplaces improve information sharing between buyers and sellers by promoting quick, just-in-time deliveries and reduce inventories. (iii) Increased personalization of product offerings. [1.2.1 Information Phase'] [...] Lower search costs enable new markets to emerge, as for example creating a market for second hand cameras where otherwise the search costs would be too high to enable potential buyers and sellers to find each other on a conventional market (Bakos 1998). Bakos, Y. 1998, "The Emerging Role of Electronic Marketplaces on the Internet," Communications of the ACM, vol. 41, pp. 35-46. |
How the Internet Affects Markets
[...] Two major emerging trends distinguish products in electronic marketplaces from their traditional counterparts: increased personalization and customization of product offerings, and the aggregation and disaggregation of information-based product components to match customer needs and to support new pricing strategies. [page 39] The lower search costs enable new markets to emerge. For example, low buyer search costs and global reach allowed Onsale.com (www.onsale.com) to create markets in goods like secondhand cameras; otherwise the search costs would be too high to enable potential buyers and sellers to find each other in a conventional market. [page 40] Electronic marketplaces improve information sharing between buyers and sellers, helping lower the cost of logistics and promoting quick, just-in-time deliveries and reduced inventories. [page 42] It has been argued that as friction-free electronic marketplaces lower the cost of market transactions, it will become easy to match directly buyers and sellers, and as a result, the role of intermediaries may be reduced or even eliminated leading to “disintermediation” (see [9, 10]). 9. Gates, W. The Road Ahead. Penguin Books, New York, 1995. 10. Gellman, R. Disintermediation and the Internet. Government Information Q. 13, 1 (1996), 1–8. |
Source is given but it does not become clear to what extent text is copied. |
| [15.] Svr/Fragment 009 01 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 9, Zeilen: 1-5, 9-16, 21-24 |
Quelle: Bakos 1998 Seite(n): 39, 40, 41, Zeilen: 39: right col. last paragraph; 40: left col., 1 ff., right col., 4 ff.; 41: left col., 9 ff. |
|---|---|
| The dynamics of friction free markets will change product-pricing strategies of companies that had previously depended on geography or customer ignorance. As geography becomes less Important, new source of product differentiation such as customized features, service or innovation will become more important (Bakos 1998).
[1.2.2 Agreement Phase New types of price agreements are possible in electronic markets with auctions, or bulk buying, where customers can obtain higher bargaining power.] The ability to customize products, combined with the ability of sellers to access substantial information about prospective buyers, such as demographics, preferences and past shopping behavior, is greatly improving seller’ ability to price discriminate. Price discrimination is a powerful tool that allows sellers to increase their profits, and reduces consumer surplus enjoyed by buyers. On the other hand, price discrimination enables sellers to service buyers that would otherwise be priced out of the market, an outcome that increases economic efficiency (Bakos 1998). [1.2.3 Settlement Phase With digital information goods such as news, music or software, the Internet dramatically reduces the marginal cost of distribution of these goods (Bakos 1998).] Furthermore, electronic payment systems have the potential of lowering transaction costs of commercial exchanges, and micro payment systems will lower the costs of small transactions, enabling new pricing strategies such as metering of software use. Bakos, Y. 1998, "The Emerging Role of Electronic Marketplaces on the Internet," Communications of the ACM, vol. 41, pp. 35-46. |
[page 41]
The dynamics of friction-free markets are not attractive for sellers that had previously depended on geography or customer ignorance to insulate them from the low-cost sellers in the market. As geography becomes less important, new sources of product differentiation, such as customized features or service or innovation, will become more important, at least for those sellers who don’t have the lowest cost of production. [page 39] The ability to customize products, combined with the ability of sellers to access substantial information about prospective buyers, such as demographics, preferences and past shopping behavior, is greatly improving sellers’ ability to price discriminate—that [page 40] is, to charge different prices for different buyers. Price discrimination is a powerful tool that allows sellers to increase their profits, and reduces the consumer surplus enjoyed by buyers. On the other hand, price discrimination enables sellers to service buyers who would otherwise be priced out of the market, an outcome that increases economic efficiency. [...] Electronic payment systems will further lower transaction costs in Internet marketplaces, and micropayment systems will lower the cost of small transactions, enabling new pricing strategies such as the metering of software use. |
The source is given three times, but there are no quotation marks despite the closeness of the text to the source. |
| [16.] Svr/Fragment 011 04 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 11, Zeilen: 4-10 |
Quelle: Enigma 1999 Seite(n): online, Zeilen: 0 |
|---|---|
| Prior to the emerging of the Internet, it was unusual in the word [sic] of computing to hear the word page used to describe elements of data. But HTML web pages have amazing similarities with paper in their role of information publishing. Both HTML and paper pages:
- Are optimized for visual clarity. - Focus on ultimate usability (but not on reusability). - Contain no contextual information. |
Prior to the web-quake, it wasn't very often in the world of computing to hear the word "page" used to describe elements of data. [...] That is because HTML and paper have like qualities and play similar roles in the information publishing life-cycle. Namely, they both:
|
No source is given. |
| [17.] Svr/Fragment 011 12 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 11, Zeilen: 12-31 |
Quelle: Spider's Apprentice 2000 Seite(n): online, Zeilen: 0 |
|---|---|
| Search engines use software robots to survey the Web and build their databases by retrieving and indexing HTML documents. When a query is entered at a search engine website, input is checked against the search engine's keyword indices. The best matches are then returned as hits. There are two primary methods of text searching: Keyword Searching and Concept-based Searching.
(1) Keyword Searching is the most common form of text search on the Web. Most search engines do their text query and retrieval using keywords or meta-tags. Essentially, this means that search engines pull out and index words that are believed to be significant. Words that are mentioned towards the top of a document and words that are repeated several times throughout the document are more likely to be deemed important. Most search engines index every word on every page. Others index only part of the document, such as the title, headings, subheadings, hyperlinks to other sites, and the first 20 lines of text. Some of the search engines discriminate upper case from lower case; others store all words without reference to capitalization. There are many problems with keyword searching, i.e.: Keyword searches cannot distinguish between words that are spelled the same way but mean something different. This often results in hits that are completely irrelevant to a query. Search engines also cannot return hits on keywords that mean the same, but are not actually entered in your query. |
Search engines use software robots to survey the Web and build their databases. Web documents are retrieved and indexed. When you enter a query at a search engine website, your input is checked against the search engine's keyword indices. The best matches are then returned to you as hits.
There are two primary methods of text searching--keyword and concept. Keyword Searching This is the most common form of text search on the Web. Most search engines do their text query and retrieval using keywords. [...] Essentially, this means that search engines pull out and index words that are believed to be significant. Words that are mentioned towards the top of a document and words that are repeated several times throughout the document are more likely to be deemed important. Some sites index every word on every page. Others index only part of the document. For example, Lycos indexes the title, headings, subheadings and the hyperlinks to other sites, along with the first 20 lines of text and the 100 words that occur most often. [...] Some of the search engines discriminate upper case from lower case; others store all words without reference to capitalization. Keyword searches have a tough time distinguishing between words that are spelled the same way, but mean something different (i.e. hard cider, a hard stone, a hard exam, and the hard drive on your computer). This often results in hits that are completely irrelevant to your query. [...] Search engines also cannot return hits on keywords that mean the same, but are not actually entered in your query. |
No source is given. |
| [18.] Svr/Fragment 012 01 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 12, Zeilen: 1-10 |
Quelle: Spider's Apprentice 2000 Seite(n): online, Zeilen: 0 |
|---|---|
| (2) Concept-based searching, unlike keyword search systems, tries to determine what a user means. In the best circumstances, a concept-based search returns hits on documents on a specific topic, even if the words in the document do not precisely match the words a user enters into the query. This is also known as clustering, which essentially means that words are examined in relation to other words found nearby. There are various methods of building clustering systems, some of which are highly complex, relying on sophisticated linguistic and artificial intelligence methods. Concept-based indexing is a good idea, but it is far from perfect. The results are best when one enters a lot of words, all of which roughly refer to the concept one seeking information about. | Concept-based searching
Unlike keyword search systems, concept-based search systems try to determine what you mean, not just what you say. In the best circumstances, a concept-based search returns hits on documents that are "about" the subject/theme you're exploring, even if the words in the document don't precisely match the words you enter into the query. [...] This is also known as clustering -- which essentially means that words are examined in relation to other words found nearby. How does it work? There are various methods of building clustering systems, some of which are highly complex, relying on sophisticated linguistic and artificial intelligence theory that we won't even attempt to go into here. [...] Concept-based indexing is a good idea, but it's far from perfect. The results are best when you enter a lot of words, all of which roughly refer to the concept you're seeking information about. |
No source is given. |
| [19.] Svr/Fragment 013 02 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 13, Zeilen: 2-9, 11-14 |
Quelle: Lee 1998 Seite(n): 3, Zeilen: left col., 34 ff.; right col., 4 ff., 38 ff. |
|---|---|
| Electronic contracting may be viewed from the perspective of its openness to new contracting relationships: (i) open electronic contracting, and (ii) closed electronic contracting (Lee 1998b).
Classic EDI uses closed electronic contracting to advance contracting among parties that already have a trading relationship established. The focus of such applications is to make customer-vendor trading more efficient. The more challenging case for electronic contracting is open electronic contracting, which allows the formation of contracts among parties with no prior trading relationships. [Lee (1998b) points out that the type of electronic contracting (closed to open) is actually a continuum, allowing for intermediate cases.] A central issue for open electronic contracting is in representing and negotiating ways of doing business among parties. The difficulty with classic EDI is that it does not allow flexible adaptation and customization to meet the needs of a particular situation. Lee, R. M. 1998b, “Towards Open Electronic Contracting”, Electronic Markets, vol. 8, No. 3, p. 3 - 8. |
Electronic contracting may be viewed from the perspective of its ‚openness‘ to new contracting relationships. Closed electronic contracting is the use EDI (etc) to expedite contracting among parties that already have a trading relationship established. The focus of such applications is to make customer-vendor trading more efficient. The more challenging case is open electronic contracting, which allows the formation of contracts among parties with no prior trading relationships, so called ‚arm‘s length transactions.
[...] A central issue for open electronic contracting is in representing and negotiating the ways of doing business among the parties. [...] However, a difficulty of this approach is that these scenarios are fixed in their structure, and do not allow flexible adaptation and customization to meet the needs of a particular situation. |
Source is given twice. Most of the text is copied literally. Quotation marks would have been apropriate as the longest portion of text copied literally is 25 words long. |
| [20.] Svr/Fragment 013 15 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 13, Zeilen: 15-22 |
Quelle: Lee 1998a Seite(n): 19, 20, Zeilen: 19: right col, 41 ff.; 20: center col., 15 ff.; right col.: 1 ff. |
|---|---|
| Another way to negotiate is via Email. Electronic negotiation through Email can be an information rich medium through which people can negotiate not just only price but also other aspects such as subscription terms. Electronic negotiation can be further automated with Intelligent Negotiation Support Systems, which understand Email messages and negotiate with the customer using case based reasoning. The main problem of email negotiation is the integrity of a contract due to the lack of trust between two relevant parties, and the lack of structure of the negotiation process (Lee 1998a). | [page 20]
Electronic negotiation through e-mail proves that e-mail can be an information rich medium through which people can negotiate not just price but other complex items such as subscription terms. Electronic negotiation can be automated by implementing the Intelligent NSS which understands e-mail messages and negotiate with the customer using case-based reasoning. [page 19] The core of the problem is the lack of trust between two relevant parties. |
Source is given. Quotation marks would have been approriate as the longest portion of text copied literally is 13 words long. |
| [21.] Svr/Fragment 013 29 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 13, Zeilen: 29-31 |
Quelle: Weitzel et al 1999 Seite(n): online, Zeilen: 0 |
|---|---|
| For more than 25 years, companies have been using EDI to transmit structured business documents like orders or invoices electronically. As opposed to paperbased communication, EDI is designed to make communication between different [systems possible without media discontinuities.] | For more than 20 years, companies have been using Electronic Data Interchange (EDI) to transmit structured business documents like orders or invoices electronically. As opposed to paper-based communication, EDI is designed to make communication between different systems possible without media discontinuities. |
Source is given on p. 14 as Weitzel et al. 1999. No quotation marks. Weitzel et al. 1999 might refer to Weitzel, T. & Buxmann, P. 1999, A communication architecture for the digital economy: 21st century EDI or to Weitzel, T., Buxmann, P., Kronenberg, R., & Ladner, F. 1999b, XML/EDI: The (r)evolution of EDI, Institute of Information Systems, Working Paper 99-10, [Online]. Avaliable: [sic] http://www.wiwi.uni-frankfurt.de/~tweitzel/XMLEDI.doc Accessed: October 29 1999 As the text is copied literally without quotation marks it is a pawn sacrifice either way. |
| [22.] Svr/Fragment 014 03 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 14, Zeilen: 3-11 |
Quelle: Weitzel et al 1999 Seite(n): online, Zeilen: 0 |
|---|---|
| But although there is an undoubtedly large savings potential, the use of EDI is by far not as widespread as one could expect. The main reason is that especially small and medium-sized enterprises try to avoid the considerable setup- and operating costs of traditional EDI solutions and that the standards are not flexible enough. In addition, the variety of different industryspecific and national EDI standards makes it difficult for businesses to decide which standard to use. Therefore, the use of EDI is mainly reserved for large companies, and, as empirical analysis shows, one of the main reasons for SMEs to introduce EDI is usually pressure from larger business partners (Weitzel et al. 1999).
Weitzel, T. & Buxmann, P. 1999, A communication architecture for the digital economy: 21st century EDI Weitzel, T., Buxmann, P., Ladner, F., König, W. 1999a, XML: Konzept und Anwendungen der Extensible Markup Language, SFB 403 FB-99-20, [Online]. Weitzel, T., Buxmann, P., Kronenberg, R., & Ladner, F. 1999b, XML/EDI: The (r)evolution of EDI, Institute of Information Systems, Working Paper 99-10, [Online]. |
But although there undoubtedly is large savings potential, the use of EDI is by far not as widespread as one could expect. [...] The main reason is that especially small and medium-sized enterprises (SMEs) try to avoid the considerable setup- and operating costs of traditional EDI solutions. In addition, the variety of different industry-specific and national EDI standards makes it difficult for businesses to decide which standard to use. Therefore, the use of EDI is mainly reserved for large companies, and a current empirical analysis shows that one of the main reasons for the introduction of EDI is usually pressure from larger business partners, which is often called "gun-to-the-head-EDI" [Westarp/Weitzel/Buxmann/König 1999].
Westarp, F. v./Weitzel, T./Buxmann, P./König, W. (1999): The Status Quo and the Future of EDI, forthcoming in: Proceedings of the 1999 European Conference on Information Systems (ECIS’99), http://caladan.wiwi.uni-frankfurt.de/IWI/projectb3/deu/publikat/edi/ |
The source is given, but nothing is marked as a direct quotation. Weitzel et al. 1999 might refer to Weitzel, T. & Buxmann, P. 1999, A communication architecture for the digital economy: 21st century EDI or to Weitzel, T., Buxmann, P., Kronenberg, R., & Ladner, F. 1999b, XML/EDI: The (r)evolution of EDI, Institute of Information Systems, Working Paper 99-10, [Online]. Avaliable: [sic] http://www.wiwi.uni-frankfurt.de/~tweitzel/XMLEDI.doc Accessed: October 29 1999 As the text is copied literally without quotation marks, no matter which source is meant, this is classified as a pawn sacrifice. |
| [23.] Svr/Fragment 014 22 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 14, Zeilen: 22-24 |
Quelle: Berners-Lee et al 2001 Seite(n): 42, Zeilen: right col., 14 ff. |
|---|---|
| Today, many automated Web-based services already exist without semantics, but other programs such as agents have no way to locate one that will perform a specific function. | Many automated Web-based services already exist without semantics, but other programs such as agents have no way to locate one that will perform a specific function. |
The source is not given. |
| [24.] Svr/Fragment 015 01 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 15, Zeilen: 1-5 |
Quelle: Murch Johnson 1999 Seite(n): 71, 72, Zeilen: 71: 7 ff.; 72: 25 ff. |
|---|---|
| For this reason, XML (Extensible Markup Language) was developed by the XML working group (known as the SGML1 Editorial Review Board) formed under the auspices of the World Wide Web Consortium (W3C) in 1996. XML is a highly functional subset of SGML. The purpose of XML is to specify an SGML subset that works very well for delivering SGML information over the Web. | [page 72]
XML is the Extensible Markup Language subset of ISO's Standard Generalized Markup Language (SGML) developed by the World Wide Web Consortium (W3C) "SGML on the Web" working party during the latter half of 1996 and early 1997. The formal recommendation was submitted for approval by W3C members on December 8,1997.
XML is being designed by a Working Group of the World Wide Web Consortium (W3C), an organization whose charter is to establish specifications for Web technologies to ensure the highest possible degree of utility and interoperability. The XML Working Group consists of about fourteen companies and organizations with a strong interest in either providing or utilizing XML tools. [page 71] XML, or Extensible Markup Language, is a highly functional subset of SGML. The purpose of XML is to specify an SGML subset that works very well for delivering SGML information over the Web. |
No source is given. |
| [25.] Svr/Fragment 015 101 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 15, Zeilen: 101-102, 106-112 |
Quelle: Bartlett 1997 Seite(n): online, Zeilen: 0 |
|---|---|
|
1 In 1986 the Standard Generalized Markup Language (SGML) became an international standard for defining descriptions of the structure and content of different types of electronic documents. [...] SGML has withstood the test of time. Its popularity is rapidly increasing among organizations with large amounts of document data to create, manage, and distribute as in the Defense, Aerospace, Semiconductor and Publishing industries. However, various barriers exist to delivering SGML over the Web. These barriers include the lack of widely supported style sheets, complex and unstable software because of SGML’s broad and powerful options, and obstacles to interchange of SGML data because of varying levels of SGML compliance among SGML software packages. |
Abstract: "In 1986, the Standard Generalized Markup Language (SGML) became an international standard for the format of text and documents. SGML has withstood the test of time. Its popularity is rapidly increasing among organizations with large amounts of document data to create, manage, and distribute. However, various barriers exist to delivering SGML over the Web. These barriers include the lack of widely supported stylesheets, complex software because of SGML's broad and powerful options, and obstacles to interchange of SGML data because of varying levels of SGML compliance among SGML software products. |
The source is not given. |
| [26.] Svr/Fragment 015 12 |
| KeineWertung |
|---|
| Untersuchte Arbeit: Seite: 15, Zeilen: 12-13 |
Quelle: Arbortext 1999 Seite(n): online, Zeilen: 0 |
|---|---|
| But XML also lacks some important capabilities of SGML that primarily affect document creation, not document delivery. That is so as XML was not designed to replace SGML in every respect. | XML also lacks some important capabilities of SGML that primarily affect document creation, not document delivery. That's because XML was not designed to replace SGML in every respect. |
No source is given. This sentence is also found in Svr's XML Tutorial' [1], as is the rest of page 15. |
| [27.] Svr/Fragment 016 02 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 16, Zeilen: 2-10, 15-17, 20-23, 25-32 |
Quelle: Berners-Lee et al 2001 Seite(n): 36, Zeilen: 36: right col., 15 ff.; 37: left col., 1 ff. center col., 9 ff., right col., 1 ff. ; 38: left col., 1 ff., right col., 3 ff. |
|---|---|
| [The Idea of XML is to support the vision of the Semantic Web,] to bring structure to the meaningful content of Web pages, creating an environment where software agents roaming from page to page can read ly carry out sophisticated tasks for users.
2. The Semantic Web It has been discussed that most of the content on the Internet is designed for humans to read, not for computer programs to manipulate meaningfully. Computers can parse Web pages for layout and routine processing (headers, links, meta-tags), but in general computers have no reliable way to process the semantics. [...] The challenge of the semantic web is to provide a language that expresses both data and rules for reasoning about the data and that allows rules from any existing knowledge-representation system to be exported onto the Web. [In the world of the semantic web a tourist can connect to the Internet via his handheld device and enter certain keywords when looking for a restaurant. A software agent searching the web will find the information of a list of restaurant [sic] containing] keywords such as <dinner>, <lunch>, <restaurant>, <Italian> (as might be encoded today) but also that the <opening-hours> at this restaurant are <weekdays> and then the script takes a <time range> in <yyyy-mm-dd-hour> format and returns <table available>, [thus automatically booking a table when the tourist enters <ok>.] For the semantic web to function, computers must have access to structured collections of information and sets of inference rules that they can use to conduct automated reasoning. Knowledge representation, as this technology is often called, is clearly a good idea, and some very nice demonstrations exist, but it has not yet changed the world. It contains the seeds of important applications, but to realize its full potential it must be linked into a single global system. Traditional knowledge-representation systems typically have been centralized, requiring everyone to share exactly the same definition of common concepts, but central [control is stifling, and increasing the size and scope of such a system rapidly becomes unmanageable.] |
[page 36]
Most of the Web's content today is designed for humans to read, not for computer programs to manipulate meaningfully. Computers can adeptly parse Web pages for layout and routine processing—here a header, there a link to another page—but in general, computers have no reliable way to process the semantics: this is the home page of the Hartman and Strauss Physio Clinic, this link goes to Dr. Hartman's curriculum vitae. The Semantic Web will bring structure to the meaningful content of Web pages, creating an environment where software agents roaming from page to page can readily carry out sophisticated tasks for users. Such an agent coming to the clinic's Web page will know not just that the page has keywords such as "treatment, medicine, physical, therapy" [page 37] (as might be encoded today) but also that Dr. Hartman works at this clinic on Mondays, Wednesdays and Fridays and that the script takes a date range in yyyy-mm-dd format and returns appointment times. [...] Knowledge Representation FOR THE SEMANTIC WEB to function, computers must have access to structured collections of information and sets of inference rules that they can use to conduct automated reasoning. Artificial-intelligence researchers have studied such systems since long before the Web was developed. Knowledge representation, as this technology is often called, is currently in a state comparable to that of hypertext before the advent of the Web: it is clearly a good idea, and some very nice demonstrations exist, but it has not yet changed the world. It contains the seeds of important applications, but to realize its full potential it must be linked into a single global system. Traditional knowledge-representation systems typically have been centralized, requiring everyone to share exactly the same definition of common concepts [page 38] such as "parent" or "vehicle." But central control is stifling, and increasing the size and scope of such a system rapidly becomes unmanageable. [...] The challenge of the Semantic Web, therefore, is to provide a language that expresses both data and rules for reasoning about the data and that allows rules from any existing knowledge-representation system to be exported onto the Web. |
The source is given on page 17, but it is not made clear that the text is so close to the source. |
| [28.] Svr/Fragment 017 01 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 17, Zeilen: 1-6, 8-19, 101-114 |
Quelle: Berners-Lee et al 2001 Seite(n): 37, 38, 39, 42, Zeilen: 37: right col., last paragraph; 38: left col. 1 ff., right col. 25 ff., 36 ff.; 39: left col. 1 ff., center col. 2 ff., 20 ff., right col., 1 ff.; 42: left col., 9 ff. |
|---|---|
| [Traditional knowledge-representation systems typically have been centralized, requiring everyone to share exactly the same definition of common concepts, but central] control is stifling, and increasing the size and scope of such a system rapidly becomes unmanageable.
Three important technologies for developing the Semantic Web are already in place: XML, the Resource Description Framework (RDF)1 and Ontologies2. XML allows users to add arbitrary structure to their documents but says nothing about what the structures mean. [This is what RDF (an XML application itself) is used for, expressing meaning. The next challenge for the realization of the semantic web is that] two databases may use different identifiers for what is in fact the same concept, such as <chair>. A program that wants to compare or combine information across the two databases has to know whether these two terms are being used to mean the same thing, a chair to sit on or the chairman of a conference. Ideally, the program must have a way to discover such common meanings for whatever databases it encounters. A solution is provided by ontologies, the third basic component of the Semantic Web. The real power of the Semantic Web will be realized when people create many programs that collect Web content from diverse sources, process the information and exchange the results with other programs. The effectiveness of such software agents will increase exponentially as more machine-readable Web content and automated services (including other agents) become available (Berners-Lee et. al. 2001). 1 RDF (W3C 1999b) encodes XML in sets of triples, each triple being rather like the subject, verb and object of an elementary sentence. These triples can be written using XML tags. In RDF, a document makes assertions that particular things (people, Web pages or whatever) have properties (such as "is a sister of," "is the author of") with certain values (another person, another Web page). This structure turns out to be a natural way to describe the vast majority of the data processed by machines. Subject and object are each identified by a Universal Resource Identifier (URI), just as used in a link on a Web page. The verbs are also identified by URIs, which enables anyone to define a new concept, a new verb, just by defining a URI for it somewhere on the Web. The triples of RDF form webs of information about related things. Because RDF uses URIs to encode this information in a document, the URIs ensure that concepts are not just words in a document but are tied to a unique definition that everyone can find on the Web. 2 Ontologies are a document or file that formally define the relations among terms. They can be compared to a mediator between the information seeker and the set of XML documents. The most typical kind of ontology for the Web has taxonomy and a set of inference rules. Berners-Lee, T. Hendler, J. and Lassila,O. [sic] 2001, "The Semantic Web. A new form of Web content that is meaningful to computers will unleash a revolution of new possibilities.," [sic] The Scientific American, May 2001. W3C (eds) 1999b, Resource Description Framework (RDF). Model and Syntax Specification. W3C Recommendation 22 February 1999. [Online]. Available: http://www.w3.org/TR/REC-rdf-syntax/ |
[page 37]
Traditional knowledge-representation systems typically have been centralized, requiring everyone to share exactly the same definition of common concepts [page 38] such as “parent” or “vehicle.” But central control is stifling, and increasing the size and scope of such a system rapidly becomes unmanageable. [...] Two important technologies for developing the Semantic Web are already in place: eXtensible Markup Language (XML) and the Resource Description Framework (RDF). XML lets everyone create their own tags—hidden labels such as <zip code> or <alma mater> that annotate Web pages or sections of text on a page. [...] In short, XML allows users to add arbitrary structure to their documents but says nothing about what the structures mean [see “XML and the Second-Generation Web,” by Jon Bosak and Tim Bray; SCIENTIFIC AMERICAN, May 1999]. Meaning is expressed by RDF, which encodes it in sets of triples, each triple being rather like the subject, verb and object of an elementary sentence. These triples [page 39] can be written using XML tags. In RDF, a document makes assertions that particular things (people, Web pages or whatever) have properties (such as “is a sister of,” “is the author of”) with certain values (another person, another Web page). This structure turns out to be a natural way to describe the vast majority of the data processed by machines. Subject and object are each identified by a Universal Resource Identifier (URI), just as used in a link on a Web page. (URLs, Uniform Resource Locators, are the most common type of URI.) The verbs are also identified by URIs, which enables anyone to define a new concept, a new verb, just by defining a URI for it somewhere on the Web. [...] The triples of RDF form webs of information about related things. Because RDF uses URIs to encode this information in a document, the URIs ensure that concepts are not just words in a document but are tied to a unique definition that everyone can find on the Web. [...] OF COURSE, THIS IS NOT the end of the story, because two databases may use different identifiers for what is in fact the same concept, such as zip code. A program that wants to compare or combine information across the two databases has to know that these two terms are being used to mean the same thing. Ideally, the program must have a way to discover such common meanings for whatever databases it encounters. A solution to this problem is provided by the third basic component of the Semantic Web, collections of information called ontologies. In philosophy, an ontology is a theory about the nature of existence, of what types of things exist; ontology as a discipline studies such theories. Artificial-intelligence and Web researchers have co-opted the term for their own jargon, and for them an ontology is a document or file that formally defines the relations among terms. The most typical kind of ontology for the Web has a taxonomy and a set of inference rules. [page 42] THE REAL POWER of the Semantic Web will be realized when people create many programs that collect Web content from diverse sources, process the information and exchange the results with other programs. The effectiveness of such software agents will increase exponentially as more machine-readable Web content and automated services (including other agents) become available. |
The source is given, but it is not made clear that the text is so extensively copied. |
| [29.] Svr/Fragment 018 15 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 18, Zeilen: 15-18 |
Quelle: Pitts-Moultis Kirk 1999 Seite(n): 705, Zeilen: 14-18 |
|---|---|
| A software module called an XML processor is used to read XML files and provide access to their content and structure. It is assumed that an XML processor is doing its work on behalf of another module, the application. This specification describes the required behavior [of an XML processor in terms of how it must read XML data and the information it must provide to the application.] | A software module called an XML processor is used to read XML documents and provide access to their content and structure. It is assumed that an XML processor is doing its work on behalf of another module, called the application. This specification describes the required behavior of an XML processor in terms of how it must read XML data and the information it must provide to the application. |
No source is given. |
| [30.] Svr/Fragment 019 07 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 19, Zeilen: 7-10 |
Quelle: Berners-Lee et al 2001 Seite(n): 38, Zeilen: right col., 29 ff. |
|---|---|
| XML enables users to create own tags <address> or <name> that annotate Web pages or sections of text on a page. Scripts, or programs, can make use of these tags in sophisticated ways, but the scriptwriter has to know what the page writer uses each tag for. | XML lets everyone create their own tags—hidden labels such as <zip code> or <alma mater> that annotate Web pages or sections of text on a page. Scripts, or programs, can make use of these tags in sophisticated ways, but the script writer has to know what the page writer uses each tag for. |
The source is not given. |
| [31.] Svr/Fragment 019 11 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 19, Zeilen: 11-16 |
Quelle: Pitts-Moultis Kirk 1999 Seite(n): 707, Zeilen: 21 ff. |
|---|---|
| Each XML document has both a logical and a physical structure. Physically, the document is composed of units called entities. An entity may refer to other entities to cause their inclusion in the document. A document begins in a "root" or document entity. Logically, the document is composed of declarations, elements, comments, character references, and processing instructions, all of which are indicated in the document by explicit markup. | Each XML document has both a logical and a physical structure. Physically, the document is composed of units called entities. An entity may refer to other entities to cause their inclusion in the document. A document begins in a “root” or document entity. Logically, the document is composed of declarations, elements, comments, character references, and processing instructions, all of which are indicated in the document by explicit markup. |
No source is given. |
| [32.] Svr/Fragment 019 21 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 19, Zeilen: 21-27 |
Quelle: Kotok 1999 Seite(n): online, Zeilen: 0 |
|---|---|
| The logical structure of the document and tag set can be specified in a Document Type Definition (DTD). In a DTD, (i) sets of elements and their attributes are defined; (ii) the names that are used as tags are assigned; and (iii) the element relationships or transaction is defined.
If a DTD is used then programs can validate the transaction's structure. The best-known example of a DTD is HTML, which is defined by a SGML-DTD describing the structure of HTML documents. |
The logical structure of the document and tag set can be specified in a Document Type Definition or DTD. (The best-known example of a DTD is HTML, which is defined by a DTD describing the structure of HTML documents.) In a DTD, sets of elements and their attributes are defined; the names that are used as tags are assigned; and the element relationships or transaction is defined. If a DTD is used then programs can validate the transaction's structure. |
No source is given. |
| [33.] Svr/Fragment 020 08 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 20, Zeilen: 8-21 |
Quelle: W3C 1999 Seite(n): online, Zeilen: 0 |
|---|---|
| The W3C Consortium envisions XML applications where a single XML document may contain markup vocabulary (elements and attributes) that are defined for and used by multiple software modules. One motivation for this is modularity; if such a markup vocabulary exists which is well-understood and for which there is useful software available, it is better to re-use this markup rather than re-invent it. But such documents, containing multiple markup vocabularies, pose problems of recognition and collision. Software modules need to be able to recognize the tags and attributes which they are designed to process, even in the face of collisions occurring when markup intended for some other software package uses the same element type or attribute name. XML Namespaces (W3C 1999a) avoid the collision of different semantics, when using different XML documents. XML namespaces provide a simple method for qualifying element and attribute names used in Extensible Markup Language documents by associating them with namespaces identified by URI (Uniform Resource Identifiers) references.
W3C (eds) 1999a, Namespaces in XML, W3C Recommendations, |
XML namespaces provide a simple method for qualifying element and attribute names used in Extensible Markup Language documents by associating them with namespaces identified by URI references.
[...] We envision applications of Extensible Markup Language (XML) where a single XML document may contain elements and attributes (here referred to as a "markup vocabulary") that are defined for and used by multiple software modules. One motivation for this is modularity; if such a markup vocabulary exists which is well-understood and for which there is useful software available, it is better to re-use this markup rather than re-invent it. Such documents, containing multiple markup vocabularies, pose problems of recognition and collision. Software modules need to be able to recognize the tags and attributes which they are designed to process, even in the face of "collisions" occurring when markup intended for some other software package uses the same element type or attribute name. |
The source is given but it is not made clear that the text is so extensively copied. |
| [34.] Svr/Fragment 021 01 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 21, Zeilen: 1-7 |
Quelle: Schwartz 2001 Seite(n): 200, 201, Zeilen: 200: last paragraph; 201: 2 ff. |
|---|---|
| [For the first time Cascading Style] Sheets (CSS) gave Web developers more control over style and layout. Style sheets work like templates where the style for a particular HTML element is defined once, and is then used over and over on any number of Web pages. In order to change how an element looks, the style sheet is modified and the element automatically changes wherever it appears. Before CSS, the only way to change the element was individually, each time it appeared. Style sheets let Webdesigners quickly create more consistent pages, and more consistent sites. | Both Netscape and Internet Explorer support Cascading Style Sheets (CSS), which give Web developers more control over style and layout. (Style sheets made a limited appearance in Internet Explorer 3.0, but not in Navigator 3.0.)
[page 201] Style sheets work like templates—you define the style for a particular HTML element once, and then use it over and over on any number of Web pages. If you want to change how an element looks, you just change the style: the element automatically changes wherever it appears. (Before CSS, you had to change the element individually, each time it appeared.) Style sheets let Web designers quickly create more consistent pages—and more consistent sites. |
No source is given. |
| [35.] Svr/Fragment 021 12 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 21, Zeilen: 12-32 |
Quelle: Seybold report on internet publishing 1997 Seite(n): online, Zeilen: 0 |
|---|---|
| XSL (W3C 2000b) offers more capabilities than the present CSS specification for HTML. [...] XSL adds provisions for formatting of elements based on their position in the document, handling of generated text, and the definition of formatting macros. The new style language complements XML. It also introduces an extensible set of formatting objects and is the first Web style sheet language that accommodates languages that flow in different directions than right to left.
XSL lacks many features one might want to see in a print style sheet (e.g. multiple columns, widow & orphan control, etc.), but its rule-based approach to formatting on the fly is an exciting new development in Web publishing. It will enable an XSLcapable browser to do simple things like rearranging elements and reformatting them accordingly, something that previously could happen only on the server. Furthermore it will bring new capabilities, such as adjusting box rules to the dimensions of the type composed within the box, that are not possible in HTML today. Although it goes beyond CSS, XSL is being developed so that its style sheets can be easily translated to CSS for HTML documents. For publishers who already use SGML, the rapid pace of XML-related development and the noticeably strong interest in it by the big industry players are welcome changes from the past decade, when SGML was relegated to a niche supported only by small software suppliers or by small pockets within larger [developers.] W3C (eds) 2000b, Extensible Stylesheet Language (XSL) Version 1.0 - W3C Candidate Recommendation 21 November 2000, [Online], Available:http://www.w3.org/TR/xsl/ |
Called XSL (Extensible Style Language), the new style language offers more capabilities than the present cascading style sheet specification for HTML. XSL adds provisions for formatting of elements based on their position in the document, handling of generated text and defining formatting macros. It also introduces an extensible set of formatting objects, and is notable for being the first Web style sheet language that accommodates languages (e.g., Hebrew, Arabic) that flow in directions other than from right to left.
Although it goes beyond CSS, XSL is being developed so that its style sheets can be easily translated to CSS for HTML documents. [...] It lacks many specific features one might want to see in a print style sheet (e.g., multiple columns, widow and orphan control, and so forth), but its rules-based approach to formatting on the fly is an exciting new development in Web publishing. It will enable an XSL-capable browser to perform simple tasks—such as rearranging elements and reformatting them accordingly—that previously could only happen on the server. And XSL will bring new capabilities, such as adjusting box rules to the dimensions of the type composed within the box, that are not possible in HTML today. [...] For publishers that already use SGML, the rapid pace of XML-related development and Microsoft’s noticeably strong interest in it are welcome changes from the past decade, when SGML was relegated to a niche supported only by small software suppliers or by small pockets within larger developers. |
The actual source is not given. The text cannot be found at the given reference "W3C (eds) 2000b", see https://web.archive.org/web/20010213224036/http://www.w3.org/TR/xsl/ (February 13, 2001) and https://web.archive.org/web/20010411232116/http://www.w3.org/TR/xsl/ (April 11, 2001). |
| [36.] Svr/Fragment 022 01 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 22, Zeilen: 1-4 |
Quelle: Seybold report on internet publishing 1997 Seite(n): online, Zeilen: 0 |
|---|---|
| Though the first XML implementations will likely focus on data processing, not document formatting, the introduction of a Web style sheet language for XML looks promising as the foundation for richer online style presentations in the future. | Though the first XML implementations will likely focus on data processing, not on document formatting, the introduction of a Web style sheet language for XML looks promising as the foundation for richer online style presentations in the future. |
Continued from previous page. The source is not given. |
| [37.] Svr/Fragment 022 06 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 22, Zeilen: 6-20 |
Quelle: DeRose 1999 Seite(n): online, Zeilen: 0 |
|---|---|
| [2.1.4 XML Navigation]
XML Linking, formerly known as XLink and as XLL (the eXtensible Linking Language), is a work in progress of the Web Consortium. It is closely related to the XML Recommendation, adding functionality for high-function hypertext and hypermedia. It is now an independent Working Group, but its projects were started under the main XML Working Group, and progressed to solid Working Drafts there before being handed off to the new XML Linking Working Group. The work of this working group has two parts: XLink provides advanced linking capabilities such as multidirectional and external linking, while the separate XPointer specifications provide a convenient and easily-understood way of describing locations in XML documents. Either can be used without the other, but they are most valuable in combination, and of course in combination with XML itself. XLink (W3C 2001d) adds many kinds of advanced hypertext linking functionality to the Web (and other environments where it may be used). XLink provides the possibility of bi-directional links or links that lead to multiple destinations. Bidirectional links can traverse in either direction regardless of which way you went originally. W3C (eds) 2001d, XML Linking Language (XLink) Version 1.0. W3C Recommendation 27 June 2001. [Online], Available: http://www.w3.org/TR/xlink/ |
XML Linking, formerly known as XLink and as XLL (the eXtensible Linking Language), is a work in progress of the Web Consortium. It is closely related to the XML Recommendation, but adds functionality for high-function hypertext and hypermedia. It is now an independent Working Group, but its projects were started under the main XML Working Group, and progressed to solid Working Drafts there before being handed off to the new XML Linking Working Group.
The work of this WG has two parts: XLink proper provide advanced linking capabilities such as multidirectional and external linking, while the separate XPointer spec provides a convenient and easily-understood way of describing locations in XML documents. [...] Either of XPointer and XLink can be used without the other; [...] Yet they are especially valuable in combination, and of course in combination with XML itself. [...] XLink adds these kinds of advanced hypertext linking functionality to the Web (and other environments where it may be used):
|
The actual source is not given. The given reference does not lead to the copied text, see https://web.archive.org/web/20010630064508/https://www.w3.org/TR/xlink/ . |
| [38.] Svr/Fragment 022 20 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 22, Zeilen: 20-32 |
Quelle: Funke 1998 Seite(n): online, Zeilen: 0 |
|---|---|
| Bidirectional links can traverse in either direction regardless of which way you went originally. HTML supports one-way links making the "Go Back" button on the browser the way to return to the location of the original link. A bi-directional link will allow a user to return to the original location via a corresponding link on the site. It will also make it easier to find dangling links when a document is moved or deleted. XLink furthermore enables to create links targeted to specific parts within a document. A specific part of information can be targeted rather than the entire document. HTML can do this as well but not with the expected ease of XML coding. Another advantage is the possibility of links having multiple functions. Hyperlinks can be established within a specific document or Web site to perform more than the one function that currently exists. For example, looking at a research document, one might find a descriptor hyperlinked to perform two [functions, one that request for a thesaurus definition and the other to reach other documents carrying the same term.] | Bi-directional links. A link that can traverse in either direction regardless of which way you went originally. HTML supports one-way links making the "Go Back" button on the browser the way to return to the location of the original link. A bi-directional link will allow a user to return to the original location via a corresponding link on the site. It will also make it easier to find dangling links when a document is moved or deleted.
Links targeted to specific parts within a document. A specific part of information can be targeted rather than the entire document. [...] (HTML can do this but not with the expected ease of XML coding.) Links with multiple functions. Hyperlinks can be established within a specific document or Web site to perform more than the one function that currently exists. For example, looking at a research document, you might find a descriptor hyperlinked to perform two functions, one a request for a thesaurus definition and the other to reach other documents carrying the same term. |
No source given. |
| [39.] Svr/Fragment 023 01 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 23, Zeilen: 1-8 |
Quelle: Funke 1998 Seite(n): online, Zeilen: 0 |
|---|---|
| [For example, looking at a research document, one might find a descriptor hyperlinked to perform two] functions, one that request for a thesaurus definition and the other to reach other documents carrying the same term. The XML designer could designate different color links for each function, i.e. red for the definition and blue for the index. When the user placed a cursor over the link, the color would turn red to go to the definition or blue for the index. Last but not least, with XLink links will be able to execute special actions. Some of the proposed actions include hyperlinks that will replace the current document, open a link in a new window, and insert the contents of the link into the current document. | For example, looking at a research document, you might find a descriptor hyperlinked to perform two functions, one a request for a thesaurus definition and the other to reach other documents carrying the same term. The XML designer could designate different color links for each function, say red for the definition and blue for the index. When the user placed a cursor over the link, the color would turn red to go to the definition or blue for the index.
Links with special actions. Some of the proposed actions include hyperlinks that will replace the current document, open a link in a new window, and insert the contents of the link into the current document. |
No source given. |
| [40.] Svr/Fragment 023 09 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 23, Zeilen: 9-11, 14-22 |
Quelle: DeRose 1999 Seite(n): online, Zeilen: 0 |
|---|---|
| XPointer (W3C 2001c) provides better location specifications. XPointers are based on TEI extended pointer, [sic] a proven and multiple-implemented technology for the same purpose, developed by the Text Encoding Initiative. [... ;] it is simply an abstract language that specifies locations. XLink can use XPointer as part of specifying where its link-ends reside. Furthermore, XPointer Links [sic] a point to specific places inside of documents, even when the author of those documents has not already provide [sic] an ID at just the right place. Also Fine-grained addressing to elements, other information objects, point and strings selections, and spans (also called ranges) inside documents is made possible. XPointer also provides a clear syntax for talking about locations and relationships in hierarchies, such as the structure of XML documents, so that locations are human-readable and writeable.
W3C (eds) 2001c, XML Pointer Language (XPointer) Version 1.0. W3C Last Call Working Draft 8 January 2001. [Online], Available: http://www.w3.org/TR/xptr |
XPointer provides better location specifications. It doesn't "return" things; it is simply an abstract language that specifies locations; obviously XLink can use it as part of specifying where its link-ends reside. Some added capabilities of XPointer (beyond HTML's rudimenary use of fragment identifiers on the end of URLs) include:
XPointers are largely based on TEI extended pointers, a proven and multiply-implemented technology for the same purpose, developed by the Text Encoding Initiative. |
The actual source is not given. The given reference does not lead to the content, see https://web.archive.org/web/20010404233121/http://www.w3.org/TR/xptr/ . Re-writing the text introduced a few wrong verb tenses and plurals. |
| [41.] Svr/Fragment 023 30 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 23, Zeilen: 30-32 |
Quelle: Pitts-Moultis Kirk 1999 Seite(n): 97, Zeilen: 28 ff. |
|---|---|
| As XML separates the content from the presentation, it is much easier for search engines, scripting tools and programming or scripting languages to work with the XML data. Presentation tags do not mess up the source-code. | Because XML separates the content from the presentation, it is much easier for search engines, scripting tools, and programming or scripting languages to work with the XML data. Presentation tags don’t get in the way. |
No source is given. |
| [42.] Svr/Fragment 024 01 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 24, Zeilen: 1-2, 14-15, 17-21, 30-35 |
Quelle: Pitts-Moultis Kirk 1999 Seite(n): 97, 98, Zeilen: 97: 6 f., 16 ff., 30 ff.; 98: 5 ff. |
|---|---|
| [Document] structures can be matched with existing systems. Search queries can match the exact level in the XML document where the user needs to search for information.
[...] More and more companies are moving toward using Intranets to help manage documents, document creation, and document distribution. [...] Unless a user creates his own hierarchical structure, handling massive amounts of word documents is difficult at best. Finding information stored within these types of documents is even more frustrating. By using XML’s hierarchical document-handling capability, users can pick up and choose the exact data they want, without having to plow through all the rest. [...] The problem of HTML is that IS departments must decide on standards: standards for creating files, standards for delivering information, and standards for storing, converting and searching for information on the company’s servers. As HTML offers no standards, these must be set by the developers themselves and therefore usually corresponds to what the designer wants, not what the company needs, whereas [XML requires for documents at least be well formed (Pitts-Moultis and Kirk, 1999: 98). Pitts-Moultis, N. & Kirk, C. 1999, XML Black Book: Indispensable Problem Solver, The Coloris Group, Scottsdale, Arizona.] |
More and more companies are moving toward using intranets to help manage documents, document creation, and document distribution.
[...] Unless you create your own hierarchical structure, handling massive amounts of Word documents is difficult at best. Finding information stored within these types of documents is even more frustrating. By using XML’s hierarchical document-handling capabilities, users can pick and choose the exact data they want without having to plow through all the rest. [...] Document structures can be matched within existing systems. Search queries can specify the exact level in the XML document where the user needs to search for information. [page 98] First, information technology departments must decide on standards: standards for creating files, standards for delivering information, and standards for storing, converting, and searching for information on the company’s servers. HTML offers no standards. Instead, standards must be set by the developers themselves. HTML requires no conformity, whereas XML requires conformity for documents to be at the least well-formed and at the most valid. HTML browsers are notoriously forgiving, which means document structures usually correspond to what the designer wants, not what the corporation needs. |
A source is given on p. 25 for the last paragraph, but it is not made clear that the text is so extensively copied. No quotation marks are used. |
| [43.] Svr/Fragment 024 24 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 24, Zeilen: 24-30 |
Quelle: Funke 1998 Seite(n): online, Zeilen: 0 |
|---|---|
| As already discussed, the creators of HTML intended it as a document description language, not a format for the graphics, sound, and video which have become major components of many Web sites today. These developments have resulted in an unintended lack of formatting control that often causes problems with the display of a document and control of the size of a browser window. In order to correct these problems, XML includes DTD and XSL components that make the structuring and formatting of documents more friendly. | As already discussed, the creators of HTML intended it as a document description language, not a format for the graphics, sound, and video which have become major components of many Web sites today. These developments have resulted in an unintended lack of formatting control that often causes problems with the display of a document and control of the size of a browser window. To correct these problems, XML includes DTD (Document Type Definition) and XSL (eXtensible Style Language) components that would make structuring and formatting documents more friendly. |
No source given. |
| [44.] Svr/Fragment 025 02 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 25, Zeilen: 2-21 |
Quelle: Pitts-Moultis Kirk 1999 Seite(n): 98, 99, 100, Zeilen: 98: 23 ff.; 99: 16 ff., 31 ff.; 100: 1 ff. |
|---|---|
| With HTML, one actually has to create pieces of data, parse them down into workable size, and then think ahead to create hyperlinks that will allow users to navigate through the site to the information they need. XML on the other hand does this automatically. Its tree structure, almost like a table of contents, makes it easier for the user to select the data; it also makes it easier for computers to retrieve information. This makes XML a much more sophisticated document management system than HTML. With XSL one can create programming rules for how to pull information out of an XML document and transform it into another format, such as HTML.
PDF versus XML PDF is an electronic file format which is entirely platform independent and which can be passed around from computer to computer. If users have the Acrobat Reader software or plug-ins installed on their browsers, they can read, search and print the file in the format in which the original designer created it. PDF is basically a display technology. It deals little with document format or structure. XML, on the other hand, is much more capable of handling and managing documents, because it is able to provide structured information that a wide variety of applications can understand. It furthermore allows the user to specify how the document is to be presented, whereas the layout and format of PDF documents is hard coded in the page. (Pitts-Moultis and Kirk, 1999: 99). Pitts-Moultis, N. & Kirk, C. 1999, XML Black Book: Indispensable Problem Solver, The Coloris Group, Scottsdale, Arizona. |
[page 98]
With HTML, you actually have to create chunks of data, parse them down into workable size, and then think ahead to create hyperlinks that will allow users to jump through the site to the information they need. XML, on the other hand, does all this automatically. Its tree structure, almost like a table of contents, not only makes it easier for humans to pick out the data they want, it also makes it easier for computers to snatch the data components they need. These strict structural requirements make XML a much more sophisticated document-management system than HTML. [page 99] With XSL, the language used to create style sheets, you can create a collection of programming rules for how to pull information out of an XML document and transform it into another format, such as HTML. [...] The electronic file, entirely platform independent, can then be passed around from computer to computer. If users have the Acrobat Reader software or the Acrobat Reader plug-in is installed in their browsers, they can read, search, and print the file in the format in which the original designer created it. [page 100] PDF is basically a display technology. It deals little with document format or structure. [...] XML, on the other hand, is much more capable of handling and managing documents, because it is able to provide structured information that a wide variety of applications can understand. [...] Better still, XML lets you specify how the document is presented, whereas the layout and format of PDF documents is hard-coded in the page. |
The source is given twice, but it is not made clear that the text is so extensively copied. No quotation marks are used. |
| [45.] Svr/Fragment 025 23 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 25, Zeilen: 23-27, 30-32 |
Quelle: Berners-Lee et al 2001 Seite(n): 42, Zeilen: right col., 18 ff., 40 ff., 47 ff. |
|---|---|
| Service discovery can happen only when there is a common language to describe a service in a way that lets other agents understand both the function offered and how to take advantage of it. In the current Web, services and agents can advertise their function by, for example, depositing such descriptions in directories analogous to the Yellow Pages. [...]
The Semantic Web, in contrast, is more flexible. The consumer and producer agents can reach a shared understanding by exchanging ontologies, which provide the vocabulary needed for discussion. Semantics also makes it easier to [take advantage of a service that only partially matches a request.] |
[page 42]
This process, called service discovery, can happen only when there is a common language to describe a service in a way that lets other agents “understand” both the function offered and how to take advantage of it. Services and agents can advertise their function by, for example, depositing such descriptions in directories analogous to the Yellow Pages. [...] The Semantic Web, in contrast, is more flexible. The consumer and producer agents can reach a shared understanding by exchanging ontologies, which provide the vocabulary needed for discussion. [...] Semantics also makes it easier to take advantage of a service that only partially matches a request. |
The source is not given. |
| [46.] Svr/Fragment 025 27 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 25, Zeilen: 27-29 |
Quelle: Funke 1998 Seite(n): online, Zeilen: 0 |
|---|---|
| Many current search engines geared towards HTML markup and search queries offer this feature which focus on text in the URL, title, summary, or first heading, depending on the structure of the document. | Many current search engines geared towards HTML markup and search queries offer this feature. [...] Search queries using Open Text can focus on text in the URL, title, summary, or first heading, depending on the structure of the document. |
No source is given. |
| [47.] Svr/Fragment 026 01 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 26, Zeilen: 1-3, 9-27 |
Quelle: Funke 1998 Seite(n): online, Zeilen: 0 |
|---|---|
| Thus, XML goes beyond the limitations of the fixed tagging structure of HTML and allows for the introduction of custom tags, resulting in enhanced searching on the Web. [...]
In order to search XML Web pages, however, a search engine must support XMLbased search queries. This will require search engine technology to build XML parsers and processors. The processor would need to recognize the structure of XML tags based on the filtering done by the parser. As XML applications develop for usage on the Web, it is expected that XML-based search engines will emerge. 2.2.3 Multiple uses for Hyperlinking As previously discussed, Xlink provides the possibility of bi-directional links, making the "Go Back" button on the browser obsolete. It will also make it easier to find dangling links when a document is moved or deleted. Xlink furthermore enables to create links targeted to specific parts within a document. A specific part of information can be targeted rather than the entire document. HTML can do this as well but not with the expected ease of XML coding. Another advantage is the possibility of links having multiple functions. Hyperlinks can be established within a specific document or Web site to perform more than the one function that currently exists. Last but not least, with Xlink links will be able to execute special actions. Some of the proposed actions include hyperlinks that will replace the current document, open a link in a new window, and insert the contents of the link into the current document. |
As already discussed, XML will go beyond the limitations of the fixed tagging structure of HTML and allow for the introduction of custom tags, resulting in enhanced searching on the Web.
[...] In order to search XML Web pages, however, a search engine must support XML-based search queries. This will require search engine technology to build XML parsers and processors. The processor would need to recognize the structure of XML tags based on the filtering done by the parser. As XML applications develop for usage on the Web, it is expected that XML-based search engines will emerge. 3. Multiple uses for hyperlinking [...] HTML supports one-way links making the "Go Back" button on the browser the way to return to the location of the original link. [...] It will also make it easier to find dangling links when a document is moved or deleted. Links targeted to specific parts within a document. A specific part of information can be targeted rather than the entire document. [...] (HTML can do this but not with the expected ease of XML coding.) Links with multiple functions. Hyperlinks can be established within a specific document or Web site to perform more than the one function that currently exists. [...] Links with special actions. Some of the proposed actions include hyperlinks that will replace the current document, open a link in a new window, and insert the contents of the link into the current document. |
No source is given. |
| [48.] Svr/Fragment 026 06 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 26, Zeilen: 6-8, 29-30 |
Quelle: Wong 1998 Seite(n): online, Zeilen: 0 |
|---|---|
| When they create a document, they can use the XML metadata tag to think about how other people will consume and access that document.
[...] Many voices in the industry say, that XML will revolutionize the exchange of business information similar to the way the phone, fax machine, and photocopier [did when those devices were invented.] |
XML will revolutionize the exchange of business information similar to the way the phone, fax machine, and photocopier did when those devices were invented, a new report says.
[...] "Web authors can approach content creation more strategically with XML than with HTML," Rappaport said. "When they create a document, they can use the XML metadata tag to think about how other people will consume and access that document." |
No source is given. |
| [49.] Svr/Fragment 027 06 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 27, Zeilen: 6-18 |
Quelle: Wong 1998 Seite(n): online, Zeilen: 0 |
|---|---|
| XML based protocols can interoperate, such as VoxML, the voice recognition protocol, with the banking industry's Open Financial Exchange protocol, which facilitates the exchange of financial data between financial institutions, businesses, and consumers. Banks, for example, can build personal financial management applications that can use voice recognition simply by adding a few lines of XML code, instead of incorporating an entire voice recognition application into the financial software.
With XML specific tags, search engines can give users more refined search results. A search engine seeks the term in the tags, rather than the entire document, giving the user more precise results. Web authors can approach content creation more strategically with XML than with HTML. When they create a document, they can use the XML metadata tag to think about how other people will consume and access that document. |
Rappaport said XML-based protocols can also interoperate, such as VoxML, the voice recognition protocol, with the banking industry's Open Financial Exchange protocol, which facilitates the exchange of financial data between financial institututions, businesses, and consumers. Banks, for example, can build personal financial management applications that can use voice recognition simply by adding a few lines of XML code, instead of incorporating an entire voice recognition application into the financial software, Rappaport said.
With XML-specific tags, search engines can give users more refined search results, he said. A search engine seeks the term in the tags, rather than the entire document, giving the user more precise results. "Web authors can approach content creation more strategically with XML than with HTML," Rappaport said. "When they create a document, they can use the XML metadata tag to think about how other people will consume and access that document." |
No source is given. |
| [50.] Svr/Fragment 027 22 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 27, Zeilen: 22-26 |
Quelle: Norman 1999 Seite(n): 49, Zeilen: 1 ff. |
|---|---|
| Enterprise resource planning (ERP) software producers such as PeopleSoft Inc., Oracle Corp., and SAP AG already incorporate XML syntax into products to help companies lower the cost and labor involved in exchanging data with business partners. Third-party software vendors are pushing XML to enable data exchange over the Web between separate financial systems. | Enterprise resource planning (ERP) heavyweights such as PeopleSoft Inc., Oracle Corp., and SAP AG plan to incorporate XML syntax into products to help companies lower the cost and labor involved in exchanging data with business partners. Separately, third-party software vendors are pushing XML to enable data exchange over the Web between separate financial systems. |
The source is not given. |
| [51.] Svr/Fragment 027 28 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 27, Zeilen: 28-31 |
Quelle: Pitts-Moultis Kirk 1999 Seite(n): 480, Zeilen: 2 ff., last 3 lines |
|---|---|
| With the flexibility of XML to create new vocabularies, which are actually the applications that use the XML language, industries can create their own elements, attributes and entities that fully explain the structure (with DTD and XML Schema) of the specific types of data they use. That means that XML allows anybody to [construct entirely new applications, not through conventional programming methods, but rather by defining the contextual structure of the document.] | XML offers the flexibility to create new vocabularies, which are actually applications that use the XML language. This means organizations and industries can create their own elements, attributes, and entities that fully explain the structure of the specific types of data they use.
[...] XML allows you to construct entirely new applications, not through conventional programming methods, but rather by defining the contextual structure of the document |
No source is given. |
| [52.] Svr/Fragment 028 05 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 28, Zeilen: 5-19 |
Quelle: Sanborn Lattig 2000 Seite(n): 16, Zeilen: left col., 1 ff. |
|---|---|
| − Extensible HTML (XHTML): The WWW Consortium (W3C), seeking to expand the use of XML without making existing HTML elements obsolete, recommended the XHTML 1.0 specification as a bridge between the two language environments. The specification is designed to allow developers to create Web pages that combine the data structuring of XML and the presentation of HTML. XHTML 1.0 was created by rewriting HTML 4 as an XML application, creating a specification that will work with HTML browsers and leverage XML's device-independent access capabilities. Developers already writing HTML 4 documents should have a smooth transition to XHMTL 1.0. XHTML will simplify the Web development process by obviating the need for developing multiple versions of a single Web site based on the type of device upon which the site will run. XHTML is the immediate link between the two standards, allowing developers to program their Web Sites without having to go through and strip out everything and reprogram what they already have in order to take advantage of XML. | THE WORLD WIDE Web Consortium (W3C), seeking to expand the use of XML without making existing HTML elements obsolete, recommended the XHTML (Extensible HTML) 1.0 specification as a bridge between the two language environments.
The specification is designed to allow developers to create Web pages that combine the data structuring of XML and the presentation of HTML. XHTML 1.0 was created by rewriting HTML 4 as an XML application, creating a specification that will work with HTML browsers and leverage XML's device-independent access capabilities. [...] Developers already writing HTML 4 documents should have a smooth transition to XHMTL 1.0, said Janet Daly, a spokesperson for the W3C, adding that the W3C provides tools to convert HTML 4 documents into XHTML. [...] XHTML will simplify the Web development process by obviating the need for developing multiple versions of a single Web site based on the type of device upon which the site will run, ZOT Group's Khudairi added. "[XHTML] is the immediate link between the two standards, allowing developers to program their Web Sites without having to go through and strip out everything and reprogram what they already have in order to take advantage of XML," Khudairi said. |
No source is given. |
| [53.] Svr/Fragment 028 19 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 28, Zeilen: 19-21 |
Quelle: Johnson 1999 Seite(n): 81, Zeilen: left col., 39 ff. |
|---|---|
| Pages developed in XHTML 1.0 instead of the current HTML 4.0 can be processed by standard XML tools without becoming completely useless to older HTML only technologies. | W3C has targeted XHTML as a chief migration tool for bringing the vast archives of HTML documents into the XML world; pages developed in XHTML 1.0 instead of the current HTML 4.0 can be processed by standard XML tools without becoming completely useless to older HTML-only technologies. |
No source is given. |
| [54.] Svr/Fragment 028 22 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 28, Zeilen: 22-32 |
Quelle: Funke 1998 Seite(n): online, Zeilen: 0 |
|---|---|
| - Resource Definition Format (RDF) is the XML application for Metadata under development by the W3C to address areas such as better search engine capabilities and cataloging content. RDF will establish the syntax for how different tags relate to Web pages and to one another. Users or groups will be able to name the tags and decide the collections of tags to use. The Dublin Core, an RDF standard under development by the library community, consists of 15 tags that give basic information about electronic documents.
- Meta Content Framework (MCF) is Netscape's application for XML based on RDF for processing metadata. MCF will represent meta information about content that includes Web pages, desktop files, gopher and FTP files, e-mail, and structured databases. |
RDF (Resource Definition Format). The XML application for Metadata under development by the W3C to address areas such as better search engine capabilities and cataloging content. RDF will establish the syntax for how different tags relate to Web pages and to one another. Users or groups will be able to name the tags and decide the collections of tags to use. The Dublin Core, an RDF standard under development by the library community, consists of 15 tags that give basic information about electronic documents.
MCF (Meta Content Framework). Netscape's application for XML based on RDF for processing metadata. MCF will represent meta information about content that includes Web pages, desktop files, gopher and FTP files, e-mail, and structured databases. |
No source is given. |
| [55.] Svr/Fragment 029 01 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 29, Zeilen: 1-10, 18-21, 28-30 |
Quelle: Funke 1998 Seite(n): online, Zeilen: 0 |
|---|---|
| - Channel Definition Format (CDF) is an XML-based file format for the description of channel information developed by Microsoft. Supported by Microsoft's Internet Explorer 4.0 and above, CDF is already in use by such sites as PointCast. The concept of Channels involves the organization and classification of information from Web servers and Web pages.
- Chemical Markup Language (CML): One of the earliest XML applications, CML is being developed to represent molecular science and related technical information on the Web, using a CML DTD and CML tags. Files would require a viewer such as CML Viewer to display. The sponsor is Open Molecule Foundation. [...] - Synchronized Multimedia Integration Language (SMIL) is an XML-based application for the delivery of multimedia content on the Web. SMIL permits multimedia synchronization of the delivery of sound, video, graphics, and text, reducing the bandwidth. [...] - XML/EDI: The XML/EDI group has developed an XML standard for electronic commerce that would move it from the value-added network onto the Internet reaching a broader cross section of business (see chapter 4). |
CDF (Channel Definition Format). An XML-based file format for the description of channel information developed by Microsoft. Supported by Microsoft's Internet Explorer 4.0 and above, CDF is already in use by such sites as PointCast. The concept of Channels involves the organization and classification of information from Web servers and Web pages.
CML (Chemical Markup Language). One of the earliest XML applications, CML is being developed to represent molecular science and related technical information on the Web, using a CML DTD and CML tags. Files would require a viewer such as CML Viewer to display. The sponsor is Open Molecule Foundation. SMIL (Synchronized Multimedia Integration Language). An XML-based application for the delivery of multimedia content on the Web. SMIL permits multimedia synchronization of the delivery of sound, video, graphics, and text, reducing the bandwidth. XML/EDI (Electronic Data Interchange). [...] The XML/EDI group has developed an XML standard for electronic commerce that would move it from the value-added network onto the Internet -- reaching a broader cross section of business. |
No source is given. |
| [56.] Svr/Fragment 029 11 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 29, Zeilen: 11-17 |
Quelle: Wong 1998 Seite(n): online, Zeilen: 0 |
|---|---|
| - OFX and VOXML: XML-based protocols can interoperate, such as VoxML, the voice recognition protocol, with the banking industry's Open Financial Exchange protocol, which facilitates the exchange of financial data between financial institutions, businesses, and consumers. Banks, for example, can build personal financial management applications that can use voice recognition simply by adding a few lines of XML code, instead of incorporating an entire voice recognition application into the financial software. | Rappaport said XML-based protocols can also interoperate, such as VoxML, the voice recognition protocol, with the banking industry's Open Financial Exchange protocol, which facilitates the exchange of financial data between financial institututions, businesses, and consumers. Banks, for example, can build personal financial management applications that can use voice recognition simply by adding a few lines of XML code, instead of incorporating an entire voice recognition application into the financial software, Rappaport said. |
No source is given. See p. 27. |
| [57.] Svr/Fragment 029 22 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 29, Zeilen: 22-27 |
Quelle: Norman 1999 Seite(n): 49, Zeilen: 7 ff. |
|---|---|
| - Web Interface Definition Language (WIDL), introduced in 1996, was one of the first applications of XML. WIDL provides a means of describing automated access to Web-enabled resources and enterprise applications through well-defined interfaces much like COM and CORBA. By abstracting information about Web and external application resources, applications can be protected from changes in the structure, appearance, and location of data. | At the heart of webMethods B2B is the Web Interface Definition Language (WIDL) [11]. Introduced in 1996, WIDL was one of the first applications of XML. WIDL provides a means of describing automated access to Web-enabled resources and enterprise applications through well-defined interfaces much like COM and CORBA. By abstracting information about Web and external application resources, applications can be protected from changes in the structure, appearance, and location of data.
[11] Web Interface Definition Language (WIDL) |
The source is not given. |
| [58.] Svr/Fragment 030 05 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 30, Zeilen: 5-10, 17-23 |
Quelle: Kotok 2000a Seite(n): online, Zeilen: 0 |
|---|---|
| The next section will analyze the development of XML applications for e-commerce, thus excluding applications designed for strictly enhancing XML, such as XSL even though they too may have use in business. The purpose of the next section is to show the extent of XML's penetration into the world of business data exchange, which covers transactions between businesses and also with consumers, including scientific and technical.
[...] To help understand the various ways in which XML for business data exchange has grown, applications can be broken down into three major categories (See Appendix 3 for more detailed information on XML business applications): (i) XML Application Functions set the guidelines for specific business operations that cut across industry boundaries. (ii) Vertical XML Applications are one-industry applications, defining messages for exchanges within a specific industry. |
The purpose of this survey is to show the extent of XML's penetration into the world of business data exchange, which covers transactions between businesses and also with consumers. As a result, the survey excludes XML vocabularies for enhancing XML, such as XML Schema, XPath, or XLink, even though they may have business implications. It also excludes applications designed for strictly publishing purposes, such as XHTML, even though they too may have use in business. But the survey tries to cover as many potential business data exchanges as possible, and thus includes scientific, technical, and even religious vocabularies.
To help understand the various ways in which XML for business data exchange has grown, the survey breaks down the applications into three major categories: Frameworks: specifications for structuring XML messages between parties for exchanges both within and among industries Functions: guidelines for specific business operations that cut across industry boundaries Verticals: messages for exchanges within a specific industry. |
Source is not given. |
| [59.] Svr/Fragment 030 12 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 30, Zeilen: 12-16, 23-29 |
Quelle: Kotok 2000 Seite(n): online, Zeilen: 0 |
|---|---|
| In February 2000, XML.com published a survey that found 124 different XML business applications at various registries and reference sources. By August 2000, the number of XML business vocabularies listed with these sources appears to have doubled to over 250, putting even more pressure on standards bodies to develop a way for these applications to interact (Kotok 2000).
[...] (ii) [...] They represent the majority of the business vocabularies (146 of the 251). (iii) XML Application Frameworks define the specifications for structuring XML messages between parties for exchanges both within and among industries. Frameworks represent the fewest number of vocabularies. They offer interoperability among the business languages and provide the most functionality, thus frameworks have received the most attention. |
In February 2000, XML.com published a survey that found 124 different XML business applications at various registries and reference sources. By August 2000, the number of XML business vocabularies listed with these sources appears to have doubled to over 250, putting even more pressure on standards bodies to develop a way for these applications to interact.
As in the first survey, a majority of the vocabularies (146 of the 251) represent one-industry applications, called verticals. Some 95 other entries express business functions, defined as common operations that apply to a number of industries. The fewest number of vocabularies are frameworks that offer interoperability among the business languages, but frameworks provide the most functionality and have received the most attention. |
The source is given, but it is not made clear that the text is so extensively copied. No quotation marks are used and the copying continues after the in-text reference. |
| [60.] Svr/Fragment 030 30 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 30, Zeilen: 30-31 |
Quelle: Enigma 1999 Seite(n): online, Zeilen: 0 |
|---|---|
| The question of whether XML would enter the market was answered when Microsoft, Adobe, Netscape and other big market players not only supported the [development of the new standard, but also began making sizable product investments to this new format.] | The question of whether XML would enter the market was answered when Microsoft, Adobe, Netscape and other vendors not only voiced their support of the emerging standard but began making sizable product investments to this new format. |
No source is given. |
| [61.] Svr/Fragment 031 01 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 31, Zeilen: 1-2, 8-10 |
Quelle: Enigma 1999 Seite(n): online, Zeilen: 0 |
|---|---|
| [The question of whether XML would enter the market was answered when Microsoft, Adobe, Netscape and other big market players not only supported the] development of the new standard, but also began making sizable product investments to this new format. [...] The question that is open is not whether XML will succeed as a widespread data format for e-commerce applications, but rather how fast, to what level of success and with what vocabularies. | The question discussed here is not whether XML will succeed as a widespread data format, but rather how fast, to what level of success and with what products. The question of whether XML would enter the market was answered when Microsoft, Adobe, Netscape and other vendors not only voiced their support of the emerging standard but began making sizable product investments to this new format. |
No source is given. |
| [62.] Svr/Fragment 031 02 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 31, Zeilen: 2-5 |
Quelle: Bartlett 1997 Seite(n): online, Zeilen: 0 |
|---|---|
| The momentum building behind the XML effort means that XML is inevitably destined to become the mainstream technology for powering broadly functional and highly valuable business applications on the Internet, intranets, and extranets. | "[...] The momentum building behind the XML effort means that XML is inevitably destined to become the mainstream technology for powering broadly functional and highly valuable business applications on the Internet, intranets, and extranets." |
The source is not given. |
| [63.] Svr/Fragment 031 12 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 31, Zeilen: 12-17 |
Quelle: Weitzel et al 2000 Seite(n): 1, Zeilen: left col., 21 ff. |
|---|---|
| Open standards in general and XML in particular will play a major role in emerging electronic marketplaces. So far, there was no ubiquitous way of describing data, e.g. on websites or for heterogeneous applications, in a commonly understandable way. There was no universal data format. XML has the potential, especially in combination with Java, to be the data format of choice to enable the next step in the evolution of Electronic Data Interchange [in particular, and e-commerce in general.] | But we are quite convinced that open standards in general and the eXtensible Markup Language (XML) in particular will play a major role in emerging electronic marketplaces. So far, there was no ubiquitous way of describing data, e.g. on websites or for heterogeneous applications, in a commonly understandable way. There was no universal data format. XML, proposed by the World Wide Web Consortium in February of 1998, has the potential, especially in combination with Java, to be the data format of choice to enable the next step in the evolution of EDI [1].
[1] Bosak, J.: XML, Java and the future of the Web, October, 3rd, http://sunsite.unc.edu/pub/suninfo/standards/xml/why/xmlapps.ps.zip |
No source is given. |
| [64.] Svr/Fragment 032 01 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 32, Zeilen: 1-2 |
Quelle: Weitzel et al 2000 Seite(n): 1, Zeilen: right col., 5 ff. |
|---|---|
| [Eventually, XML’s ability to separate structure from content is expected to contribute to the] emergence of open markets with non-proprietary XML interfaces being the foundation of business-to-business communication. | Eventually, XML’s ability to separate structure from meaning is expected to contribute to the emergence of open markets with non-proprietary XML interfaces being the foundation of business- to-business communication. |
No source is given. |
| [65.] Svr/Fragment 032 03 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 32, Zeilen: 3-4, 5-11 |
Quelle: Erdmann Studer 1999 Seite(n): online, Zeilen: 0 |
|---|---|
| But, in spite of the positive features and prospects of XML, two things must be kept in mind. [It is not yet clear when and how and which XML business vocabularies will penetrate e-commerce applications.] Furthermore, XML is solely a description language to specify the structure of documents and thus their syntactic dimension. Document structure can represent some semantic properties but it is not clear how this can be deployed outside of special purpose applications. DTD and document structure are not enough to give XML a sound semantics. Therefore it will be necessary to appoint true semantics to XML documents with RDF and ontologies. | In spite of these positive features and prospects of XML it must be clearly stated that XML is solely a description language to specify the structure of documents and thus their syntactic dimension. The document structure can represent some semantic properties but it is not clear how this can be deployed outside of special purpose applications. We will define in this paper how to add true semantics to XML documents by relating the document structure to an ontology.
[...] Of course concepts and relationships have to be expressed and stored in linear form in documents; but this is pure representation, i.e. DTDs and the document structure are not enough to give XML a sound semantics. |
No source is given. The text can also be found as a closer copy in Fragment 055 01. |
| [66.] Svr/Fragment 032 13 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 32, Zeilen: 13-20 |
Quelle: Norman 1999 Seite(n): 43, 44, Zeilen: 43: last paragraph; 44: 1 f. |
|---|---|
| [3. EDI]
Companies today have put great effort into constructing computer applications to help them in their business processes. While this has resulted in significant improvements in efficiency, that efficiency has not been extended to external processes. External processes are processes that involve interchange between applications or business processes at different companies. Companies have in many cases created islands of automation that are isolated from their suppliers, trading partners, and customers. EDI has been heralded as the solution to this problem. |
3.4 XML and Electronic Transactions
Companies have today put great effort into constructing computer applications to help them in their business processes. While this has resulted in significant improvements in efficiency, that efficiency has not been extended to external processes. By external processes I mean processes that involve interchange between applications or business processes at different companies. Companies have in many cases created islands of automation that are isolated from their suppliers, trading partners, and customers. Electronic Data [page 44] Interchange (EDI) has been heralded as the solution to this problem. |
The source is not given. |
| [67.] Svr/Fragment 032 21 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 32, Zeilen: 21-23 |
Quelle: Parfett 1992 Seite(n): 5, Zeilen: 16 ff. |
|---|---|
| The origins of EDI may be tracked down to the United States when in the 1960s various industry sectors (airlines, car manufacturing and health) established the idea of EDI. | EDI is not new. Its origins may be traced back to the United States when in the 1960s various industry sectors (airlines, car manufacturing and health) established EDI trials, albeit involving, in comparison with today’s technology, poorly developed standards and inflexible communications links. |
No source is given. |
| [68.] Svr/Fragment 032 23 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 32, Zeilen: 23-32 |
Quelle: Emmelhainz 1990 Seite(n): 21, 81, Zeilen: 21: 18 ff.; 81: 7 ff. |
|---|---|
| In 1968 a number of companies in the transportation industry formed a committee to evaluate the feasibility of developing standards for electronic communication, called Transportation Data Coordinating Committee (TDCC). The actions of TDCC formed the foundations for EDI as used today. In 1987 the EDFICAT (EDI for Administration, Commerce, and Transport) standard was defined by the UN together with ISO as an international standard using the ANSI X12 standard and the TDI standard as a basis. The International Standardization Organization (ISO) is responsible for developing syntax rules and the data dictionary. The United Nations Economic Commission for Europe is responsible for the development of document standards (Emmelhainz 1990).
Emmelhainz, M. 1990, Electronic Data Interchange: A total Management Guide. Van Nostrand Reinhold, New York. |
In 1968 a number of companies in the transportation industry formed a committee to evaluate the feasibility of developing standards for electronic communication. This committee was known as the Transportation Data Coordinating Committee (TDCC). The actions of the TDCC formed the foundation for EDI as used today.
[page 81] In 1987, efforts to create an international standard, EDI for Administration, Commerce, and Transport (EDIFACT), were undertaken. [...] The International Standards Organization (ISO) is responsible for developing syntax rules and the data dictionary. The United Nations Economic Commission for Europe is responsible for the development of the document standards. |
The source is given, but it is not made clear how close the text is to the source. No quotation marks are used. |
| [69.] Svr/Fragment 033 01 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 33, Zeilen: 1-3 |
Quelle: Ritz 1995 Seite(n): 12, Zeilen: last 3 lines |
|---|---|
| EDI has evolved from bilateral, individually negotiated agreements between pairs of two trading partners (e.g. a buyer and a seller engaged in an ongoing business relationship), to multilateral. | Historically, EDI has evolved from bilateral, individually negotiated agreements between pairs of two trading partners, e.g. a buyer and a seller engaged in an ongoing business relationship, about how to coordinate the exchange of trade documents. |
No source is given. |
| [70.] Svr/Fragment 033 03 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 33, Zeilen: 3-8 |
Quelle: Weitzel et al 1999 Seite(n): online, Zeilen: 0 |
|---|---|
| Today, EDI is the business-to-business exchange of electronic documents in a standardized machine-processable format. EDI enables partners to electronically exchange structured business documents, such as purchase orders and invoices, their computer systems. EDI is a means of reducing the costs of document processing and, in general, to achieve strategic business advantages made possible by shorter business process cycle times (Weitzel et al. 1999).
Weitzel, T. & Buxmann, P. 1999, A communication architecture for the digital economy: 21st century EDI Weitzel, T., Buxmann, P., Ladner, F., König, W. 1999a, XML: Konzept und Anwendungen der Extensible Markup Language, SFB 403 FB-99-20, [Online]. Weitzel, T., Buxmann, P., Kronenberg, R., & Ladner, F. 1999b, XML/EDI: The (r)evolution of EDI, Institute of Information Systems, Working Paper 99-10, [Online]. |
Electronic Data Interchange (EDI) is the business-to-business exchange of electronic documents in a standardized machine-processable format. EDI enables partners to electronically exchange structured business documents, such as purchase orders and invoices, between their computer systems. EDI is a means of reducing the costs of document processing and, in general, to achieve strategic business advantages made possible by shorter business process cycle times. |
The source is given but it is not made clear that the text is so extensively copied. Weitzel et al. 1999 might refer to Weitzel, T. & Buxmann, P. 1999, A communication architecture for the digital economy: 21st century EDI or to Weitzel, T., Buxmann, P., Kronenberg, R., & Ladner, F. 1999b, XML/EDI: The (r)evolution of EDI, Institute of Information Systems, Working Paper 99-10, [Online]. Avaliable: [sic] http://www.wiwi.uni-frankfurt.de/~tweitzel/XMLEDI.doc Accessed: October 29 1999 As the text is copied literally without quotation marks it is a pawn sacrifice either way. |
| [71.] Svr/Fragment 033 09 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 33, Zeilen: 9-25 |
Quelle: Carroll 2000 Seite(n): online, Zeilen: 0 |
|---|---|
| EDI standards in wide use are the American ANSI ASC-X12 and the international UN/EDIFACT. However, these standards predate Internet e-commerce and reflect a flat-file-based, least-common-denominator approach to computer data interchange. With the explosive growth of Internet, such interchange standards are considered by many to be inflexible and inadequate. New methods of exchanging structured data based on Internet technologies are now dominant.
Traditional EDI has much to offer semantically and structurally to Internet B2B, but its syntax is definitely antiquated. XML/EDI working groups are working on helping to ensure that valuable domain knowledge codified in EDI standards that is, the semantics and structure of business documents is not lost in the rush to deploy newer technologies like XML. However, XML-based approaches have the potential to go beyond the mere reproduction of EDI transactions in XML format. XML brings the potential for document processing and validation. Of course, there are still plenty of legacy systems that need to be fed X12 or EDIFACT documents, so developers need to integrate Internet messaging and data transfer mechanisms with translators that can talk to the back-end legacy systems. |
A couple of EDI standards in wide use are ANSI ASC X12 and the international UN/EDIFACT. However, these standards predate Internet e-commerce and reflect a flat-file-based, least-common-denominator approach to computer data interchange. With the explosive growth of Internet e-commerce, however, such interchange standards are considered by many to be inflexible and inadequate. New methods of exchanging structured data based on HTML and XML are now dominant.
Of course, there are still plenty of legacy systems that need to be fed X12 or EDIFACT documents, so developers need to integrate Internet messaging and data transfer mechanisms with translators that can talk to the back-end legacy systems. Traditional EDI has much to offer semantically and structurally to Internet B2B -- but its syntax is definitely antiquated. [...] It helps ensure that valuable domain knowledge codified in EDI standards -- that is, the semantics and structure of business documents -- is not lost in the rush to deploy newer technologies like XML. However, XML-based approaches have the potential to go beyond the mere reproduction of EDI transactions in XML format. XML brings the potential for document processing and validation. |
No source is given. |
| [72.] Svr/Fragment 034 02 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 34, Zeilen: 2-11 |
Quelle: Parfett 1992 Seite(n): 49, Zeilen: 9 ff. |
|---|---|
| Computer Systems, whether big or small, are today considered to be an integral part of most trading operations. The data for such systems will typically be entered manually before processing and subsequently written to such output documents as invoices, orders, acknowledgements, delivery notes, etc., which are then typically distributes via the postal services. With EDI, this data is extracted in an electronic form, structured according to the appropriate in-house file format. This is subsequently converted to an agreed document format standard and is the in a suitable form for transfer via some form of EDI network function, to the relevant trading partner. When received, the information will be decoded into the electronic in-house format of the receiving company. | Computer systems, whether micro, mini or mainframe are now considered to be an integral part of most trading operations. The data for such systems will typically be entered manually before being processed and subsequently written to such output documents as invoices, orders, acknowledgements and delivery notes. These documents are then normally distributed via the postal services.
With EDI, data is extracted in an electronic form, structured according to the appropriate in-house file format. This is subsequently converted to an agreed document format standard and is then in a suitable form for transfer, via some form of EDI network function, to the relevant trading partner. When received, the information will be de-coded from the agreed EDI standard format and converted into one suitable for their in-house system. |
A source is only given for Figure 6, which is below this text portion. |
| [73.] Svr/Fragment 034 13 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 34, Zeilen: 13-16, 17 |
Quelle: Emmelhainz 1990 Seite(n): 82, Zeilen: 21 ff. |
|---|---|
| [3.1.1 EDI Message Standards]
For a conversation to be effective, both parties must speak the same language. The same is true for the use of EDI. In order for computer-to-computer communication to be successful, both of the computers involved must be able to read and understand data the same way. [fig. 6] EDI provides this common language need. |
[SUMMARY]
For a telephone conversation to be effective, both parties must speak the same language. The same holds true for the use of EDI. In order for computer-to-computer communication to be successful, both of the computers involved must be able to read and understand data in the same way. EDI standards provide the common language needed for EDI to work. |
The source is given on the next page for a literal quote that follows this fragment, but it is not made clear that the documented text is copied as well. |
| [74.] Svr/Fragment 035 10 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 35, Zeilen: (1-3), 10-17, 30-31 |
Quelle: Emmelhainz 1990 Seite(n): (14), 16, 80, 89, Zeilen: (14: 31-34); 16: 5 ff.; 80: 28 ff.; 89: 5 ff. |
|---|---|
| [ ["[...] These rules] of format and syntax provide an accepted way of communicating between business and ensure that the message sent is understood upon receipt. Similar rules of format and syntax exist in the world of EDI" (Emmelhainz 1990: 14).]
[...] This is where a standard like EDI makes sense. Standards can be either (i) proprietary or (ii) common (open). Proprietary EDI standards are limited to the use of one company and it's trading partners. These are systems in which the organizations have developed a standard format used in communication only with that organization's trading partners on a closed system. While these systems are often referred to as EDI, they do not use common EDI standards. Common EDI standards are guidelines adopted by industry-wide or cross-industry users (Emmelhainz 1990). [...] As explained above, EDI standards provide the structure and the common format for electronic messages. However, since no organization has its data file [structured in EDI format, some method of transforming data from a company specific format to the EDI standard format is needed. EDI software performs this function.] Emmelhainz, M. 1990, Electronic Data Interchange: A total Management Guide. Van Nostrand Reinhold, New York. |
[page 14]
[These rules of format and syntax provide an accepted way of communicating between businesses and ensure that the message sent is understood upon receipt. Similar rules of format and syntax exist in the world of EDI.] [page 16] Proprietary Standards As guidelines for formatting and communication, EDI standards can be either proprietary or common. Proprietary EDI standards are formatting and communications guidelines whose use is limited to one organization and its trading partners. [...] Common EDI Standards Common EDI standards, on the other hand, are guidelines adopted by industry-wide or cross-industry users. [page 80] These are systems in which the organization has developed a “standard” format used in communicating only with that organization’s trading partners on a closed system. While these types of systems are often referred to as EDI, they do not use common EDI standards as the format or method of communication. [page 89] As explained in Chapter 4, EDI standards provide the structure and the common format for electronic messages. However, since no organization has its data file structured in EDI format, and since manual input of data in EDI format would be tedious and time consuming, some method of transforming data from a company-specific format to the EDI standard format is needed. EDI software performs this function. |
The source is mentioned twice. At the top of the page there is a passage that is correctly referenced as a literal quote (and therefore only documented here), but it is not made clear that additional passages are also extremely close to the source. |
| [75.] Svr/Fragment 035 20 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 35, Zeilen: 9-10, 20-28 |
Quelle: Parfett 1992 Seite(n): 40, 42, Zeilen: 40: 20 ff.; 42: 6 ff. |
|---|---|
| The desirable solution for all trading partners is to agree upon common standards from converting data from and into their in-house systems.
[...] Message refers to a specific Type of EDI dialogue, which is formed to achieve a particular trade function. Functional Groups are groups of messages of the same type, e.g. all purchase orders to one company. Interchange is the envelope that contains the message standards and functional groups thereof. Interchange forms the entirety of an EDI communication between trading partners. Syntax Rules effectively specify the grammar for EDI dialogue. Message Design Guidelines allow groups engaged in designing new messages or modifying existing messages to do so in a consistent manner, which will allow other users to understand them. |
The desirable solution is for all trading partners to agree to adopt a common standard for their in-house systems, which would remove any requirement for conversion routines.
[page 42] A message is a specific type of EDI dialogue which is formed to achieve a particular trade function. [...] - Functional Groups. These refer to groups of messages of the same type, eg all purchase orders to one company. - Interchange. The interchange forms the entirety of an EDI communication between trading partners. It is the envelope which contains the messages and functional groups thereof. [...] - Syntax Rules. The syntax rules effectively specify the grammar for EDI dialogue. [...] - Message Design Guidelines. Message design guidelines allow groups engaged in designing new messages or modifying existing messages to do so in a consistent manner, which will allow other users to understand them. |
The source is given only for a literal quote top of page that is part of the previous chapter. |
| [76.] Svr/Fragment 036 01 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 36, Zeilen: 1-6 |
Quelle: Emmelhainz 1990 Seite(n): 16, 89, Zeilen: 16: 26 ff.; 89: 5 ff. |
|---|---|
| [However, since no organization has its data file] structured in EDI format, some method of transforming data from a company specific format to the EDI standard format is needed. EDI software performs this function. Just as every company has its own paper form on which information is placed, every company has its unique format and structure for its database. Converting Software is needed to translate information from the company specific database into the EDO standard format for transmission. | [page 89]
However, since no organization has its data file structured in EDI format, and since manual input of data in EDI format would be tedious and time consuming, some method of transforming data from a company-specific format to the EDI standard format is needed. EDI software performs this function. [page 16] Just as every company has its own paper form on which information is placed, every company has its own unique format and structure for its database. Therefore, some method must be used to take the information from the company-specific database and translate it to EDI standard format for transmission. |
The source is given for the third paragraph on the page, after citing a different source for the second paragraph. No quotation marks are given. |
| [77.] Svr/Fragment 036 07 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 36, Zeilen: 7-14 |
Quelle: Parfett 1992 Seite(n): 49, Zeilen: 18 ff. |
|---|---|
| EDI standard format are converted into a format suitable for their in-house system. The data can then be inserted into a suitable in-house file ready for subsequent processing by the appropriate application software. However, studies have shown that many companies, especially in SMEs, often printed out the received EDI message (Parfett 1992: 49).
The basic aspects, which need to be considered when looking at EDI software, as illustrated above are: (i) Data extraction, (ii) Data encoding, (iii) Data transmission, (iv) Data receipt, (v) Data de-coding, and (vi) Data insertion (Emmelhainz 1990). |
When received, the information will be de-coded from the agreed EDI standard format and converted into one suitable for their in-house system. The data can then be inserted into a suitable in-house file ready for subsequent processing by the appropriate application software. However, it must be said that in many initial installations, especially in SMEs, the received EDI message is often printed out.
The above is a simple description of the EDI process but one which illustrates the basic aspects which need to be considered when looking at EDI software. These are:
|
The source is given, but it is not made clear that the text is so extensively copied - no quotation marks, and that the copying continues also after the reference. |
| [78.] Svr/Fragment 037 01 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 37, Zeilen: 1-6, 8-9, 11-17, 18-21 |
Quelle: Emmelhainz 1990 Seite(n): 17, 89, Zeilen: 17: 16 ff., 28 ff.; 89: 11 ff. |
|---|---|
| EDI software translates information from unstructured, company specific format to the structured EDI format and then communicates the EDI message. EDI software also performs this activity in reverse (receives the message and translates from standard format to company specific format). EDI software can be either developed in-house or it can be purchased from a number of commercial software vendors.
[3.1.4 EDI Networks] Classic EDI documents are transmitted electronically through phone or data lines from one computer to the other. [...] Direct Network: Computers of trading partners are linked directly, usually through dial up modems or leased lines. When one of the partners wants to transmit documents to the other, the sender simply dials up the receiving party and transmits the document. Value Added Networks, also known as third party networks or indirect networks, serve as an intermediary between trading partners. The VAN in an EDI world is similar to the post office in the paper world. [...] A VAN maintains a mailbox for both the sender and the receiver. In this way, if a company has a large number of electronic purchase orders to send to different sellers, the company would transmit all of the purchase orders to the VAN in a single connect or call. [The application provides added value to data network and allows users to purchase facilities as electronic mail, on-line database access, and EDI. (Emmelhainz 1990: 17).] Emmelhainz, M. 1990, Electronic Data Interchange: A total Management Guide. Van Nostrand Reinhold, New York. |
[page 89]
EDI software consists of computer instructions that translate information from unstructured, company-specific format to the structured EDI format and then communicates the EDI messsage. EDI software also performs this activity in reverse (receives the message and translates from standard format to company-specific format). EDI software can be developed in-house or it can be purchased from a number of commercial software vendors. [page 17] EDI documents are transmitted electronically through phone or data lines from one computer to another. In a direct EDI network the computers of the trading partners are linked directly, usually through dial-up modems. When one of the partners wants to transmit documents to the other, the sender simply dials up the receiving party and transmits the document. [...] A third party network, also known as a value added network or VAN, serves as an intermediary between trading partners. The VAN in the EDI world is similar to the post office in the paper world. [...] A VAN maintains a mailbox for both the sender and the receiver. In this way, if a company has a large number of electronic purchase orders to send to different sellers, the company would transmit all of the purchase orders to the VAN in a single connect or call. |
The source is given, but the passage should be in quotation marks. These sentences are intermingled with Parfett (1992), see Fragment 037 17. |
| [79.] Svr/Fragment 037 17 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 37, Zeilen: 17-18, 21-29 |
Quelle: Parfett 1992 Seite(n): 59, 61, Zeilen: 59: last 6 lines; 61: 7 ff., last paragraph |
|---|---|
| VANs comprise two components, a network and an application. [...] The application provides added value to data network and allows users to purchase facilities as electronic mail, on-line database access, and EDI. (Emmelhainz 1990: 17).
VANs offer different Services: (i) Network Services: Connects Network Services and has high level of security and systems resilience. (ii) Post/ Mailbox Services: Often referred to having 'clearing house' or 'store and forward' functions. (iii) Enabling Software Services: VAN suppliers will often also offer software, both to make connection to the network and to convert in-house document standards to and from an adopted trade standard. |
[page 59]
VANs comprise two components:
The application provides added value to data networks and allows users to purchase facilities such as electronic mail, on-line database access, and EDI. [page 61] The following services are typical of those provided by VAN suppliers: Network Service A network service connects trading partners and has high levels of security and systems resilience, and may provide multiple routing paths and physical links. Postbox/Mailbox Service This service is often referred to as the central ‘clearing house’ or ‘store-and-forward’ function of the third-party VAN network. [...] The VAN supplier will often also offer software, both to make connection to the network and to convert in-house document standards to and from an adopted trade standard. |
The actual source is given at the end of the page; but it is not made clear, that most of the text is copied literally. The reference to Emmelhainz (1990) is misleading, since this text cannot be found there. These sentences are intermingled with ones documented at Fragment 037 01 which are from that source. |
| [80.] Svr/Fragment 038 01 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 38, Zeilen: 1-6, 10-23, 28-32 |
Quelle: Ritz 1995 Seite(n): 51, 52, 53, Zeilen: 51: 7 ff.; 52: 1, 13 ff.; 53: 1 ff. |
|---|---|
| 3.1.5 Cost of setting up and [sic] EDI network
Because of the organizational gap, and EDI network cannot start right away, but requires an initiative to be launched to close the gap. The first contributors to the collective action, i.e. the initiators of an EDI network, do not only have to plan, design, and implement the required techno-organizational infrastructure and the related services, but they also have to bear the associated costs. [There are different cost categories such as: (1) Coordination costs of a new network, (2) Implementation costs of a new network, (3) Individual expenses, and (4) Opportunity costs (Ritz 1995: 51-52).] The set-up process of a coordination and a subsequent implementation stage. During the coordination stage, the network's future characteristics are determined, and plans to implement the specified conception are drawn up. The subsequent implementation of the network infrastructure yields even higher costs for the organizations involved in the collective action at that stage. Infrastructure investments foremost include the direct capital cost of acquiring the systems hard- and software, the highering of staff to operate and market it, the provision of facilities to house the system, etc. Moreover, the cost of establishing an intermediary organization may also be subsumed under this heading. Depending on the scope of this project and the situation at the outset in terms of pre-existing technical infrastructure and standards, the implementation of the network infrastructure may entail altogether substantial costs to the initiators. Some of these investments may actually represent sunk costs that display asset-specificity. [...] Beside the cost of implementing of the communication infrastructure, initial contributors to the collective action will have to carry the individual expenses of joining the network as participants. Usually, an organization that decides to participate in an EDI network needs to invest in its internal hard- and software, e.g. by purchasing converter software and by adapting business applications to the [communication requirements of the clearing center.] Ritz, D. 1995, The start-up of an EDI Network: A comparative case study for the air cargo industry, Dissertation, Hochschule für Wissenschaft-, Recht- u. Sozialwissenschften [sic] St. Gallen. |
[page 51]
2.3.2 The cost of setting up an EDI network It has been shown earlier17 that because of the organizational gap, an EDI network cannot start right away, but requires an initiative to be launched to close that gap. The first contributors to the collective action, i.e. the initiators of an EDI network, do not only have to plan, design, and implement the required techno-organizational infrastructure and the related services, but they also have to bear the associated costs. Cost categories As mentioned earlier, the set-up process of an EDI network encompasses a coordination and a subsequent implementation stage. During the coordination stage, the network's future characteristics are determined, and plans to implement the specified 17See chapter A 1.2. [page 52] conception are drawn up. [...] The subsequent implementation of the network infrastructure yields even higher costs for the organizations involved in the collective action at that stage. Infrastructure investments foremost include the direct capital cost of acquiring the system's hard- and software, the hiring of staff to operate and market it, the provision of facilities to house the system, etc. Moreover, the cost of establishing an intermediary organization may also be subsumed under this heading. Depending on the scope of the project and the situation at the outset in terms of pre-existing technical infrastructures and standards, the implementation of the network infrastructure may entail altogether substantial costs to the initiators.18 Some of these investments may actually represent sunk costs19 that display asset-specificity, i.e. "nontrivial investments in transaction-specific assets." (Williamson 1985, pp. 30). Besides the costs related to the implementation of the common infrastructure, initial contributors to the collective action additionally have to carry the individual expenses of joining the network as participants, if applicable.20 Usually, an organiza- 18The direct capital cost for developing the technical infrastructure of Singapore's TradeNet, for instance, amounted to more than $20 million. This sum does not include the investment made by the involved governmental bodies in conceiving the project, managing the development, or establishing Singapore Network Services (SNS) as intermediary organization (King and Konsynski 1990). 19For a discussion of sunk cost from an accountancy perspective, see e.g. Luther (1992). Rosenbaum (1992) provides an economic analysis of entry, barriers, exit, and sunk costs. 20This applies primarily to community members as initiators. A third-party service provider leading an EDI initiative, on the other hand, will obviously not join the network as a participant. Its role in the diffusion stage will thus be limited to acting as an intermediary. [page 53] tion that decides to participate in an EDI network needs to invest in its internal hard- and software systems, e.g. by purchasing converter software and by adapting business applications to the communications requirements of the clearing center. King, J.L. and Konsynski, B. (1990) Singapore TradeNet. A tale of one city, Nl-191-009, Harvard Business School, Boston, MA, 1990. Luther, R.G. (1992) Fixed costs and sunk costs in decision-making, in: Management Accounting, Vol. 70, 1992, pp. 37, 42. Rosenbaum, D. I. (1992) Entry, barriers, exit, and sunk costs. An analysis, in: Applied Economics, Vol. 24, 1992, pp. 297-304. Williamson, O.E. (1975) Markets and hierarchies. Analysis and antitrust implications, London, 1975. |
The source is given, but it is not made clear that the text is so closely and extensively copied. |
| [81.] Svr/Fragment 039 01 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 39, Zeilen: 1-3, 5-32 |
Quelle: Ritz 1995 Seite(n): 53, 54, Zeilen: 53: 3 ff.; 54: 1 ff. |
|---|---|
| At an organization level, internal business processes may have to be re-shaped in order to be able to interface with trading partners and to reap the full benefits from electronic trading. [Also, retraining of employees are affected by innovations. (Ritz 1995: 52-53).]
Last but not least, opportunity costs also have to be mentioned in this context. Those arise from the uncertainties associated with the collective action of establishing and EDI network. Should EDI initiative fail for the lack of attracting sufficient participants, investments in the joint infrastructure will be al least partly be sunk costs. Furthermore the giving up of established forms of trade data exchange when joining an EDI network also yields opportunity costs from the perspective of an individual participant (Ritz 1995: 53). Risk of Sunk Costs: A very large proportion of the investments in the joint infrastructure outlined above have to be made up-front. Coordination costs arising during the process of determining the network's future characteristics and planning it's implementation. Hard- and software systems have to be acquired and installed before trial operations may begin. Intermediary organizations need to be founded and incorporated before the diffusion process starts. Once the network infrastructure is established, the marginal cost of adding trading partners is comparably low from an initiator's perspective. The reason is that the infrastructure represents fixed costs. Increasing trading volume augments total costs only slightly. As a consequence, unit cost per transaction falls, leading to significant cost based economics of scale. The danger of competing EDI initiatives superseding a focal network is very high at that early stage, and so are the related opportunity costs. The reason is the inherent uncertainty of whether a sufficiently large number of network participants will be attracted to guarantee the success of the collective action. As the number of network participants increases, i.e. as the point of critical mass is being approached, the risk of failure decreases. This leads to a stabilization of expectations among community members, which in turn attracts additional participants and enables the self-sustained growth of an EDI network. For the same set of reasons, the opportunity cost of an individual organization, that has to give up and established platform of trading partner communication, are high at that early stage (Ritz 1995:53-54). Ritz, D. 1995, The start-up of an EDI Network: A comparative case study for the air cargo industry, Dissertation, Hochschule für Wissenschaft-, Recht- u. Sozialwissenschften [sic] St. Gallen. |
At an organizational level, internal business processes may have to be re-shaped in order to be able to interface with trading partners and to reap the full benefits from electronic trading. [...]
Last but not least, opportunity costs also have to be mentioned in this context. Those arise from the uncertainties associated with the collective action of establishing an EDI network. Should an EDI initiative fail for the lack of attracting sufficient participants, either because the design was not accepted by community members, or because it was superseded by a rivalling solution, investments in the joint infrastructure will at least partly be in vain. Furthermore, the giving up of established forms of trade data exchange when joining an EDI network also yields opportunity costs from the perspective of an individual participant (Monse and Reimers 1993). Arising costs in a temporal perspective A very large proportion of the investments in the joint infrastructure outlined above have to be made up-front. Coordination costs arise during the process of determining the network's future characteristics and planning its implementation; hard- and software systems have to be acquired and installed before trial operations may begin; intermediary organizations need to be founded and incorporated before the diffusion process starts, etc. Once the network infrastructure is established, however, the marginal cost of adding trading partners is comparably low from an initiator's perspective. The reason is that the infrastructure represents fixed costs. Increasing transaction volume augments total costs only slightly. As a consequence, unit cost per transaction falls, leading to significant cost-based economies of scale (see also Sheldon 1993). The danger of competing EDI initiatives superseding a focal network is very high at that early stage, and so are the related opportunity costs. The reason is the inherent uncertainty of whether a sufficiently large number of network participants will be attracted to guarantee the success of the collective action. As the number of network [page 54] participants increases, i.e. as the point of critical mass is being approached, the risk of failure decreases. This leads to a stabilization of expectations among community members, which in turn attracts additional participants and enables the self-sustained growth of an EDI network (Schneider 1993).21 For the same set of reasons the opportunity costs of an individual organization, which has to give up an established pattern of trading partner communication, are high at that early stage, too. Monse, K. and Reimers, K. (1993) The development of electronic data interchange networks from an institutional perspective, Paper presented at the EDI/IONS PICT-COST Workshop, Edinburgh, April 15-16, 1993. Schneider, V. (1993) Networks and games in large technical systems. The case of Videotex, in: Scharpf, F.W. (ed.) Games in hierarchies and networks. Analytical and empirical approaches to the study of governance institutions, Frankfurt/M.: Campus, 1993, pp. 251-286. Sheldon, P. (1993) Destination information systems, in: Journal of Tourism Research, Vol. 20, 1993, pp. 633-649. |
The source is given twice, but it is not made clear that the text is so closely and extensively copied. |
| [82.] Svr/Fragment 040 04 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 40, Zeilen: 4-8 |
Quelle: Ritz 1995 Seite(n): 55, Zeilen: 23 ff. |
|---|---|
| In contrast to the cost of setting up an EDI network, which is predominantly arises upfront, economic benefits start to occur only during the diffusion stage. The reason is that all three categories of benefits described below are positively related to the size of an EDI network in terms of subscribers (Ritz 1995: 55).
Ritz, D. 1995, The start-up of an EDI Network: A comparative case study for the air cargo industry, Dissertation, Hochschule für Wissenschaft-, Recht- u. Sozialwissenschften [sic] St. Gallen. |
In contrast to the cost of setting up an EDI network, which predominantly arises upfront, economic benefits start to accrue only during the diffusion stage. The reason is that all three categories of benefits described above are positively related to the size of an EDI network in terms of subscribers. |
The source is given, but without quotation marks. |
| [83.] Svr/Fragment 040 09 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 40, Zeilen: 9-29 |
Quelle: Parfett 1992 Seite(n): 2, 12, 13, 17, Zeilen: 2: 13 ff.; 12: last 5 lines; 13: 5 ff.; 17: 2 ff. |
|---|---|
| EDI investment projects used to be justified on the basis of savings on postal charges and processing charges alone, and figures were calculated from the amount saved on every order raised or invoice processed. But time and EDI have moved on. There is a greater realization that EDI is just an enabler, and the mayor benefits that derive from the use of today's computer and telecommunications revolution will be in the change in business relationships and practices that use of timely and accurate information can bring (Parfett 1992: 2).
Parfett (1992: 12-13) concludes from a survey that the most important arguments for implementing EDI are: - Strategic benefits - To increase the competitive edge (68%): Of crucial, longterm significance to the functioning of the organization. These benefits will affect the very business the company is undertaking, i.e. its central operating function. - Operational benefits - To reduce costs (56%): Of mayor importance to daily operations of the company, usually only impacting on certain department within the organization. Benefits from future opportunities - To provide new business opportunities (45%): EDI is not necessarily seen to be crucial to the current operations of the company, but as offering potential future benefits. The list of opportunity benefits includes such factors as enhanced image and competitive edge, which although perceived as beneficial, are difficult to quantify. |
Justification for EDI was on the basis of savings on postal charges and processing charges alone and figures were calculated for the amount saved on every order raised or invoice processed. But time and EDI have moved on. There is a greater realisation that EDI is just an enabler and the major benefits derived from the use of today’s computer and telecommunications revolution will be in the changes in business relationships and practices that use of timely and accurate information can bring.
[page 12] The most important ones cited were: - to increase competitive edge 68% of respondents - to reduce costs 56% - to provide new businessopportunities 45% [page 13]
- Operational
- Opportunity
[page 17] The list of opportunity benefits includes such factors as enhanced image and competitive edge, which although perceived as beneficial, are difficult to quantify. |
The source is given, but it is not made clear that the text is so extensively similar - no quotation marks. |
| [84.] Svr/Fragment 041 02 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 41, Zeilen: 2-7, 12-13, 17-26 |
Quelle: O'Callaghan Turner 1995 Seite(n): online, Zeilen: 0 |
|---|---|
| The savings come from improvements in a number of areas (O'Callaghan and Turner 1995: 9-11; Seffinga 1996: 15; Parfett 1992:16):
Better use of personnel through reduction in document handling tasks. The savings in document handling are dependant upon how the document was processed prior to EDI. [...] Reduction in other costs such as exception handling and premium freights due to a mistake in a purchase order. [...] Cheaper and more efficient information processing reduces the transaction costs of writing contracts, and monitoring and ensuring secure commitments, thus making external provision of production more attractive. Furthermore an EDI system may reduce the amount of management influence as the routine nature of EDI transactions short circuits many internal operations and thus reduces the necessity for management intervention. 3.2.2 Strategic benefits The implementation of EDI within an organization provides a chance to improve internal operations and even to redesign business processes altogether (Seffinga 1996:15). O'Callaghan, R. & Turner, E. 1995, EDI in Europe: How it works in Practice, West Sussex. Parfett, M. 1992, What is EDI? A Guide to Electronic Data Interchange, 2nd ed., NCC Blackwell Limited, Oxford, England. Seffinga, J. 1996, Electronic Data Interchange (EDI), Stand und Potentiale, Hochschulverlag AG an der ETH Zürich. |
They suggest that cheaper and more efficient information processing reduces the transactions costs of writing contracts, and monitoring and ensuring secure commitments, thus making external provision of production more attractive.
[...] An EDI system may reduce the amount of management influence as the routine nature of EDI transactions short circuit many internal operations and thus reduce opportunities for intervention. [...] The savings come from improvements in a number of areas: reduction in document handling tasks, reduction and/or better use of personnel, reduction in inventories, and reduction in other costs such as exception handling and premium freight (e.g. due to a mistake in a purchase order). The savings in document handling are dependent upon how the document was processed prior to EDI. [...] The implementation of EDI within an organization provides a chance to improve internal operations and even to re-design business processes altogether. The improvements can result from a review of current operations that should precede the implementation of EDI, from the integration of EDI with other systems, from better use of personnel, and from the management of more accurate and timely information. |
The source is given, but quotation marks are missing. |
| [85.] Svr/Fragment 041 09 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 41, Zeilen: 9-11, 15-18 |
Quelle: Parfett 1992 Seite(n): 16, Zeilen: 22 ff., 30 ff. |
|---|---|
| EDI furthermore enables suppliers to send accurate and timely invoices thus a higher proportion of invoices get paid in time.
[...] This includes the elimination of errors in transcribing information from one medium (paper) to another (computer) and the reduces [sic] chance of mismatching orders, ie. fewer good [sic] returned, and a cost reduction in repeat deliveries to put errors right and reduction of redundant work. |
EDI enables suppliers to send accurate and timely invoices. [...] The net result is that a higher proportion of invoices get paid on time.
[...] This includes the elimination of errors in transcribing information from one medium (paper) to another (computer) and the reduced chance of mismatching orders, ie fewer goods returned, and a reduction in repeat deliveries to put errors right. |
The source is given some lines above, but it is not made clear that the content is literally copied from there, as there are no quotation marks. |
| [86.] Svr/Fragment 042 01 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 42, Zeilen: 1-5, 14-19 |
Quelle: Parfett 1992 Seite(n): 14, 19, Zeilen: 14: 19 ff.; 19: 29 ff. |
|---|---|
| [EDI facilitates the adoption of these JIT techniques by providing the timely and] accurate information required on a daily basis, whilst promoting the trust and commitment required on a long-term basis (Parfett 1992: 14).
Higher bargaining power: In a highly competitive market, EDI can be useful as it provides the ability to offer significant cuts in product delivery time, which may be the difference between winning and loosing a contract. (Parfett 1992: 14). [...] 3.3.1 Limited number of standard EDI documents defined The development of EDI standards is crucial to the widespread adoption of this form of trading. The foundations to a truly international set of documents standards have been laid in the form of the EDIFACT syntax standard. However, the number of fully approved EDIFACT messages is still small and proprietary subsets or even supersets are often used (Parfett 1992: 19). |
EDI facilitates the adoption of these JIT techniques by providing the timely and accurate information required on a daily basis, whilst promoting the trust and commitment required on a long-term basis. [...]
Terms of trade dictated by bargaining power In a highly competitive market, EDI can be a powerful weapon in a company’s corporate armoury. The ability to offer significant cuts in product delivery time may be the difference between winning and losing a contract. [page 19] - Limited number of standard EDI documents defined.
|
The source is given three times, but no quotation marks are used. |
| [87.] Svr/Fragment 042 07 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 42, Zeilen: 7-9, 20-30 |
Quelle: Norman 1999 Seite(n): 44, Zeilen: 15 ff. |
|---|---|
| [3.3. Barriers for EDI penetration]
One of the major problems with the current implementations of EDI is that they often require a unique solution for each pair of trading partners, making EDI costly and time-consuming to implement. [...] [3.3.1 Limited number of standard EDI documents defined] [...] Another problem with traditional EDI is that it is based on the use of rigid transaction sets with business rules embedded in them. These transaction sets are defined by standards bodies such as the United Nations Standards Messages Directory for Electronic Data Interchange for Administration, Commerce, and Transport (UN/EDIFACT) and American National Standards Institute’s Accredited Standards Committee X12 sub-group (ANSI X12). Transaction sets define the fields, the order of these fields, and the length of the fields. Along with these transactions sets there are business rules, which in EDI-language are referred to as implementation guidelines (United Nations 1999 and ASC12 1999). A fixed transaction set prevents companies from evolving by adding new services and products or changing business processes. The bodies that make the standard [transaction sets are ill equipped to keep up with the rapid pace of change in the various business environments they impact.] ASC12 (eds). 1996, Data International Standards Association (DISA), [Online]. Available: http://polaris.disa.org/ United Nations, Rules for Electronic Data Interchange for Administration, Commerce, and Transport (EDIFACT), [Online]. Available: http://www.unece.org/trade/untdid/welcom1.htm |
One of the major problems with the current implementations of EDI is that they often require a unique solution for each pair of trading partners, making EDI costly and time-consuming to implement.
Another problem with traditional EDI is that it is based on the use of rigid transaction sets with business rules embedded in them. These transaction sets are defined by standards bodies such as the United Nations Standards Messages Directory for Electronic Data Interchange for Administration, Commerce, and Transport (UN/EDIFACT) [30] and American National Standards Institute’s Accredited Standards Committee X12 sub-group (ANSI X12) [32]. Transaction sets define the fields, the order of these fields, and the length of the fields. Along with these transactions sets are business rules, which in EDI-language are referred to as “implementation guidelines”. [...] A fixed transaction set prevents companies from evolving by adding new services and products or changing business processes. The bodies that make the standard transaction sets are ill equipped to keep up with the rapid pace of change in the various business environments they impact. [30] Rules for Electronic Data Interchange for Administration, Commerce, and Transport (EDIFACT) [32] Data International Standards Association (DISA) |
The actual source is not given. |
| [88.] Svr/Fragment 043 01 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 43, Zeilen: 1-3 |
Quelle: Norman 1999 Seite(n): 44, Zeilen: 30 ff. |
|---|---|
| [The bodies that make the standard] transaction sets are ill equipped to keep up with the rapid pace of change in the various business environments they impact. It is also very hard, if not impossible, to develop a one-size-fits-all solution. | The bodies that make the standard transaction sets are ill equipped to keep up with the rapid pace of change in the various business environments they impact. It is also very hard, if not impossible, to develop a one-size-fits-all solution. |
Continued from previous page. The source ist not given. |
| [89.] Svr/Fragment 043 10 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 43, Zeilen: 10-16, 17-24 |
Quelle: Parfett 1992 Seite(n): 2, 19, 20, Zeilen: 2: 25 ff.; 19: 22 ff.; 20: 1, 4 ff. |
|---|---|
| It is symptomatic of electronic office communications technology that a critical mass of users is required before a 'big bang' style adoption of the techniques is achieved. Potential users must assess whether the population is sufficient for them to realize their investment, and certainly some business are more mature than others in this respect (Parfett 1992: 19-20).
The figures quoted for the number of companies using EDI vary from source to source. [...] The companies using EDI come from a range of business sectors, including retail, manufacturing, transport, construction, finance and the public sector (Parfett 1992: 49). 3.3.3 Legal Problems The legal aspects include the provision of new forms of contract, and deciding when and where the contract is formed. This issue is of particular importance as EDI transactions cross national boundaries. Computer fraud and theft of data need also be addressed (Parfett 1992: 19). |
The figures quoted for the number of companies using EDI seems to vary with every article that you read. [...]
The companies at present using EDI come from a range of business sectors, including retail, manufacturing, transport, construction, finance and the public sector. [page 19]
[...]
[page 20]
|
The source is given three times, but it is not made clear that the text is so extensively similar - no quotation marks are used. |
| [90.] Svr/Fragment 043 26 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 43, Zeilen: 26-29 |
Quelle: Weitzel et al 2000 Seite(n): 1, Zeilen: right col., 10 ff. |
|---|---|
| What is wrong with traditional EDI? Since the late 1960s, especially large enterprises have been using Electronic Data Interchange to expedite the exchange of business documents such as sales orders, invoices etc. In contrast to paper-based communication, EDI is designed to make communication between [different systems possible without media discontinuities.] | But, as one might ask, what is wrong with traditional EDI? Since the late 1960s, especially large enterprises have been using Electronic Data Interchange to expedite the exchange of business documents such as sales orders, invoices etc. In contrast to paper-based communication, EDI is designed to make communication between different systems possible without media discontinuities. |
No source is given. |
| [91.] Svr/Fragment 044 10 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 44, Zeilen: 10-21 |
Quelle: Weitzel et al 2000 Seite(n): 1, 2, Zeilen: 1: right col., 20 ff.; 2: left col., 1 |
|---|---|
| [Both the sending and receiving company gains the ability to fully control and audit the end-to-end business transaction,] yielding time advantages and supporting Just-in-time production.
While this is often true for large enterprises, there is another side to EDI. Presumably, nowadays only 2 - 5% of all companies who could benefit from EDI actually use it. Especially small and mid-sized enterprises often name the high costs of implementing and running EDI as dissuading factors, and a current empirical study found pressure from larger business partners to be among the main reasons for the implementation of EDI. Furthermore, many of today’s solutions are platform dependent, meaning additional investments in both, hardware and software. Thus, EDI is predominantly implemented by large firms, preventing the electronic processing of data flowing through entire supply chains in open networks. Generally speaking, traditional EDI lacks the flexibility and efficiency required for state of the art electronic business. |
Hailed as a strategic competitive advantage, a look at the literature paints EDI as the „killer application“ for B2B communication, promising cost reductions in the millions, yielding time advantages and supporting Just in Time production [6]. While this is often true for large enterprises, there is another side to EDI. Presumably, nowadays only 5% of all companies who could benefit from EDI actually use it [7]. Especially small and mid-sized enterprises (SMEs) often name the high costs of implementing and running EDI as dissuading factors, and a current empirical study found pressure from larger business partners (“gun-to-the-head-EDI”) to be among the main reasons for the implementation of EDI [10]. Furthermore, many of today’s solutions are platform dependent, meaning additional investments in both, hardware and software. Thus, EDI is predominantly implemented by large firms, preventing the electronic processing of data flowing through entire supply chains in open networks. Generally speaking, traditional EDI lacks the flexibility and efficiency required for state of the art electronic business.
[6] Emmelhainz, M.: (1993): EDI – A Total Management Guide, 2nd edition, New York [7] Segev, A./Porra, J./Roldan, M. (1997): Internet-based EDI Strategy, Working Paper 10-21, Fisher Center of Management and Information Technology, University of California Berkeley; http://haas.berkeley.edu/~citm/wp-1021.pdf [10] Westarp, F. v./Weitzel, T./Buxmann, P./König, W.(1999): The Status Quo and the Future of EDI, in: Proceedings of the 1999 European Conference on Information Systems (ECIS’99) |
No source is given. |
| [92.] Svr/Fragment 045 17 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 45, Zeilen: 17-19 |
Quelle: Weitzel et al 2000 Seite(n): 2, Zeilen: left col., 25 ff. |
|---|---|
| The term Web/EDI, also referred to as Form-based EDI, describes the use of the WWW as the basis for both, EDI applications and the transfer of business documents. | The term WebEDI describes the use of the WWW as the basis for both, EDI applications and the transfer of business documents. |
No source is given. |
| [93.] Svr/Fragment 045 23 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 45, Zeilen: 23-27, 29-31 |
Quelle: Weitzel et al 1999 Seite(n): online, Zeilen: 0 |
|---|---|
| Existing solutions generally offer an HTML input mask, which allows the manual input of structured data, similar to the HTML frontend to a shopping system. Thus, there is no machine-to-machine connection and no way the client, usually the smaller partner, can import the EDI data into his inhouse systems.
[...] The obvious advantage of using the Web as a medium for EDI communication is that the only (client side) prerequisite is an Internet connection and a Web browser. |
More important, WebEDI is mostly no more than an HTML-front-end to a shopping system. A user manually enters data into a form using a webbrowser as communication interface. Thus, there is no machine-to-machine connection and no way the client, i. e. the small partner, can import the EDI data into his inhouse systems.
The obvious advantage of using the Web as a medium for EDI communication is that the only (client side) prerequisite is an Internet connection and a webbrowser. |
No source is given. |
| [94.] Svr/Fragment 046 05 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 46, Zeilen: 5-14 |
Quelle: Edwards 1999 Seite(n): online, Zeilen: 0 |
|---|---|
| One pioneer of Web/EDI is Wal-Mart Stores, Inc., which has extended its private EDI network to its entire trading community using an Internet-based system. Wal-Mart has also given the required client software to several thousand smaller suppliers, who can now receive purchase orders via the Internet and send back invoices simply by completing a Web-based form. The invoices are filtered through a server at Wal-Mart headquarters and integrated into the company's existing EDI system. Like Wal-Mart, many of the Fortune 1000 companies that have made large investments in EDI are unlikely to abandon it anytime soon. Instead, they will probably use Internet-based EDI to augment their existing infrastructure and allow smaller companies to join the trading community and share in its benefits. | One pioneer of the shift to Web-based EDI is Wal-Mart Stores, Inc., which has extended its private EDI network to its entire trading community using an Internet-based system. Wal-Mart has also given the required client software to several thousand smaller suppliers.
Using Harbinger's TrustedLink Express, trading partners can now receive purchase orders via the Internet and send back invoices simply by completing a Web-based form. The invoices are filtered through a server at Wal-Mart headquarters and integrated into the company's existing EDI system. Like Wal-Mart, many of the Fortune 1000 companies that have made large investments in EDI are unlikely to abandon it anytime soon. Instead, they will probably use Internet-based EDI to augment their existing infrastructure and allow smaller companies to join the trading community and share in its benefits. |
No source is given. |
| [95.] Svr/Fragment 046 16 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 46, Zeilen: 16-17, 23-32 |
Quelle: Norman 1999 Seite(n): 44, 45, Zeilen: 44: last paragraph; 45: 26 ff. |
|---|---|
| [3.4.3 XML/EDI]
By using XML to implement EDI many of the old problems of EDI (as discussed in previous chapter) are eliminated. [...] XML therefore maintains the content and structure, but separates the business rules from the data. By focusing on exchanging data content and structure, trading partners can apply their own business rules. Using XML it is also very easy to extend the communication to support new business processes, EDI will no longer be limited to rigid standards. The fact that XML documents can easily be distributed using the Internet is another major advantage. This combined with the fact that XML is self-explaining provides the entire framework for what the XML/EDI group calls a new supply web. Earlier many EDI implementations only worked within their own Intranets. With XML this is no longer the case since XML provides connectivity through the [Internet.] |
3.4.2 EDI using XML
By using XML to implement EDI many of the old problems are eliminated. XML maintains the content and structure, but separates the business rules from the data. By focusing on exchanging data content and structure, trading partners can apply their own business rules. Using XML it is also very easy to extend the communication to support new business processes, EDI will no longer be limited to rigid standards. [page 45] The fact that XML documents can easily be distributed using the Internet is another major advantage. This combined with the fact that XML is self-explaining provides the entire framework for what the XML/EDI group calls a new “supply web”. Earlier many EDI implementations only worked within their own Intranets. With XML this is no longer the case since XML provides connectivity through the Internet. |
The source is not given. |
| [96.] Svr/Fragment 046 17 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 46, Zeilen: 17-21 |
Quelle: Raman 1998 Seite(n): online, Zeilen: 0 |
|---|---|
| The XML tags can actually replace existing EDI segments or data-element identifiers, which produce a somewhat bigger file than an EDI file (before compression), but in which all the labels of the data elements (in other words the description or the explanations) can optionally be used as XML tag names. | The XML tags can actually replace existing EDI segments or data-element identifiers, which produces a somewhat bigger file than an EDI file, but in which all the labels of the data-elements (in other words the descriptions or explanations) are included as well. |
No source is given. |
| [97.] Svr/Fragment 047 01 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 47, Zeilen: 1-4 |
Quelle: Norman 1999 Seite(n): 45, Zeilen: 29 ff. |
|---|---|
| All applications are then able to communicate and exchange data, thus the old point-to-point solutions are history. To many people XML/EDI is also what they call a politically correct way to merge ANSI X12 (the US standard) and EDIFACT (the international standard). | All applications are then able to communicate and exchange data, thus the old point-to-point solutions are history. To many people XML-EDI is also what they call a ‘politically correct’ way to merge ANSI X12 (the US standard) and EDIFACT (the world standard). |
Continued from the previous page. The source is not given. |
| [98.] Svr/Fragment 047 12 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 47, Zeilen: 12-18, 21-30 |
Quelle: Weitzel et al 2000 Seite(n): 2, Zeilen: left col., 36 ff.; right col., 1 ff. |
|---|---|
| Web/EDI proves to be a good idea for large companies seeking ways of having their small customers send their data in a standardized format without forcing them to invest large amounts of money (Weitzel et al. 1999b). But in order to procure the exchange of information throughout the entire supply chain, the solutions need to be more flexible. While Web/EDI is a means of integrating small partners into existing sub-networks, the emergence of new electronic marketplaces required the transformation of "supply chains" into "supply Webs".
[...] As opposed to traditional EDI, where communication flows over private Value Added Networks, the Internet is a public network and there are serious security issues to be considered. Although more than 50% of the Fortune1000 enterprises in both, Germany and the U.S. plan to use Web/EDI in the future, it is so far only implemented by 7.4% in Germany and 16.9% in the U.S (Westarp et al.1999). Questionable security is, by far, the greatest stumbling block to widespread use of the Internet for EDI. Given these considerations, compared to traditional EDI a state of the art Web/EDI solution must meet the following five requirements: (a) lower setup costs and time, (b) reduced operating costs, (c) security, (d) easy integration in in-house systems especially of the smaller partners (clients), and (e) flexibility and extensibility (Weitzel and Buxmann 1999). Weitzel, T. & Buxmann, P. 1999, A communication architecture for the digital economy: 21st century EDI Weitzel, T., Buxmann, P., Kronenberg, R., & Ladner, F. 1999b, XML/EDI: The (r)evolution of EDI, Institute of Information Systems, Working Paper 99-10, [Online]. Avaliable: http://www.wiwi.uni-frankfurt.de/~tweitzel/XMLEDI.doc Accessed: October 29 1999. Westarp, F. V., Weitzel, T., Buxmann, P., & König, W. 1999, “The Status Quo and the Future of EDI”, Proceedings of the 1999 European Conference on Information Systems (ECIS’99), [Online]. Available: |
In this context, form-based EDI proves to be a good idea for large companies seeking ways of having their small customers send their data in a standardized format without forcing them to invest large amounts of money [8]. But in order to procure the exchange of information throughout the entire supply chain, the solutions need to be more flexible. While form-based EDI is a means of integrating small partners into existing sub-networks, the emergence of new electronic marketplaces, or as CommerceOne calls it the transformation of “supply chains” into “supply Webs” [9], requires a greater flexibility, e. g. enabling an easy alteration of transaction content and partners as well as fast and easy integration into in-house systems. Additionally, there are serious security issues to be considered. Although more than 50% of the Fortune1000 enterprises in both, Germany and the U.S. plan to use WebEDI in the future, it is so far only implemented by 7.4% in Germany and 16.9% in the U.S [10]. Questionable security is, by far, the greatest stumbling block to widespread use of the Internet for EDI.
Given these considerations, compared to traditional EDI a state of the art WebEDI solution must meet the following five requirements:
[8] Weitzel, T./Buxmann, P./Kronenberg, R./Ladner, F. (1999): XML/EDI - the (r)evolution of EDI, Institute of Information Systems WP 99-10, http://www.wiwi.unifrankfurt.de/~tweitzel/XMLEDI.doc [9] Glushko, R./Tenenbaum, J./Meltzer, B. (1999): An XML Framework for Agent-based E-commerce, in: Communications of the ACM, Vol. 42, No. 3 (March 1999), p. 106-114 [10] Westarp, F. v./Weitzel, T./Buxmann, P./König, W. (1999): The Status Quo and the Future of EDI, in: Proceedings of the 1999 European Conference on Information Systems (ECIS’99) |
The actual source is given, but neither does it become clear that the text is copied literally, nor which portions have been taken from the source. |
| [99.] Svr/Fragment 048 01 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 48, Zeilen: 1-14 |
Quelle: Houser et al 1996 Seite(n): 5, 6, Zeilen: 5: 22 ff.; 6: 1 ff. |
|---|---|
| In spite of the security aspect, the greatest benefits of the Internet for EDI will derive from:
- Adoption of common standards and proven inter-operable systems. - Adoption and deployment of a distributed Directory Service capability, so that one can readily contact electronically any other organization in the world. - Explicit commitment by participating organizations to cooperatively route traffic, work to resolve addresses, and meet required standards. - Ubiquitous (anytime, anywhere) network coverage from many service providers. This allows the customer to choose the level of service needed. - Layering of applications (such as EDI) over existing, proven, applications. - A standards process with reference implementations which all vendors have equal access. - Widely available public domain software including but not limited to applications, protocol/transports and multiple platform development tools. |
The greatest benefits will derive from:
[page 6]
|
No source is given. |
| [100.] Svr/Fragment 048 19 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 48, Zeilen: 19-21, 23-27 |
Quelle: ECOOP 2001 Seite(n): online, Zeilen: 0 |
|---|---|
| [4. XML/EDI]
The growth of the Internet and the expansion of e-commerce systems have accentuated pre-existing problems related with systems interoperability and the definition of common semantics throughout business organizations. [...] The issues involved, however, are not just related to infrastructure and technology. Fundamental problems exist around the understanding of what concepts are shared, how they relate and what mechanisms should be adopted to allow systems to communicate and interoperate at all levels. |
[Call For Papers]
The growth of the Internet and the widespread of e-commerce systems have accentuated pre-existing problems related with systems interoperability and the definition of common semantics throughout business organisations. [...] The issues involved are not just related to infrastructure and technology. Indeed fundamental problems exist around the understanding of what ‘concepts’ are shared, how they relate and what mechanisms should be adopted to allow systems to communicate and interoperate at all levels. |
The source is not given. |
| [101.] Svr/Fragment 048 28 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 48, Zeilen: 28-32 |
Quelle: Webber 1998 Seite(n): 40, Zeilen: left col., 2 ff.; right col., 11 ff. |
|---|---|
| XML/EDI provides 100% backward compatibility to existing EDI transactions, while moving EDI forward to the next generation. This means that it will not be necessary to discard the investment in existing EDI systems and knowledge (Webber 1998a: 40) But simply redefining message format to make the web deployable for EDI is not enough of itself.
Webber, D. 1998a, “Introducing XML/EDI Frameworks”, Electronic Markets, vol. 8, no.1, pp38-41. |
Simply redefining the message format to make it Web deployable is not enough of itself.
[...] XML/EDI provides 100% backward compatibility to existing EDI transactions, while moving EDI forward to the next generation. This means we do not have to discard the investment in existing EDI systems and knowledge. |
The source is given, but the quotation marks are missing. |
| [102.] Svr/Fragment 049 01 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 49, Zeilen: 1-6 |
Quelle: ECOOP 2001 Seite(n): online, Zeilen: 0 |
|---|---|
| [Genericity mechanisms, such as] patterns, frameworks and components, have the potential for defining, modeling, designing, and implementing shared concepts. Such mechanisms have inherited many object-oriented principles and built upon them to enhance the generalized nature of business problems and solutions both vertically (within the same domain) and horizontally (across different domains). Increasingly, emerging ontological definitions and related languages like XML supports these mechanisms. | Genericity mechanisms, such as patterns, frameworks and components, have the potential for defining, modelling, designing and implementing shared concepts. Such mechanisms have inherited many object-oriented principles and built upon them to enhance the generalised nature of business problems and solutions both vertically (within the same domain) and horizontally (across different domains). Increasingly, these are supported by emerging ‘ontological’ definitions and related languages (e.g. XML) designed to exemplify genericity. |
The source ist not given. |
| [103.] Svr/Fragment 049 13 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 49, Zeilen: 13-19 |
Quelle: Peat Webber 1997 Seite(n): online, Zeilen: 0 |
|---|---|
| By using the XML extensible tag set, EDI objects can be either passed or dynamically referenced [sic] to objects stored in repositories. The XML/EDI Group (see chapter 4.1.4. and Appendix) is proposing the use of XML as a carrier for the document information so that the transaction can carry not only data, but also code (at each level in the transaction tree). With an element having data properties and code methods, this allows the business elements to be manipulated as objects. | By using the XML extensible tag set, EDI "objects" can be either passed or dynamically reference to objects stored in repositories. The XML/EDI Group is proposing the use of XML as a "carrier" for the document information so that the transaction can carry not only data (like trad-edi), but also code (at each level in the transaction tree). With an element having data properties and code methods, this allows the business elements to be manipulated as "objects". |
No source is given. |
| [104.] Svr/Fragment 049 24 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 49, Zeilen: 24-30 |
Quelle: Webber 1998 Seite(n): 40, Zeilen: left col., 4 ff. |
|---|---|
| Classic EDI is captive to its own fixed structures and inflexibility. To save XML/EDI suffering this same fate, the XML/EDI guidelines proposed by the XML/EDI Group adds three additional key components: Process Templates, Software Agents, and Global Entity Repositories (Webber 1998a: 40).
These three additional components transform old EDI into XML/EDI that allows full dynamic e-commerce between business partners and avoids the mistakes of the past. Each component adds unique tools that leverage the other pieces to make [XML/EDI a dynamic process that can be infinitely extended.] Webber, D. 1998a, “Introducing XML/EDI Frameworks”, Electronic Markets, vol. 8, no.1, pp38-41. |
Old style EDI is captive to its own fixed structures and inflexibility. To save XML/EDI suffering this same fate, the XML/EDI Guidelines proposed by the XML/EDI Group adds three additional key components:
+ process Templates, + software Agents, + and Global Entity Repositories. These three additional components transform old EDI into XML/EDI that allows full dynamic Electronic Commerce between business partners and that avoids the mistakes of the past. Each component adds unique tools that leverage the other pieces. In the past EDI was very static, what XML/EDI provides is an exciting dynamic process that can be infinitely extended. |
The source is given, but there are no quotation marks. It does not become clear to what extent text is copied nor that it is a literal copy. |
| [105.] Svr/Fragment 050 01 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 50, Zeilen: 1-5 |
Quelle: XML EDI Group 1999 Seite(n): online, Zeilen: 0 |
|---|---|
| The combination of XML and EDI semantic foundation will provide a complete framework where a set of different technologies work together to create a format that is usable by applications as well as humans. These components all work together to create an XML framework for business use (Peat and Webber, 1999).
Peat, B. & Webber, D. August 1997, XML/EDI: The E-business Framework, [Online]. Available: http://www.geocities.com/WallStreet/Floor/5815/startde.htm |
WHAT ARE XML REPOSITORIES?
The combination of XML and EDI semantic foundations, called XML/EDI, will provide a complete framework where a set of different technologies work together to create a format that is usable by applications as well as humans. [...] These components all work together to create an XML framework for business use: |
This text is not found in the archived version of Peat Webber 1997 (or 1999). The text is almost identical to an excerpt of a document linked from a page given in the bibliography as "XML/EDI Repository Group (eds). 1999a". |
| [106.] Svr/Fragment 050 11 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 50, Zeilen: 11-19 |
Quelle: Peat Webber 1997 Seite(n): online, Zeilen: 0 |
|---|---|
| [- XML (transport, metadata, parsing)
- EDI (business transactions) - Repositories (business process entities) - Templates (business rules & information exchange) - Agents (control and facilitation)]
XML itself provides the foundation. The Web was born on the abilities of the HTML language, itself a very limited subset of the original and highly complex SGML document syntax. Now XML has been created that sits between the two, not as complex as SGML, but vastly more capable than HTML. XML tokens and frameworks are the syntax that transports the other components across the network. XML tokens replace of [sic] supplement existing segment identifiers. XML also brings with it all the rich capabilities and transport layers of the Web and the Internet in general. EDI is the grandfather of the current e-commerce. Peat, B. & Webber, D. August 1997, XML/EDI: The E-business Framework, [Online]. Available: http://www.geocities.com/WallStreet/Floor/5815/startde.htm |
Each component adds unique tools that leverage the other pieces. In the past EDI was very static, today the XML/EDI framework provides is an exciting dynamic process that can be infinitely extended. We now look at each technology to give you an overview, while later sections provide more in depth looks at each.
Figure 1. XML/EDI the Fusion of Technologies The Power of Five: XML itself provides the foundation. The Web was born on the abilities of the HTML language, itself a very limited subset of the original and highly complex SGML document syntax. Now XML has been created that sits between the two, not as complex as SGML, but vastly more capable than HTML. XML tokens and frameworks are the syntax that transports the other components across the network. XML tokens replace or supplement existing EDI segment identifiers. XML also brings with it all the rich capabilities and transport layers of the Web and the Internet in general. EDI is the grandfather of the electronic commerce. |
The source is given, but no quotation marks are used. Figure 8 appears to be a copy from the source. |
| [107.] Svr/Fragment 050 19 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 50, Zeilen: 19-20 |
Quelle: Norman 1999 Seite(n): 44, Zeilen: 11 ff. |
|---|---|
| Using EDI, it is not necessary for the trading partners to have identical document processing systems. When the [sender sends a document, EDI translation software can convert the proprietary format into an agreed upon standard.] | When you use EDI, it's not necessary for the trading partners to have identical document processing systems. When the sender sends a document, EDI translation software can convert the proprietary format into an agreed upon standard. |
The source is not given. |
| [108.] Svr/Fragment 051 01 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 51, Zeilen: 1-4 |
Quelle: Norman 1999 Seite(n): 44, Zeilen: 12 ff. |
|---|---|
| [When the] sender sends a document, EDI translation software can convert the proprietary format into an agreed upon standard. When the receiver receives the document, his EDI translation software automatically changes the standard format into the proprietary format of his document processing software. | When the sender sends a document, EDI translation software can convert the proprietary format into an agreed upon standard. When the receiver receives the document, his EDI translation software automatically changes the standard format into the proprietary format of his document processing software. |
The source is not given. |
| [109.] Svr/Fragment 051 07 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 51, Zeilen: 7-9, 13-19 |
Quelle: Raman 1998 Seite(n): online, Zeilen: 0 |
|---|---|
| Process Templates are the rules that determine how XML files should be interpreted. They can define the layout of the file and are supplemented by DTDs that enable transaction operability. [...]
Software Agents interpret the templates to perform the job need to be done (such as accessing local data stores), and also interact with the transaction and help the users to create new templates for each specific task (Webber 1998a: 41). Repositories are locations where shared and agreed-upon Internet directories are stored and where users can manually or automatically look up the meaning and definition of XML/EDI Tags. The repository is in fact the semantic foundation for the business transactions (Webber 1999a: [sic] 41). Webber, D. 1998a, “Introducing XML/EDI Frameworks”, Electronic Markets, vol. 8, no.1, pp38-41. |
The templates are essentially rules that determine how the XML files should be interpreted. It can define the layout of the file and is supplemented by DTDs (Document Type Definitions) that enable transaction operability.
The agents can interpret the templates to perform whatever job needs to be done, but they can also interact with the transaction and help the user to create new templates for each specific task. The repository is a location where shared Internet directories are stored and where users can manually or automatically look up the meaning and definition of XML/EDI Tags. The repository is in fact the semantic foundation for the business transactions. |
The actual source is not given. |
| [110.] Svr/Fragment 051 21 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 51, Zeilen: 21-28 |
Quelle: Peat Webber 1997 Seite(n): online, Zeilen: 0 |
|---|---|
| According to Peat and Webber (1999) XML/EDI provides four core models of use. These include traditional EDI deployment methods, along with new documentcentric capabilities. Figure 6 shows at a glance the four core models: (i) Star Model, (ii) Ad-hoc Model, (iii) Hybrid Model, and (iv) Web Model.
The Star-model shown is the classic EDI model, where a major business partner or organization sets the standards for its trading partners. The Ad-hoc-model is the new net-based model. Smaller trading partners setup their own ad hoc interactions, these in time may evolve into more formal methods, or they may not. Peat, B. & Webber, D. August 1997, XML/EDI: The E-business Framework, [Online]. Available: http://www.geocities.com/WallStreet/Floor/5815/startde.htm |
XML/EDI provides four core models of use. These include traditional EDI deployment methods, along with new document-centric capabilities. Figure 2 shows at a glance the four core models.
[...] The "star" model shown is the classic EDI model, where a major business partner or organization sets the standards for its trading partners. The "ad hoc" model is the new net-based model. Smaller trading partners setup their own ad hoc interactions, these in time may evolve into more formal methods, or they may not. |
The source is given but it is not made clear that the text is so extensively copied - no quotation marks. |
| [111.] Svr/Fragment 052 01 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 52, Zeilen: 1 ff. (completely) |
Quelle: Peat Webber 1997 Seite(n): online, Zeilen: 0 |
|---|---|
| The Hybrid-model is a combination of the first two. Here a "Star" model is extended by trading partners, by creating new versions of frameworks, and by linking in their own ad hoc ones. The Web-model is a document-centric model, where content is the most important information being exchanged. Content can either arrive driven by pre-set rules, or be requested, or be broadcast. The classic example for this is an electronic catalog, and the associated Request for Quotations (RFQ) dialogs.
4.1.3 XML/EDI as a Framework XML/EDI provides for the infrastructure of a wide variety of e-commerce systems, from searchable on-line catalogs to robust machine-to-machine transaction subsystems. The XML/EDI initiative is to provide open solutions for implementing e-business systems today, as there is more than just one standard solution for all of the e-business scenarios. Each scenario has its own requirements and goals. Thus a framework and not an application or module is required. The goal of the framework is to provide formal interfaces for commercial e-commerce components to interoperate. For XML/EDI to be successful these interfaces will be open and yet standardized. The business model is either of ad hoc interactions between [small groups, or agreed upon national or international frameworks, such as those by trade associations or industry bodies (Peat and Webber, 1999).] Peat, B. & Webber, D. August 1997, XML/EDI: The E-business Framework, [Online]. Available: http://www.geocities.com/WallStreet/Floor/5815/startde.htm |
The "hybrid" model is a combination of the first two. Here a "Star" model is extended by trading partners, by creating new versions of frameworks, and by linking in their own ad hoc ones. The "Web" model is a document-centric model. Where content is the most important information being exchanged. Content can either arrive driven by pre-set rules, or be requested, or be broadcast. The classic example for this is an electronic catalog, and the associated "Request For Quotations" (RFQ) dialogs.
Why a framework? XML/EDI provides for the infrastructure of a wide variety of EC systems; from searchable on-line catalogs to robust machine-to-machine transaction subsystems. The XML/EDI initiative is to provide open solutions for implementing E-business systems today. The operative word here is "solutions". There isn't just one solution for all of the E-business scenarios. Each scenario has its own requirements and goals. This is why we need a framework and not an application or module. The goal of the framework is to provide formal interfaces for commercial EC components to interoperate. For XML/EDI to be successful these interfaces will be open and yet standardized. The business model is either of ad hoc interactions between small groups, or agreed upon national or international frameworks, such as those by trade associations or industry bodies. |
The source is given but it is not made clear that the text is so extensively copied - no quotation marks. |
| [112.] Svr/Fragment 053 01 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 53, Zeilen: 1 ff. (completely) |
Quelle: Peat Webber 1997 Seite(n): online, Zeilen: 0 |
|---|---|
| [The business model is either of ad hoc interactions between] small groups, or agreed upon national or international frameworks, such as those by trade associations or industry bodies (Peat and Webber, 1999).
[Figure 10] Figure 10: XML/EDI Layered Architecture (Peat/Webber, 1999). Figure 10 depicts the technical layers that a base XML/EDI system can be built on. Not all layers are required to achieve results with XML/EDI. The framework builds upon and enhances the XML and EDI standards and defines the blueprint of ecommerce component interaction. For example, catalog vendors may only want to implement the XML tagging. The tags are defined in standard repositories. The various layers support different targeted e-commerce systems. Overall each successive layer provides increasingly more sophisticated capabilities so as to handle more demanding needs (Peat and Webber, 1999). The framework is not an all-or-nothing implementation. Each e-commerce component is designed to be able to be used independently, interfacing with each other as defined by XML/EDI standards. DTDs formally define the structure of EDI messages without having to use it to validate well-formed XML documents. EDIFACT/X12 messages can simply be placed in an XML shell element or the message (or parts of it) can be coded in XML. Messages can be formally validated, or simply checked to be well-formed. Messages can be linked to data stored elsewhere, or completely stored internally. Documents can be linked to rule-templates, or be in-built (or no) rules for processing the received data. There is a variety of possibilities (options) as how to integrate EDI with XML. End Users interact with these technical layers through highly visual desktop tools. Developers [use e-commerce components to build these tools.] Peat, B. & Webber, D. August 1997, XML/EDI: The E-business Framework, [Online]. Available: http://www.geocities.com/WallStreet/Floor/5815/startde.htm |
The business model is either of ad hoc interactions between small groups, or agreed upon national or international frameworks, such as those by trade associations or industry bodies.
Figure 3 - XML/EDI Layered Architecture Figure 3 depicts the technical layers that a base XML/EDI system can be built. Not all layers are required to achieve results with XML/EDI. The framework builds upon and enhances the XML and EDI standards and defines the blueprint of EC component interaction. For example, catalog vendors may only want to implement the XML tagging. The tags are defined in "standard" repositories. The various layers support different targeted EC systems. Overall each successive layer provides increasingly more sophisticated capabilities so as to handle more demanding needs. The framework is not a "all-or-nothing" nothing implementation. Each EC component is designed to be able to be used independently -- interfacing with each other as defined by XML/EDI standards. You can create a DTD for formally define the strucuture of EDI messages without having to use it to validate well-formed XML documents. You can simply place EDIFACT/X12 messages in an XML shell element or you can code the message, or parts of it, in XML. You can chose to formally validate messages, or simply check that they are well-formed XML. You can link your messages to data stored elsewhere, or have it all stored intermally. You can link your documents to rule-templates, or have in-built (or no) rules for processing the data you receive. Its up to you how you mix and match the options. End Users interact with these technical layers through highly visual desktop tools. Developers use EC components to build these tools. |
The source is given three times but it is not made clear that the text is so extensively copied - no quotation marks. |
| [113.] Svr/Fragment 054 01 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 54, Zeilen: 1-4 |
Quelle: Peat Webber 1997 Seite(n): online, Zeilen: 0 |
|---|---|
| Users interface with their documents, as they would use any tool in their desktop applications, wordprocessing, spreadsheets, databases or whatever metaphor is most suited to the application. | Users interface with their documents as they would use any tool in their office support products - word-processing, spreadsheets, databases or whatever metaphor is most suited to the application. |
Continued from previous page, see Fragment 053 01. |
| [114.] Svr/Fragment 054 06 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 54, Zeilen: 6-11, 24-30 |
Quelle: Bryan 1998 Seite(n): online, Zeilen: 0 |
|---|---|
| The XML/EDI Group was set up in 1997 to determine how the expertise built up by the EDI community over many years of study into the problems of business-to-business communication could best be expressed in terms of XML. Their goal was to allow EDI-based transactions to be integrated with other types of communication currently taking place over the Internet to form a virtual electronic environment for business transactions (XML/EDI Group, 1999).
[...] Furthermore, the set of draft Guidelines for the use of XML for EDI needed to be tested in a European scenario to ensure that they are adequate to meet the multilingual and mixed trading practices found in Europe; this is done by the European XML/EDI Pilot Project. Subject and Scope of this group is to test the applicability XML for interchanging data, between small businesses and their business partners, of the type currently exchanged using EDI messages for the European market (Bryan 1998a). Bryan, M. 1998a: European XML/EDI Pilot Project - Terms of Reference (Draft 1.0), [Online]. Available:
http://www.cenorm.be/workshop/ec/xmledi/Documents_98/xml005.html XML/EDI Group (eds). 1999, Homepage of the XML/EDI Group, [Online].
Avaliable: http://www.geocities.com/WallStreet/Floor/5815 |
European XML/EDI Pilot Project
2) Subject and Scope To test the applicability XML for interchanging data, between SMEs and their business partners, of the type currently exchanged using EDI messages. [...] The international XML/EDI Group has developed a set of draft Guidelines for the use of XML for EDI. These Guidelines need to be tested in a European scenario to ensure that they are adequate to meet the multilingual and mixed trading practices found in Europe. [...] The XML/EDI Group was set up to determine how the expertise built up by the EDI community over many years of study into the problems of business-to-business communication could best be expressed in terms of XML. Their goal is to allow EDI-based transactions to be integrated with other types of communication currently taking place over the Internet to form a virtual electonic environment for business transactions. |
The actual source is given, but quotation marks are missing. |
| [115.] Svr/Fragment 054 12 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 54, Zeilen: 12-23 |
Quelle: Walsh Nelson 1998 Seite(n): online, Zeilen: 0 |
|---|---|
| The XML/EDI Group has formed a working group in 1998 to organize the development of a global repository. The goal of the XML/EDI repository working group, was to develop a repository for business transactions based on the Extensible Markup Language. The repository would store the tag sets, document type definitions, Extensible Stylesheet language templates, and other schema needed for effective business-to-business communication (XML/EDI Repository Group 1999a). Posting DTDs online and sharing them among partners is not a new concept, but previously it had only existed among small groups. By opening up the repository, it will serve as a global library for companies to share their preferred formats. The repositories are not limited to text, however. Anything that can be sent via MIME can be housed in the repository, which opens it up to scripts, Java applets, and various forms and templates.
XML/EDI Repository Group (eds). 1999a, Official website of the XML/EDI repository Working Group, [Online]. Available: http://www.xmledi.com/repository |
The XML/EDI Group has announced it is developing a repository for business transactions based on the Extensible Markup Language (XML).
The repository would store the tag sets, document type definitions (DTDs), Extensible Stylesheet Language templates, and other schema needed for effective business-to-business communication, according to Bruce Peat, chairman of the XML/EDI Group. [...] The XML/EDI Group is also forming a working group to organize the development of the repository. [...] Peat noted that posting DTDs online and sharing them among partners is not a new concept, but previously it had only existed among small groups. By opening up the repository, it will serve as a global library for companies to share their preferred formats. The repositories are not limited to text, however. Anything that can be sent via MIME can be housed in the repository, which opens it up to scripts, Java applets, and various forms and templates. |
The actual source is not given. The given reference does not lead to the content, see https://web.archive.org/web/19991009055853/http://www.xmledi.com/repository/ resp. https://web.archive.org/web/19991118230529/http://www.xmledi.com/repository/repository.htm . |
| [116.] Svr/Fragment 055 01 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 55, Zeilen: 1-4 |
Quelle: Erdmann Studer 1999 Seite(n): online, Zeilen: 0 |
|---|---|
| [All these XML/EDI movements realized that there is a big downside to XML. In spite XML’s positive features and prospects it must be clearly stated that XML is] solely a description language to specify the structure of documents and thus their syntactic dimension. The document structure can represent some semantic properties but it is not clear how this can be deployed outside of special purpose applications. | In spite of these positive features and prospects of XML it must be clearly stated that XML is solely a description language to specify the structure of documents and thus their syntactic dimension. The document structure can represent some semantic properties but it is not clear how this can be deployed outside of special purpose applications. |
No source is given. A variation of this text can also be found in Fragment 032 03. |
| [117.] Svr/Fragment 055 04 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 55, Zeilen: 4-10 |
Quelle: Heflin 2000 Seite(n): online, Zeilen: 0 |
|---|---|
| XML allows individuals and organizations to create tag sets that describe more than just how to display their information. But there still is an interoperability problem. If a university and a furniture store both use the tag < Chair >;, do they mean the same or different things? What if another furniture store uses the tag < Seat >? XML DTDs can be used to ensure that a set of documents use the same set of tags, but it would be impossible to create a single DTD that describes everything. | This allows individuals and organizations to create tag sets that describe more than just how to display their information. However, this flexibility leads to an interoperability problem: if a university and a furniture store both use the tag < Chair >, do they mean the same or different things? What if another furniture store uses the tag < Seat >? XML DTDs can be used to ensure that a set of documents use the same set of tags, but it would be impossible to create a single DTD that describes everything! |
The source is not given. |
| [118.] Svr/Fragment 055 22 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 55, Zeilen: 22-28 |
Quelle: Webber 1998 Seite(n): 38, 39, Zeilen: 38: right col., last paragraph; 39: center col., 8 ff. |
|---|---|
| As discussed above, history shows that in the past traditional EDI failed to create a broad based acceptance for a number of reasons. The most important one being that setting up traditional EDI is an expensive and time consuming manual process as trading partners attempt to synchronize their internal systems with the external systems of their partners. Worse, some large companies, such as the mayor [sic] manufacturers have potentially three hundred thousand trading partners in the USA alone (Webber 1998a: 38).
Webber, D. 1998a, “Introducing XML/EDI Frameworks”, Electronic Markets, vol. 8, no.1, pp38-41. |
Setting up traditional EDI is an expensive and time consuming manual process as trading partners attempt to synchronize their internal systems with the external systems of their partners. Worse, some large companies, such as the major car manufacturers have potentially three hundred thousand trading partners in the USA alone.
[page 39] However returning to the underlying business parameters rather than technologies themselves, history shows that in the past traditional EDI failed to create a broad based acceptance for a number of reasons. |
The source is given, but there are no quotation marks. |
| [119.] Svr/Fragment 055 29 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 55, Zeilen: 29-31 |
Quelle: XML EDI Group 2001 Seite(n): online, Zeilen: 0 |
|---|---|
| The Internet proposes a vast opportunity for businesses to conduct a form of electronic communication. In contrast to traditional EDI, Internet use has grown astronomically in the last few years. | The Internet proposes a vast opportunity for businesses to conduct a form of electronic communication. In contrast to traditional EDI, Internet use has grown astronomically in the last few years. |
No source is given. |
| [120.] Svr/Fragment 056 02 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 56, Zeilen: 2-26 |
Quelle: Norman 1999 Seite(n): 45, Zeilen: 6 ff. |
|---|---|
| [4.2.1 Impact of XML on EDI]
What XML provides is primarily (a) Self-explaining syntax, (b) Modularity, (c) Extensibility, (d) Presentation, and (e) Transformation. Self-explaining syntax: Since the elements in XML are discoverable using document type definitions, the elements used to describe a supplier's product, its pricing, or other attributes can be gleaned without first having to agree upon a single format beforehand. Previous visions of EDI could not use this kind of ad hoc partnership approach. At best, an industry might define a set of EDI templates or forms for specific transaction types. Generally, these would be established by the largest company in a supply chain as a de facto set of transaction standards and data types. Modularity: The XML/EDI messages can be constructed using a combination of several standardized modules. It is possible to provide a number of standardized and publicly accepted building blocks that can be used to construct more complex EDI messages. This is quite different from the current implementations where all the functionally has to be included in the messages from the beginning, resulting in that people are adding all kinds of messages in the standards because they may be used in the future. Extensibility: Since the EDI standard using XML is no longer under the eye of standardization committees, such as UN/EDIFACT and ANSI X12, it is much easier to add new support and functionality in the EDI messages. Presentation: The XML/EDI messages can be presented directly to the user using the XSL specification (when and if such support becomes available in the browsers). Transformation: The XML/EDI messages can be processed transformed and analyzed using the proposed XML/QL standardization. |
What XML provides is primarily:
· Self-explaining syntax: Since the elements in XML are discoverable using document type definitions, the elements used to describe a supplier's product, its pricing, or other attributes can be gleaned without first having to agree upon a single format beforehand. Previous visions of EDI could not use this kind of ad hoc partnership approach. At best, an industry might define a set of EDI templates or forms for specific transaction types. Generally, these would be established by the largest company in a supply chain as a de facto set of transaction standards and datatypes. · Modularity: The XML – EDI messages can be constructed using a combination of several standardized modules. It is possible to provide a number of standardized and publicly accepted building blocks that can be used to construct more complex EDI messages. This is quite different from the current implementations where all the functionally has to be included in the messages from the beginning, resulting in that people are adding all kinds of messages in the standards because they MAY be used in the future. · Extendibility: Since the EDI standard using XML is no longer under the eye of standardization committees, such as UN/EDIFACT and ANSI X12, it is much easier to add new support and functionality in the EDI messages. · Presentation: The XML – EDI messages can be presented directly to the user using the XSL specification (when and if such support becomes available in the browsers). · Transformation: The XML – EDI messages can be processed, transformed and analyzed using the proposed XML-QL standardization. |
The source is not given. |
| [121.] Svr/Fragment 056 28 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 56, Zeilen: 28-30 |
Quelle: Edwards 1999 Seite(n): online, Zeilen: 0 |
|---|---|
| Compared with conventional EDI approaches, the Internet offers less costly transactions, easier access, broader reach, and improved functionality. With its flat-rate fee structure, for instance, the Internet is substantially cheaper than the [value-added networks (VANs) traditionally used for EDI, which charge by the byte for each EDI message.] | Compared with conventional EDI approaches, the Internet offers less costly transactions, easier access, broader reach, and improved functionality. With its flat-rate fee structure, for instance, the Internet is substantially cheaper than the value-added networks (VANs) traditionally used for EDI, which charge by the byte for each EDI message. |
Source is given on p. 57. Text is copied literally without quotation marks, however. |
| [122.] Svr/Fragment 057 01 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 57, Zeilen: 1-13, 15-32 |
Quelle: Edwards 1999 Seite(n): online, Zeilen: 0 |
|---|---|
| [With its flat-rate fee structure, for instance, the Internet is substantially cheaper than the] value-added networks (VANs) traditionally used for EDI, which charge by the byte for each EDI message. Using traditional EDI, it costs about $2.50 to process a purchase order, compared to around $50 to process a paper-based version, according to Forrester Research, Cambridge, Mass. Internet-based EDI can lower the transaction cost still further, to less than $1.25 (Edwards 1999).
The Internet also makes EDI accessible to the companies previously shut out by the high start-up fees and complexity of implementing and maintaining the required systems. In large companies, these costs can be justified by the increase in efficiency and the additional revenues generated from trading partners. For smaller companies, though, the EDI costs may be prohibitive, so millions of firms are denied these revenue opportunities. With a Web-based EDI service, companies can now be part of the action for less than $1,000 a year, compared to the estimated cost of $50,000 to join a traditional EDI network. [4.2.3 Hub and Spoke Relationship Improvement] For the moment, though, rather than eliminating EDI, organizations are combining it with Internet transaction systems to make the service faster and more comprehensive, and to add new partner, supplier, and customer connections, especially with smaller firms. This is a win-win development, since the more partners and suppliers a company connects, the larger the savings and production efficiencies and, often, the greater the revenues. Changes are also occurring in the traditional hub-spoke EDI business model, where the hub is the organization that initiates the transaction and the spoke the trading partner supplying products and services to the hub. Increasingly, organizations are adopting a dual-capacity role as both hubs and partners, creating an extended EDI model. The Internet takes this evolution a step further by adding extranets with the potential for connecting many more partners, suppliers, distributors, and customers. According to market researcher International Data Corp. (IDC), dual-capacity hubpartners will account for the strongest growth in EDI transactions over the next few years, jumping from one-quarter of EDI service revenues in 1998 to two-thirds by 2003. IDC also predicts that the Internet will handle 41% of EDI transactions by 2003, up from 6% in 1998. It still sees a rosy future for EDI, projecting an 18.6% [compound annual growth rate in EDI service revenues to reach $2.3 billion by 2003, with the Internet portion accounting for 33% of the revenues (Edwards 1999).] |
With its flat-rate fee structure, for instance, the Internet is substantially cheaper than the value-added networks (VANs) traditionally used for EDI, which charge by the byte for each EDI message. Using traditional EDI, it costs about $2.50 to process a purchase order, compared to around $50 to process a paper-based version, according to Forrester Research, Cambridge, Mass. Internet-based EDI can lower the transaction cost still further, to less than $1.25.
The Internet also makes EDI accessible to the companies previously shut out by the high start-up fees and complexity of implementing and maintaining the required systems. In large companies, these costs can be justified by the increase in efficiency and the additional revenues generated from trading partners. For smaller companies, though, the EDI costs may be prohibitive, so millions of firms are denied these revenue opportunities. With a Web-based EDI service, companies can now be part of the action for less than $1,000 a year, compared to the estimated cost of $50,000 to join a traditional EDI network. [...] For the moment, though, rather than eliminating EDI, organizations are combining it with Internet transaction systems to make the service faster and more comprehensive, and to add new partner, supplier, and customer connections, especially with smaller firms. This is a win-win development, since the more partners and suppliers a company connects, the larger the savings and production efficiencies and, often, the greater the revenues. Changes are also occurring in the traditional hub-spoke EDI business model, where the hub is the organization that initiates the transaction and the spoke the trading partner supplying products and services to the hub. Increasingly, organizations are adopting a dual-capacity role as both hubs and partners, creating an extended EDI model. The Internet takes this evolution a step further by adding extranets with the potential for connecting many more partners, suppliers, distributors, and customers. According to market researcher International Data Corp. (IDC) of Framingham, Mass., dual-capacity hub/partners will account for the strongest growth in EDI transactions over the next few years, jumping from one-quarter of EDI service revenues in 1998 to two-thirds by 2003. IDC also predicts that the Internet will handle 41% of EDI transactions by 2003, up from 6% in 1998. It still sees a rosy future for EDI, projecting an 18.6% compound annual growth rate in EDI service revenues to reach $2.3 billion by 2003, with the Internet portion accounting for 33% of the revenues. |
Although the source is given twice, there are no quotation marks. |
| [123.] Svr/Fragment 058 05 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 58, Zeilen: 5-11, 18-31 |
Quelle: Webber 1998 Seite(n): 39, Zeilen: left col. 1 ff.; right col. 14 ff. |
|---|---|
| EDI has traditionally used unique segment identifiers like tokens to separate and identify data items within messages. So replacing those same segments with web tokens allows XML to express EDI and carry EDI via Web delivery methods. This moves EDI from the arcane, obtuse and static into the dynamic mainstream of computing. Webber (1998a: 41) predicts that XML will move EDI from the inadequate 10,000 companies using traditional EDI in the US to millions of desktops and companies instead.
[...] XML/EDI allows each trading partner to quickly synchronize their systems by exchanging not just EDI data, but also process control templates as well. Thus not only this data exchanged but also the enabling underlying process information. Additionally the process control templates are supported by the use of software agents (typically Java and ActiveX components) and Internet based global Reference repositories that allow the required process to be both directed and centrally coordinated. This means that large companies can provide a foundation that their smaller trading partners can easily download and re-use or simply adapt for their local needs. Extended rule based businesses are now possible going beyond traditional process flow forms, and including dynamic and ad-hoc systems that adapt. This is the model needed to create full electronic enterprises where documents and business information flows and is exchanged easily. Other business models are also enabled. The use of HTML on the web has already allowed product catalogues to be integrated into the sales order process. Better [yet with XML markup creating objects and meta-data new uses for catalogues, that allow customers to request information based on criteria and rules can be setup. Also XML documents include web-style content such as graphics and multimedia, nut [sic] just bare text (Webber 1998a: 39).] Webber, D. 1998a, “Introducing XML/EDI Frameworks”, Electronic Markets, vol. 8, no.1, pp38-41. |
XML/EDI solves this impasse by allowing each trading partner to quickly synchronize their systems by exchanging not just EDI data, but also process control templates as well. Thus not only is data exchanged but also the enabling underlying processing information.
Additionally the process control templates are supported by the use of software agents (typically Java and ActiveX components) and internet based Global Reference Repositories that allow the required processes to be both directed and centrally coordinated (figure 1). This means that large companies can provide a foundation that their smaller trading partners can easily download and re-use, or simply adapt for their local needs. Extended rule based business processes are also now possible, going beyond traditional process flow forms, and including dynamic ad hoc systems that adapt. This is the model needed to create full Electronic Enterprises where documents and business information flows and is exchanged easily. Other business models are also enabled. The use of HTML on the Web has already allowed product catalogues to be integrated into the sales order process. Better yet with XML markup creating objects and meta-data new uses for catalogues, that allow customers to request information based on criteria and rules can be setup. Also XML documents include Web style content such as graphics and multimedia, not just bare text (figure 2). [...] EDI (Electronic Data Interchange) has traditionally used unique segment identifiers like tokens to separate and identify data items within messages. So replacing those same segments with Web tokens allows XML to express EDI and carry EDI via Web delivery methods. This moves EDI from the arcane, obtuse and static into the dynamic mainstream of computing. From the pitifully inadequate 10,000 companies using current EDI in the US, to millions of desktops and companies instead. |
Although the source is given twice, there are no quotation marks. |
| [124.] Svr/Fragment 059 01 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 59, Zeilen: 1-4 |
Quelle: Webber 1998 Seite(n): 39, Zeilen: left col. last line, center col. 1 ff. |
|---|---|
| [Better] yet with XML markup creating objects and meta-data new uses for catalogues, that allow customers to request information based on criteria and rules can be setup. Also XML documents include web-style content such as graphics and multimedia, nut [sic] just bare text (Webber 1998a: 39).
Webber, D. 1998a, “Introducing XML/EDI Frameworks”, Electronic Markets, vol. 8, no.1, pp38-41. |
Better yet with XML markup creating objects and meta-data new uses for catalogues, that allow customers to request information based on criteria and rules can be setup. Also XML documents include Web style content such as graphics and multimedia, not just bare text (figure 2). |
The source is given, but quotation marks are missing. |
| [125.] Svr/Fragment 059 08 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 59, Zeilen: 8-13 |
Quelle: Ricciuti Wong 1999 Seite(n): online, Zeilen: 0 |
|---|---|
| XML is touted as an industry neutral language that could revolutionize information exchange in much the same way that HTML has defined the Web. But XML's greatest strength, which is allowing developers to custom-build systems for data exchange, could also be its downfall, leading to incompatible versions that could tarnish XML's cross-industry appeal, analysts said. (Cnet News 1998).
Wong, W. 1998, “XML to revolutionize info exchange”, Cnet News, 31 Dec [Online]. Available: http://www.news.com |
XML is touted as an industry-neutral language that could revolutionize information exchange in much the same way that HTML has defined the Web. But XML's greatest strength--allowing developers to custom-build systems for data exchange--could also be its downfall, leading to incompatible versions that could tarnish XML's cross-industry appeal, analysts said. |
The actual source is not given. The given reference does not lead to the content. |
| [126.] Svr/Fragment 059 14 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 59, Zeilen: 14-18 |
Quelle: Dumbill 2001 Seite(n): online, Zeilen: 0 |
|---|---|
| XML is still young in terms of practical development experience. Critics fear that the relentless flood of specification development and marketing endangers the discovery and communication of solid XML programming experience. They see a threat in overselling the XML idea, and would prefer to see the hype machine slow a little and getting on with building practical systems instead. | The XML world is still a young one in terms of practical development experience, and the most interesting sessions at XML conferences are ones where individual developers share the techniques and tricks they've discovered for processing XML.
[...] The relentless flood of specification development and marketing endangers the discovery and communication of solid XML programming experience. It's time to slow the hype machine a little, take a rest, and get on with building practical systems. |
The source is mentioned on the next page as the source for a literal quotation. |
| [127.] Svr/Fragment 059 19 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 59, Zeilen: 19-31 |
Quelle: Johnson 1999 Seite(n): 77, 81, Zeilen: 77: 3rd col., 11 ff.; 81: left col., 50 ff., 2nd col., 5 ff. |
|---|---|
| As XML standardization efforts have not really caught on yet, organizations find it easier to create custom tags and just map data to achieve interoperability. Many corporations today are building effective XML utilities without waiting for standardization. Experts point out that this is not much of a problem after all, as it is easy to map one application's tag set to another if and when tagging standards change. XML is flexible enough, as long a high-level set of rules is followed. Companies are not looking for external definitions of XML tags, they are rather building their own sets of tags for internal use and translating them to communicate with external partners.
XML has barely penetrated the vast established base of Web browsers and other HTML tools, which means XML data may not display properly in all applications. Older browsers do not natively render XML. Companies still have to convert XML to HTML on the fly. That is one feature to look for in an XML application server. |
XML standardization efforts haven't really caught on, organizations find it easier to create custom tags and just map data to achieve interoperability.
[page 81] But many corporations today are building effective XML utilities without waiting for standardization. Moore points out that it's easy to map one application's tag set to another if tagging standards change. "XML is flexible enough, as long as I follow a high-level set of rules," he says. Gilpin agrees. Companies aren't looking for external definitions of XML tags, he says. They're building their own sets of tags for internal use and translating them to communicate with external partners, he says. [...] XML has barely penetrated the vast established base of Web browsers and other HTML tools, which means XML data may not display properly in all applications. Older browsers don't natively render XML, points out Don Klein, Ingenta's manager of new media services. Ingenta still has to convert XML to HTML on the fly. That's one feature to look for in an XML application server. |
No source is given. |
| [128.] Svr/Fragment 060 02 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 60, Zeilen: 2-6 |
Quelle: Johnson 1999 Seite(n): 80, Zeilen: third col. 5 ff.; right col. 6 f. |
|---|---|
| Overall response time of XML applications slows as the data store grows larger. Object databases, which store XML content, are not as highly tuned as standard SQLbased relational database management systems. Using XML is not necessarily proven in terms of performance. Many believe that these problems will disappear as XML settles in. | Then, too, says Klein, overall response time of XML applications slows as the data store grows larger. Object databases, which store XML content, aren’t as highly tuned as standard SQL-based relational database management systems. “Using XML is not necessarily proven in terms of performance,” he says. [...]
Most say these problems will disappear as XML settles in. |
No source is given. |
| [129.] Svr/Fragment 060 07 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 60, Zeilen: 7-19, 27-32 |
Quelle: Norman 1999 Seite(n): 44, 47, 48, Zeilen: 44: 7 ff.; 47: 2 ff.; 48: last paragraph |
|---|---|
| The XML/EDI groups are working to define XML namespaces and DTDs equal to the EDIFACT standard to support commercial usage of EDI over XML. Even though most organizations agree that EDI using XML is a good idea some are still skeptical. This is due to the fact that they think that EDI is too complex to be dealt with easily. In the health care industry alone, there are 400 different formats for a claim. One of the key issues will be how compatible the new implementations of EDI will be to the old ones; currently there is no answer to this question.
Furthermore a big debate is going on between the different XML/EDI groups on what the structure of the XML tags should be. Some advocate the use of the full description in the tag and others the use of the ANSI element number as the tag name. Others want to use a unique number that would include the standard version of the directory, the segment it resides in and the data-element it represents. [...] [4.4. XML/EDI Example] EDI is quite different from sending electronic mail messages or sharing files through a network, a modem, or a bulletin board. The straight transfer of computer files requires that the computer applications of both the sender and receiver (referred to as "trading partners") agree upon the format of the document. The sender must use an application that creates a file format identical to the receiver’s computer application. |
[page 48]
The XML/EDI group [2] is working to define XML namespaces and DTDs equal to the EDIFACT standard to support commercial usage of EDI over XML. Even though most organizations agree that EDI using XML is a good idea some are still skeptical. This is due to the fact that they think that EDI is too complex to be dealt with easily. In the health care industry alone, there are 400 different formats for a claim. One of the key issues will be how compatible the new implementations of EDI will be to the old ones; currently there is no answer to this question. [page 47] Currently a big debate is going on between the different XML-EDI groups on what the structure of the XML tags should be. Some advocate the use of the full description in the tag and others the use of the ANSI element number as the tag name. Others want to use a unique number that would include the standard version of the directory, the segment it resides in and the data-element it represents. [page 44] EDI is quite different from sending electronic mail messages or sharing files through a network, a modem, or a bulletin board. The straight transfer of computer files requires that the computer applications of both the sender and receiver (referred to as "trading partners") agree upon the format of the document. The sender must use an application that creates a file format identical to the receiver’s computer application. |
The source is not given. |
| [130.] Svr/Fragment 060 22 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 60, Zeilen: 22-25 |
Quelle: Dumbill 2001 Seite(n): online, Zeilen: 0 |
|---|---|
| [Concerning the current developments in the ebXML area: “None of the vendors quite knows where we are running to, but they are running faster and harder than before to get there before their rivals” (Dumbill 2001).] Vendors claim to be cooperating on specifications, but compete on implementations. Despite vendor assurance, it seems plain that the race to compete on implementation puts the viability of multivendor institutions at risk.
Dumbill, E. 2001, XML hype down but not out in New York [Online]. Available:
http://www.xml.com/lpt/a/2001/04/11/xmldevcon.html |
None of the vendors quite knows where we're running to, but they're running faster and harder than before to get there before their rivals. IBM, Microsoft, and Sun's latest mantra is to "cooperate on specifications, but compete on implementations"; and competing they are. [...]
Despite vendor assurances, it seems plain that the race to compete on implementation puts the viability of multivendor institutions like OASIS at risk. |
The source is given for literal quote, but is not made clear that the copying continues after the reference. |
| [131.] Svr/Fragment 061 01 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 61, Zeilen: 1 ff. (completely) |
Quelle: Norman 1999 Seite(n): 45, 46, Zeilen: 45: 38 ff.; 46: 1 ff. |
|---|---|
| A retailer stocks inventory from a major manufacturer. For years this retailer has been ordering merchandise from the manufacturer using a human-readable purchase order such as that in Figure 11 for 1000 fuzzy dice. Now fuzzy dice manufacturer is demanding that the retailer begin using EDI for transactions or surcharge will be added to every order to offset the cost of handling manual transactions. The small retailer can't find a more lenient supplier, so it has little choice.
Figure 11: Plain purchase order Unfortunately, EDI compliance means that the retailer will now have to transmit its purchase orders in a format specified in one of the several standard sets for EDI format, the most widely used being ANSI X12 and UN/EDIFACT. Figure 12 shows part of an ANSI X12 version of the purchase order in Figure 11. ST*850*12345 Figure 12: Fragment of ANSI X12 transaction set corresponding to Figure 11 It's possible that the retailer's current accounting software supports EDI transactions, but not likely. It will probably have to either convert to software that [does, purchase software that can make the translation (if available), or contract with a third party to convert the data on an ongoing basis.] |
[page 45]
Consider a small, Web-based retailer that stocks inventory from a major manufacturer. For years the company has been ordering merchandise from the manufacturer using a human-readable purchase order such as that in Listing 1, for 1000 fuzzy dice. Now the manufacturer is demanding that the retailer begin using EDI for transactions or else it will add a surcharge to every order to offset the cost of handling manual transactions. The small retailer can’t find a more lenient supplier, so it has little choice. Listing 1: Plain purchase order [page 46] Unfortunately, EDI compliance means the retailer will now have to transmit its purchase orders in a format specified in one of the several standard sets for EDI format, the most widely used being ANSI X12 and UN/EDIFACT. Listing 2 shows part of an ANSI X12 version of the purchase order in Listing 1. It’s possible that the retailer’s current accounting software supports EDI transactions, but not likely. It will probably have to either convert to software that does, purchase software that can make the translation (if available), or contract with a third party to convert the data on an ongoing basis. Listing 2: Fragment of ANSI X12 transaction set corresponding to Listing 1 ST*850*12345 |
The source is not given. |
| [132.] Svr/Fragment 062 01 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 62, Zeilen: 1 ff. (completely) |
Quelle: Norman 1999 Seite(n): 46, Zeilen: 3 ff. |
|---|---|
| [It's possible that the retailer's current accounting software supports EDI transactions, but not likely. It will probably have to either convert to software that] does, purchase software that can make the translation (if available), or contract with a third party to convert the data on an ongoing basis.
Figure 13: XML document analogue to the X12 transaction set in Figure 12 Would there be any advantage, for the retailer or the manufacturer, to using an XML format instead? Perhaps the retailer's accounting software is tailored to [Internet commerce, and already uses XML formats.] |
It’s possible that the retailer’s current accounting software supports EDI transactions, but not likely. It will probably have to either convert to software that does, purchase software that can make the translation (if available), or contract with a third party to convert the data on an ongoing basis.
[...] So, would there be any advantage, for the retailer or the manufacturer, to using an XML format instead? Perhaps the retailer’s accounting software is tailored to Internet commerce, and already uses XML formats. [...] Listing 3: XML document analog to the X12 transaction set in Listing 2 |
The source is not given. |
| [133.] Svr/Fragment 063 01 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 63, Zeilen: 1 ff. (completely) |
Quelle: Norman 1999 Seite(n): 46, 47, 48, Zeilen: 46: 18 ff.; 47: 28 ff.; 48: 1 ff., 8 ff., 14 f. |
|---|---|
| [Perhaps the retailer's accounting software is tailored to] Internet commerce, and already uses XML formats. In this case, there are utilities for converting one data type definition (DTD) to another, and a generic tool accomplishes the conversion to EDI. The resulting transmission would certainly be more comprehensible to humans, and perhaps even feasible for an employee with a text editor or XML editor to generate. An example of how the sample purchase order might look in an XML rendering of X12 is given in Figure 13. This example is based on the ongoing work of the XML/EDI group. One disadvantage with using XML, as can be seen below, is that the size of the EDI messages gets a lot bigger than the X12 messages. In this example, the XML message is about 8 times bigger than the X12 message.
The idea of XML repositories is to provide a means for industries to store the document-type definitions, that identify the data elements and their relationships exchanged among parties doing business electronically, on the Internet. Repositories contain logic components, such as Java applets, template scripts, forms and object definitions needed to process message components. With common registration procedures for these components, repositories will act as global libraries, and enable industry groups, government agencies, and businesses of all sizes to make their preferred message formats widely available to current and potential trading partners. The intent of the Global Repository is to be a dynamic mechanism that responds through an open Application Programming Interface (API). It is anticipated that fully functional global repositories will evolve in phases: Phase 1 Limited Intranet implementation, proof of concept, with manual Web interface. Phase 2 Definition of basic API allows extranet implementations between specific partners. Phase 3 Definition of full API and available repository products allows full implementations. Phase 4 DNS style service established and standards bodies adopt support for API and long-term maintenance and alignment. |
[page 46]
Perhaps the retailer’s accounting software is tailored to Internet commerce, and already uses XML formats. In this case, there are utilities for converting one data type definition (DTD) to another, and the conversion to EDI might be accomplished by a generic tool. The resulting transmission would certainly be more comprehensible to humans, and perhaps even feasible for an employee with a text editor or XML editor to generate. An example of how the sample purchase order might look in an XML rendering of X12 is given in Listing 3. This example is based on the ongoing work of the XML/EDI group. One disadvantage with using XML, as can be seen below, is that the size of the EDI messages gets a lot bigger than the X12 messages. In this example, the XML message is about 8 times bigger than the X12 message. [page 47] XML repositories will provide a means for industries to store on the World Wide Web the document-type definitions that identify the data elements and their relationships exchanged among parties doing business electronically. Repositories will also contain logic components, such as Java applets, template scripts, forms and object definitions needed to process message components. [page 48] With common registration procedures for these components, repositories will act as global libraries, and enable industry groups, government agencies, and businesses of all sizes to make their preferred message formats widely available to current and potential trading partners. [...] It is anticipated that fully functional global repositories will evolve in phases: · Phase 1 - Limited Intranet implementation, proof of concept, with manual Web interface. · Phase 2 - Definition of basic API allows Extranet implementations between specific partners. · Phase 3 - Definition of full API and available repository products allows full implementations. · Phase 4 - DNS style service established and standards bodies adopt support for API and long term maintenance and alignment. [...] The intent of the Global Repository is to be a dynamic mechanism that responds through an open Application Programming Interface (API). |
The source is not given. |
| [134.] Svr/Fragment 064 01 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 64, Zeilen: 1-7 |
Quelle: Norman 1999 Seite(n): 48, Zeilen: 15 ff. |
|---|---|

Figure 14: XML/EDI Transaction Schematics Example: An XML-EDI transaction using a global repository (1) The Retailer queries the Global Repository for the structure (DTD) of those common business objects that are to be passed to the trading partner, the manufacturer. (2) The business objects are passed to the Manufacturer, using XML documents structured according to the DTDs fetched from the Global Repository. (3) The Manufacturer maps the received data in to the organization’s application system. The mapping is received from the Global Repository. |
Example: An XML-EDI transaction using a global repository
Figure 11: XML/EDI Transaction Schematics A user or agent in Organization 1 queries the Global Repository for the structure (DTD) of those common business objects that are to be passed to a trading partner - Organization 2. · The business objects are passed to Organization 2, using XML documents structured according to the DTDs fetched from the Global Repository. · The receiver maps the received data in to the organization’s application system. The mapping is received from the Global Repository. |
The source is not given. |
| [135.] Svr/Fragment 064 09 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 64, Zeilen: 9-16 |
Quelle: Carroll 2000 Seite(n): online, Zeilen: 0 |
|---|---|
| [4.5. Summary and Outlook]
The Fundamental B2B Problem so far has been the lack of shared semantics. The main challenge in using XML is not with document structure and syntax, but with semantics. It is much easier to share syntax than to share semantics. Each application domain needs to have both specific document structure and agreed-upon semantics to make effective use of XML-defined documents. Various vertical industry segments have to agree on the meaning of their domain-specific XML tags. Only then can the appropriate action be taken upon parsing: translating components into internal business objects for use within the enterprise. |
The Fundamental B2B Problem: Lack of Shared Semantics
[...] The main challenge in using XML is not with document structure and syntax, but with semantics. It's much easier to share syntax than to share semantics. Each application domain needs to have both specific document structure and agreed-upon semantics to make effective use of XML-defined documents. Various vertical industry segments have to agree on the meaning of their domain-specific XML tags. Only then can the appropriate action be taken upon parsing: translating components into internal business objects for use within the enterprise. |
No source is given. |
| [136.] Svr/Fragment 064 17 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 64, Zeilen: 17-19 |
Quelle: Balogh 1999 Seite(n): 53, Zeilen: 21 ff. |
|---|---|
| XML can make EDI transactions accessible to a broader set of users. EDI is already a powerful tool that has been deployed by large organizations around the globe to exchange data and support transactions. But today, EDI transactions can [only be conducted between sites that have been specifically set up to exchange information using compatible systems.] | EDI is already a powerful tool that has been deployed by large organizations around the globe to exchange data and support transactions. But today, EDI transactions can only be conducted between sites that have been specifically set up to exchange information using compatible systems. [...] XML should create new possibilities for how data is used, and there are many initiatives under way to move EDI to XML, which can make EDI transactions accessible to a broader set of users. |
The source is not given. |
| [137.] Svr/Fragment 065 01 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 65, Zeilen: 1-5 |
Quelle: Balogh 1999 Seite(n): 53, Zeilen: 22 ff. |
|---|---|
| [But today, EDI transactions can] only be conducted between sites that have been specifically set up to exchange information using compatible systems. XML will allow data to be exchanged, regardless of the computing systems or accounting applications being used. XML should create new possibilities for how data is used, and there are many initiatives under way to move EDI to XML. | But today, EDI transactions can only be conducted between sites that have been specifically set up to exchange information using compatible systems. XML will allow data to be exchanged, regardless of the computing systems or accounting applications being used. XML should create new possibilities for how data is used, and there are many initiatives under way to move EDI to XML, which can make EDI transactions accessible to a broader set of users. |
Continued from previous page. The source is not given. |
| [138.] Svr/Fragment 065 06 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 65, Zeilen: 6-12 |
Quelle: Weitzel et al 2000 Seite(n): 1, Zeilen: left col., abstract |
|---|---|
| Formerly expensive and inflexible EDI-processes can become manageable for SMEs, too, enabling the next step towards open communication and cooperation networks and supporting the flow of information throughout entire purchasing and supply chains. The use of XML also enables the efficient support of various data formats, including EDI or EDIFACT standards, and different business documents such as orders, invoices or catalogs opening EDI networks to SMEs and enabling more dynamic business partnerships. | Using our prototype, formerly expensive and inflexible EDI-processes can become manageable for SMEs, too, enabling the next step towards open communication and cooperation networks and supporting the flow of information throughout entire purchasing and supply chains. The use of XML also enables the efficient support of various data formats, including EDI or EDIFACT standards, and different business documents such as orders, invoices or catalogs opening EDI networks to SMEs and enabling more dynamic business partnerships. |
No source is given. |
| [139.] Svr/Fragment 066 02 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 66, Zeilen: 2-5 |
Quelle: Bakos 1991 Seite(n): online, Zeilen: 0 |
|---|---|
| Benefits of electronic markets that are realized by individual participants increase the more organizations join the system. This property, known as network externalities, can significantly affect the dynamics of the introduction and adoption of electronic market technologies like XML/EDI. | 2. The benefits realized by individual participants in an electronic market increase as more organizations join the system.
This property, known in economics as network externalities (Katz and Shapiro, 1985), can affect the dynamics of the introduction and adoption of electronic market systems, e.g., by favoring the first intermediary introducing such a system. Katz, M. L. and Shapiro, C. "Network Externalities, Competition and Compatibility." American Economic Review, (75) Spring 1985, pp. 70-83. |
No source is given. |
| [140.] Svr/Fragment 066 17 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 66, Zeilen: 17-20, 23-24 |
Quelle: Strassmann 1985 Seite(n): 80, 81, Zeilen: 80: 15 ff., 24 ff.; 81: 24 ff. |
|---|---|
| When it comes to deciding about an IT project, the costs can be defined and controlled quite easily. But the benefits are usually only covered be a few statements full of hope about the effect on large labor costs, and deal with intangible expectations which cannot easily be defined (Strassmann 1985: 81). [This section will give an insight into traditional methods of evaluating IT investments.]
The demand for increased productivity, and the desire to improve responsiveness to customer needs are the driving forces behind Information Systems integration. |
When it comes to making decisions about information technology, I will always consider the competitive market price to be the final arbiter. [...]
The demand for increased productivity, the need to restore falling profits, and the desire to improve responsiveness to customer needs arc the driving forces behind office automation. [page 81] Technical matters, consuming the most time, deal with relatively tangible purchases, with costs that can be defined and controlled. Benefits, covered by a few general statements full of hope about the effects on large labor costs, deal with intangible expectations which cannot easily be defined. |
The source is given, but it neither becomes clear that the text is copied literally, nor which portions have been taken from the source. The copying also continues after the given reference. |
| [141.] Svr/Fragment 067 01 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 67, Zeilen: 1-3 |
Quelle: Strassmann 1985 Seite(n): 80, Zeilen: 22-24 |
|---|---|
| Obviously, investments in information technology must meet the same criteria of justification as any other investment. | Investments in information technology must meet the same criteria of justification as any other investments. |
No source is given. |
| [142.] Svr/Fragment 067 28 |
| KeineWertung |
|---|
| Untersuchte Arbeit: Seite: 67, Zeilen: 28-30 |
Quelle: James 1990 Seite(n): online, Zeilen: 0 |
|---|---|
| Peter Weill (1989) [sic] conducted a 6 year study of IT investment in Australian Business. He explored the effect of IT investment on firms’ performance and concluded that on average, there is no evidence of any positive result.
Weill, P. 1990 [sic], The relationship between investment in Information Technology and Firm Performance: A study of the valve manufacturing sector, University of Melbourne, Graduate School of Management, Parkville, Victoria. |
Dr Peter Weill, senior lecturer at the Melbourne University Graduate School of Management, conducted a six-year study of information technology investment in Australian business that may be partially used in a telecommunications analysis. [...]
[...] "[...] By contrast, investment made to create competitive advantage is risky, and most of the firms that invested heavily for strategic purposes had lower performance and higher labor costs. "On average, there was no evidence of any positive result. [...]" |
... [siehe Anm. zu Svr/Fragment_068_01. Gleiche Situation, daher wohl besser auf kW lassen.] |
| [143.] Svr/Fragment 068 01 |
| KeineWertung |
|---|
| Untersuchte Arbeit: Seite: 68, Zeilen: 1-10 |
Quelle: James 1990 Seite(n): online, Zeilen: 0 |
|---|---|
| - A Large amount of information technology investment (about 50%) is made for infrastructure purposes and is unlikely to be associated with measurable financial gains or losses.
- The traditional methods of analysis under DCF are not appropriate with this type of investment. - Firms which associate heavily in strategic IT were associated with relatively lower non-productive labor productivity and sales growth in the short term. In the long term the effects were neutral. Weill believes that “strategic investments give a short-term edge, which is lost when the technology becomes common”. Weill, P. 1990 [sic], The relationship between investment in Information Technology and Firm Performance: A study of the valve manufacturing sector, University of Melbourne, Graduate School of Management, Parkville, Victoria. |
"A large amount of information technology investment (half) is made for infrastructure purposes and is unlikely to be associated with measurable financial gains or losses," he says. "Return-on-investment analyses using discounted cashflows are not appropriate with this type of investment.
"[...] By contrast, investment made to create competitive advantage is risky, and most of the firms that invested heavily for strategic purposes had lower performance and higher labor costs. "On average, there was no evidence of any positive result. It should be borne in mind that strategic investment gives a short-term edge, which is lost when the technology becomes common." |
...
Das gekennzeichnete wörtliche Zitat findet sich so nicht in der titelgleichen und vom Mai 1992 datierenden Publikation (51 S.) von Weill ([3]), die zum Vergleich vorlag. Dort heißt es im Abstract wörtlich nur: Allerdings bezieht sich James im Dezember 1990 seinerseits auf eine frühere (aber nicht genannte) Weill-Publikation, die aus der Zeit davor stammen muss - infrage kämen:
Mit beiden Texten konnte bisher allerdings nicht verglichen werden. |
| [144.] Svr/Fragment 069 11 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 69, Zeilen: 11-23, 101-104 |
Quelle: Copeland Weston 1992 Seite(n): 25, 26, Zeilen: 25: 32 ff.; 26: 10 ff. |
|---|---|
| Investment decision rules are usually referred to as capital budgeting techniques. According to Copeland and Weston (1992: 26) the best technique will possess the following essential property: It will maximize shareholder's wealth. This essential property can be broken down into separate criteria:
- All cash flows must be considered. - The cash flows should be discounted at the opportunity cost of funds. - The techniques should select from a set of mutually exclusive projects the one that maximizes shareholders wealth. - Managers should be able to consider one project independently from all other (this is known as the value additivity principle). These theories assume that capital markets are frictionless1 and that the stream of cash flows estimated without error, which is also referred to as “Investment under Certainty” (Copeland and Weston 1992: 25). 1 In a frictionless market (1) financial managers can separate investment decision [sic] from individual shareholder preferences, and (2) monitoring costs are zero, so that managers will maximize shareholder's wealth. All they need to know are cash flows and the required market rate of return for projects if [sic] equivalent risk (Copeland and Weston, 1992: 25). Copeland, T.E. & Weston, J.F. 1988 [sic], Financial Theory and Corporate Policy, 3rd ed., Addison-Wesley, Reading, Massachusetts. |
We assume, for the time being, that the stream of cash flows provided by a project can be estimated without error, and that the opportunity cost of funds provided to the firm (this is usually referred to as the cost of capital) is also known. We also assume that capital markets are frictionless, so that financial managers can separate investment decisions from individual shareholder preferences, and that monitoring costs are zero, so that managers will maximize shareholders' wealth. All that they need to know are cash flows and the required market rate of return for projects of equivalent risk.
[page 26] Investment decision rules are usually referred to as capital budgeting techniques. The best technique will possess the following essential property: It will maximize shareholders' wealth. This essential property can be broken down into separate criteria: • All cash flows should be considered. • The cash flows should be discounted at the opportunity cost of funds. • The technique should select from a set of mutually exclusive projects the one that maximizes shareholders' wealth. • Managers should be able to consider one project independently from all others (this is known as the value-additivity principle). |
The source is given in the text and in a footnote. Quotation marks are used for three words ("investment under certainty") which cannot be found in the source for the page referenced, but only on p. 78 in the caption for Figure 4.1. |
| [145.] Svr/Fragment 070 02 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 70, Zeilen: 2-8, 10-15, 17-29 |
Quelle: Copeland Weston 1992 Seite(n): 27, 28, 29, 36, Zeilen: 27: 12 f., 19 ff.; 28: 2 ff.; 29: last paragraph; 30: 17 f.; 36: 5 ff. |
|---|---|
| [5.2.1 Static Methods]
Accounting Rate of Return: The ARR is the average after tax profit divided by the initial cash outlay. It is very similar to the Return on Assets, or the return on investment. Copeland and Weston (1999: 28) do not regard the ARR as an appropriate capital budgeting technique as it uses accounting profits instead of cash flows and it does not consider the time value of money. Pay-Off-Method (Pay Back Method): The payback period is the number of years it takes to recover the initial outlay. [...] If management were adhering strictly to the project, it would choose the project with the shortest payback period. The difficulty of the payback method is that it does not consider all cash flows and it fails to discount them. Copeland and Weston (1992: 26-28) reject the Payback Method because it violates three of four properties that are desirable in capital budgeting techniques as stated above (1,2 and 3). [5.2.2 Dynamic] Internal Rate of Return (IRR): The IRR on a project is defined as that rate, which equates the present value of the cash outflows and inflows, i.e. where the NPV is zero. Hence this is the rate of return on invested capital that the project is returning to the firm. If the IRR criterion is used and the projects are independent, any project that has an IRR greater than the opportunity cost of capital will be accepted. According to Copeland and Weston (1992: 36) the IRR rule errs in several ways. First, it does not obey the value additivity principle, and consequently managers who use the IRR cannot consider projects independently of each other. Second, the IRR rule assumes that funds invested in projects have opportunity costs equal to the IRR of the projects. This implicit reinvestment rate assumption violates the requirement that cash flows be discount at the market determined opportunity cost of capital. Finally, the IRR rule can lead to multiple rates of return whenever the sign of cash flow changes more than once. Copeland, T.E. & Weston, J.F. 1988 [sic], Financial Theory and Corporate Policy, 3rd ed., Addison-Wesley, Reading, Massachusetts. |
1. The Payback Method
The payback period for a project is simply the number of years it takes to recover the initial cash outlay on a project. [...] If management were adhering strictly to the payback method, it would choose project A, which has the shortest payback period. [...] The difficulty with the payback method is that it does not consider all cash flows and it fails to discount them. [page 28] We reject the payback method because it violates (at least) the first two of the four properties that are desirable in capital budgeting techniques.8 2. The Accounting Rate of Return The accounting rate of return (ARR) is the average after-tax profit divided by the initial cash outlay. It is very similar to (and in some uses exactly the same as) the return on assets (ROA) or the return on investment (ROI), and they suffer from the same deficiencies. [...] The problem with the ARR is that it uses accounting profits instead of cash flows and it does not consider the time value of money. [page 29] 4. Internal Rate of Return The internal rate of return (IRR) on a project is defined as that rate which equates the present value of the cash outflows and inflows. In other words, it is the rate that makes the computed NPV exactly zero. Hence this is the rate of return on invested capital that the project is returning to the firm. [page 30] If we use the IRR criterion and the projects are independent, we accept any project that has an IRR greater than the opportunity cost of capital, which is 10%. [page 36] The IRR rule errs in several ways. First, it does not obey the value-additivity principle, and consequently managers who use the IRR cannot consider projects, independently of each other. Second, the IRR rule assumes that funds invested in projects have opportunity costs equal to the IRR for the project. This implicit reinvestment rate assumption violates the requirement that cash (lows be discounted at the market-determined opportunity cost of capital. Finally, the IRR rule can lead to multiple rates of return whenever the sign of cash flows changes more than once. |
The source is given three times, but no quotation marks are used. |
| [146.] Svr/Fragment 071 01 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 71, Zeilen: 1-5 |
Quelle: Copeland Weston 1992 Seite(n): 28, 29, Zeilen: 28: last paragraph; 29: 14 ff. |
|---|---|
| [The NPV is computed by] discounting the cash flows at the firms opportunity cost of capital. The NPV method aims to find projects with a positive NPV (greater than zero). Copeland and Weston (1992: 28) state that the NPV of a project is exactly the same as the increase in shareholder's wealth. According to them, the NPV technique is the correct decision rule for capital budgeting purposes.
Copeland, T.E. & Weston, J.F. 1988, Financial Theory and Corporate Policy, 3rd ed., Addison-Wesley, Reading, Massachusetts. |
The net present value (NPV) criterion will accept projects that have an NPV greater than zero. The NPV is computed by discounting the cash flows at the firm’s opportunity cost of capital.
[page 29] The NPV of a project is exactly the same as the increase in shareholders' wealth. This fact makes it the correct decision rule for capital budgeting purposes. |
The source is given, but no quotation marks are used. |
| [147.] Svr/Fragment 071 12 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 71, Zeilen: 12-13, 17-32 |
Quelle: Schuyler 1992 Seite(n): 17, 18, Zeilen: 17: right col., 11 ff., 26 ff.; 18: left col., 3 ff. |
|---|---|
| 5.3.1 Decision Tree Analysis
A decision tree is a graphical extension of the Expected Value (EV) concept. [To calculate the expected value of a certain scenario, the values of the endpoints (possible scenario) are simply multiplied by the probabilities of reaching these endpoints. To consider the time value of money the value of each endpoint are discounted back to the present.] One of its strengths is that the tree diagram clarifies the decision problem with a visual approach. The diagram clearly shows all important decision elements, including contingencies (outcomes of chance events); decisions and alternatives, the logical sequence of decision points and chance events. One can often solve decision trees by hand, and the method is helpful at providing insights, especially related to the value of additional information and additional control. Branch and outcome values must be value measures (Present Value works, but, for example, internal rate of return (IRR) does not), and probabilities must be assessed or calculated for all chance event outcomes. One of the weaknesses of decision tree analysis is that one must represent all possibilities by a finite number of paths through the tree. This limits the practical number of random variables that can be accommodated, and one must use discrete distributions as approximations to continuous probability functions. Thus, range extremes are not represented. Other weaknesses of this approach include the fact that the analyst must limit the representation of uncertain time-spread events, such as for prices and inflation, to a few scenarios. Also, in [tree diagrams an output probability distribution (risk profile curve) is usually not obtained, only the EV.] |
[page 17]
1. Decision Tree Analysis—A decision tree is a graphical extension of the EV concept. Working from right to left, EV is back-calculated by:
The tree diagram clarifies the decision problem with a visual approach, one of its strengths. The diagram clearly shows all important decision elements, including contingencies (outcomes of chance events); decisions and alternatives; and the logical sequence of decision points and chance events. One can often solve decision trees by hand, and the method is helpful at providing insights, especially related to the value of additional information and additional control. One of the weaknesses of decision tree analysis is that one must represent all possibilities by a finite number of paths through the tree. This limits the practical number of random variables (chance events) that can be accommodated, and one must use discrete distributions as approximations to continuous probability functions; thus, range extremes are not represented. Other weaknesses of this approach include the fact that the analyst must limit the representation of uncertain time-spread events, such as for prices and inflation, to a few scenarios. Also, in tree diagrams an output probability distribution (risk profile curve) is usually not obtained, only the EV. [page 18] Branch and outcome values must be value measures [PV works, but, for example, internal rate of return (IRR) does not], and probabilities must be assessed or calculated for all chance event outcomes. |
The source is not given. |
| [148.] Svr/Fragment 072 01 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 72, Zeilen: 1-3 |
Quelle: Schuyler 1992 Seite(n): 17, 18, Zeilen: 17: right col., last paragraph; 18: left col., 1 ff. |
|---|---|
| [Also, in] tree diagrams an output probability distribution (risk profile curve) is usually not obtained, only the EV. However, with a modest extra effort, the distribution curve can be calculated by "rolling-forward" the tree. | [page 17]
Also, in tree diagrams an output probability distribution (risk profile curve) is usually not obtained, only the EV. However, [page 18] with a modest extra effort, the distribution curve can be calculated by “rolling-forward” the tree. |
The source is not given. |
| [149.] Svr/Fragment 072 09 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 72, Zeilen: 9-12 |
Quelle: Economist 1999 Seite(n): online, Zeilen: 0 |
|---|---|
| Options on real assets behave rather like options on financial assets (puts and calls on shares or currencies). The similarities are such that they can, at least in theory, be valued according to the same methodology. | Options on “real” assets (and indeed poker bets) behave rather like options on financial assets (puts and calls on shares or currencies, say). The similarities are such that they can, at least in theory, be valued according to the same methodology. |
The source is not given. |
| [150.] Svr/Fragment 073 09 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 73, Zeilen: 9-12 |
Quelle: Strassmann 1985 Seite(n): 100, Zeilen: 11 ff. |
|---|---|
| Strassmann (1985: 100) stated that when executives where [sic] asked about the mayor [sic] problems encountered in IT productivity projects, they emphasized that productivity was very difficult to measure, especially when the objectives where [sic] qualitative.
Strassmann, P.A. 1985, Information Payoff: Transformation of Work in the electronic age, Free Press, New York. |
When executives were asked about the major problems encountered in implementing productivity projects, they emphasized that productivity was very difficult to measure, especially when the objectives were qualitative.1
1 [...] |
The source is given, but no quotation marks are used. |
| [151.] Svr/Fragment 074 03 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 74, Zeilen: 3-6 |
Quelle: Copeland Weston 1992 Seite(n): 41, Zeilen: 18 ff. |
|---|---|
| This chapter showed that in the case of investment under certainty other decision criteria than the NPV method, such as the payback method the ARR, and the IRR, do not necessarily guarantee undertaking projects that maximize shareholder's wealth (Copeland and Weston 1992: 41).
Copeland, T.E. & Weston, J.F. 1988 [sic], Financial Theory and Corporate Policy, 3rd ed., Addison-Wesley, Reading, Massachusetts. |
Other decision criteria, such as the payback method, the accounting rate of return, and the IRR, do not necessarily guarantee undertaking projects that maximize shareholders' wealth. |
The source is given, but it is not made clear that a sequence of 20 words is copied verbatim; no quotation marks. |
| [152.] Svr/Fragment 074 12 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 74, Zeilen: 12-17 |
Quelle: Trigeorgis 1993 Seite(n): 205, Zeilen: left col., 1 ff. |
|---|---|
| Trigeorgis (1993) points out that early critics (Dean, Hayes and Abernathy, and Hayes and Garvin) also recognized that standard DCF criteria often undervalued investment opportunities, leading to myopic decisions, underinvestment and eventual loss of competitive position, because they either ignored or did not properly value important strategic considerations.
Trigeorgis, L. 1993, “Real Options and Interactions with Financial Flexibility”, Financial Management, vol. 22, no. 3, pp. 202-224. |
Garvin [36] recognized that standard discounted cash flow (DCF) criteria often undervalued investment opportunities, leading to myopic decisions, underinvestment and eventual loss of competitive position, because they either ignored or did not properly value important strategic considerations.
36. R. Hayes and D. Garvin. "Managing as if Tomorrow Mattered." Harvard Business Review (May-June 1982). pp. 71-79 |
The source is given, but no quotation marks are used. |
| [153.] Svr/Fragment 074 19 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 74, Zeilen: 19-21 |
Quelle: Coy 1999 Seite(n): online, Zeilen: 0 |
|---|---|
| A revolutionary concept is emerging in corporate finance called real options theory. In a nutshell, it says that when the future is highly uncertain, it pays to have a broad range of options open. | A revolutionary concept in corporate finance called “real options theory.” In a nutshell, it says that when the future is highly uncertain, it pays to have a broad range of options open. |
No source is given. |
| [154.] Svr/Fragment 075 08 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 75, Zeilen: 8-12, 101-102 |
Quelle: Copeland Weston 1992 Seite(n): 241, 251, Zeilen: 241: 27 ff.; 251: 17 ff. |
|---|---|
| [5.5.2 The Formula]
The formula for pricing European call options1, c, on financial assets developed by Black and Scholes (1973) has been described as a function of five parameters: The price of the underlying asset, S; the instantaneous variance of the assets returns, σ2 ; the exercise price, X; the time to expiration, t; and the risk-free rate, rf.
1 European options can only be exercised upon their maturity, as opposed to American options, which can be exercised at any date up to maturity. Black, F. & Scholes, M. 1973, “The Pricing of Options and Corporate Liabilities”, Journal of Political Economy, vol.81, pp. 637-654 (May – June 1973). |
[page 251]
F. SOME DOMINANCE THEOREMS THAT BOUND THE VALUE OF A CALL OPTION The value of a call option has been described as a function of five parameters: the price of the underlying asset, S; the instantaneous variance of the asset returns, σ2; the exercise price, X; the time to expiration; T; and the risk-free rate, rf: c = f(S, σ2, X, T, rf). (8.1) [page 241] B. A DESCRIPTION OF THE FACTORS THAT AFFECT PRICES OF EUROPEAN OPTIONS To keep the theory simple for the time being, we assume that all options can be exercised only on their maturity date and that there are no cash payments (such as dividends) made by the underlying asset. Options of this type are called European options. They are considerably easier to price than their American option counterparts, which can be exercised at any date up to maturity. |
The actual source is not given. The comparison shows that passages like the listed ones below cannot be found in Black and Scholes (1973):
The text following this fragment is taken from another source, but again not from Black and Scholes (1973), despite the given reference, see Fragment 075 13. |
| [155.] Svr/Fragment 075 13 |
| KeineWertung |
|---|
| Untersuchte Arbeit: Seite: 75, Zeilen: 13-20 |
Quelle: Brealey Myers 1981 Seite(n): 439, Zeilen: 29 ff. |
|---|---|
The exact Black and Scholes (1973) formula is expressed below:
N(d) is the probability that a normally distributed random variable will be less than or equal to d. |
Black and Scholes show that there is only one call price formula that meets that requirement. This unpleasant-looking formula is:
where
N(d) = cumulative normal probability density function15 EX = exercise price of option t = time to exercise date 15 That is, N(d) is the probability that a normally distributed random variable will be less than or equal to d. [page 430] P = price of stock now σ2 = variance per period of (continuously compounded) rate of return on the stock rf = (continuously compounded) risk-free rate of interest |
UNFERTIG [Anm. evtl. so oder so ähnlich sinnvoll?] The source is given, but only in a footnote text for the one sentence in the main text that follows this fragment. The comparison shows that passages like the listed ones cannot be found in Black and Scholes (1973):
|
| [156.] Svr/Fragment 077 07 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 77, Zeilen: 7-18 |
Quelle: Trigeorgis 1993 Seite(n): 205, Zeilen: right col, last paragraph |
|---|---|
| The actual valuation of options in practice has been greatly facilitated by Cox and Ross's (1976) recognition that an option can be replicated (or a "synthetic option" created) from an equivalent portfolio of traded securities. Thus, investors are independent of risk attitudes or capital market equilibrium considerations. Such risk-neutral valuation enables present-value discounting of expected future payoffs (with actual probabilities replaced with risk-neutral ones) at the risk-free interest rate, a fundamental characteristic of arbitrage-free price systems involving traded securities. Rubinstein (1976) further showed that standard option pricing formulas can be alternatively derived under risk aversion, and that the existence of continuous trading opportunities enabling a riskless hedge or risk neutrality, are not really necessary.
Cox, J. and Ross, S. 1976, "The Valuation of Options for Alternative Stochastic Processes," Journal of Financial Economics. 145-166 (January 1976). Rubinstein, M. 1976, "The Valuation of Uncertain Income Streams and the Pricing of Options," Bell Journal of Economics, pp. 407-425 (Autumn 1976). |
The actual valuation of options in practice has been greatly facilitated by Cox and Ross's [26] recognition that an option can be replicated (or a "synthetic option" created) from an equivalent portfolio of traded securities. Being independent of risk attitudes or capital market equilibrium considerations, such risk-neutral valuation enables present-value discounting, at the risk-free interest rate, of expected future payoffs (with actual probabilities replaced with risk-neutral ones), a fundamental characteristic of ’arbitrage-free” price systems involving traded securities. Rubinstein [87] further showed that standard option pricing formulas can be alternatively derived under risk aversion. and that the existence of continuous trading opportunities enabling a riskless hedge or risk neutrality are not really necessary.
26. J. Cox and S. Ross. "The Valuation of Options for Alternative Stochastic Processes." Journal of Financial Economics (January 1976). pp. 145-166. 87. M. Rubinstein. "The Valuation of Uncertain Income Streams and the Pricing of Options," Bell Journal of Economics (Autumn 1976), pp. 407-425. |
No quotation marks. The actual source is given on p. 74 and p. 81. |
| [157.] Svr/Fragment 077 19 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 77, Zeilen: 19-23, 25-30 |
Quelle: Brealey Myers 1981 Seite(n): 440, 442, Zeilen: 440: 6 ff.; 442: 2 ff. |
|---|---|
| As can be seen from the formula, the willingness of individuals to bear risk does not affect the option value, nor does the expected return on stock. The value of the stock increases with the level of the stock price to the exercise price (S/X), the time to expiration times the interest (rf t), and the time to expiration times the stock’s variability (σ2 t).
[5.5.3 Simplifying the calculation] The Black-Scholes option valuation formula, with all these mathematical expression, seems a little removed from the real world. However, every day dealers on the option exchanges have been using exactly this formula for years. These dealers are for the most part not trained in the formula’s mathematical derivations. Instead, they just use special computer programs or a set of tables to find the value of an option. |
Notice that the willingness of individuals to bear risk does not affect value, nor does the expected return on the stock.16 The value of the option increases with the level of the stock price relative to the exercise price (P/EX), the time to expiration times the interest rate (rft), and the time to expiration times the stock’s variability (σ2t).
16 [...] [page 442] Does the Black-Scholes option-valuation formula seem a little removed from the real world? It should not. Every day dealers on the Chicago Board Options Exchange use this formula to make huge trades. These dealers are not, for the most part, trained in the formula’s mathematical derivation; they just use a specially programmed calculator or a set of options tables to find the value of the option. |
The source is not given. |
| [158.] Svr/Fragment 078 02 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 78, Zeilen: 2-29 |
Quelle: Luehrman 1998 Seite(n): online, Zeilen: 0 |
|---|---|
| [Step 1: Calculating Cumulative Volatility]
When deferring an investment decision, the asset value may change and affect the investment decision for the better while waiting. That possibility is very important, but naturally it is difficult to quantify because of the uncertainty as to how the future asset values will change. The most common probability-weighted measure of dispersion is variance σ2. Variance is a summary measure of the likelihood of a random value far away from the average value. The higher the variance, the more likely it is that the values of an investment project will be either much higher or much lower than average. How much things can change while one waits, also depends on how long one can afford to wait. For business projects, things can change a lot more waiting two years than if waiting only two months. Thus the measure of the total amount of uncertainty is variance per period σ2 times the number of periods t. This is referred to as cumulative variance. Cumulative Variance = Variance per period x number of periods = σ2 t For mathematical convenience, instead of using the variance of project values, Luehrman (1998) suggests to use the variance of project returns, in other words to work with the percentage gained or lost per year. There is no loss of content because a project's return is completely determined by the project's value: Return = (Future Value minus Present Value) over Present Value The reason for doing this is that the probability distribution of possible values is usually quite asymmetric; value can increase greatly but cannot drop below zero. Returns, in contrast, can be positive or negative, sometimes symmetrically positive or negative, which makes their probability distribution easier to work with. Second, it helps to express uncertainty in terms of standard deviation σ, rather than variance σ2. Standard deviation, which is simply the square root of variance, expresses just as much about uncertainty as variance does, but it has the advantage of being denominated in the same units as the investment project being measured. Luehrman, T.A. 1998, “Investment opportunities as real options: Getting started on the numbers”, Harvard Business Review, vol. 76, no. 4, pp. 51 - 55 |
Quantifying Extra Value: Cumulative Volatility.
Now let’s move on to the second source of additional value, namely that while we’re waiting, asset value may change and affect our investment decision for the better. That possibility is very important, but naturally it is more difficult to quantify because we are not actually sure that asset values will change or, if they do, what the future values will be. [...] The most common probability-weighted measure of dispersion is variance, often denoted as sigma squared (σ 2 ). Variance is a summary measure of the likelihood of drawing a value far away from the average value in the urn. The higher the variance, the more likely it is that the values drawn will be either much higher or much lower than average. [...] We have to worry about a time dimension as well: how much things can change while we wait depends on how long we can afford to wait. For business projects, things can change a lot more if we wait two years than if we wait only two months. So in option valuation, we speak in terms of variance per period. Then our measure of the total amount of uncertainty is variance per period times the number of periods, or σ 2 t. This sometimes is called cumulative variance. An option expiring in two years has twice the cumulative variance as an otherwise identical option expiring in one year, given the same variance per period. Alternatively, it may help to think of cumulative variance as the amount of variance in the urn times the number of draws you are allowed, which again is σ 2 t. [...] First, instead of using the variance of project values, we’ll use the variance of project returns. In other words, rather than working with the actual dollar value of the project, we’ll work with the percentage gained (or lost) per year. There is no loss of content because a project’s return is completely determined by the project’s value:
The probability distribution of possible values is usually quite asymmetric; value can increase greatly but cannot drop below zero. Returns, in contrast, can be positive or negative, sometimes symmetrically positive or negative, which makes their probability distribution easier to work with. Second, it helps to express uncertainty in terms of standard deviation rather than variance. Standard deviation is simply the square root of variance and is denoted by o . It tells us just as much about uncertainty as variance does, but it has the advantage of being denominated in the same units as the thing being measured. |
The source is given, but it is not made clear that the text is so extensively copied - no quotation marks. |
| [159.] Svr/Fragment 080 13 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 80, Zeilen: 13-15 |
Quelle: Trigeorgis 1993 Seite(n): 206, Zeilen: left col., last paragraph |
|---|---|
| A series of papers gave a boost to the real options literature by focusing on valuing quantitatively, in many cases, deriving analytic, closed form solutions. A variety of real options scenarios have been analyzed in isolation. | There came a series of papers which gave a boost to the real options literature by focusing on valuing quantitatively — in many cases, deriving analytic, closed-form solutions— one type after another of a variety of real options, although each option was typically analyzed in isolation. |
No source is given. |
| [160.] Svr/Fragment 081 10 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 81, Zeilen: 10-12, 14-22 |
Quelle: Trigeorgis 1993 Seite(n): 206, 207, Zeilen: 206: right col., 29 ff.; 207: left col., 7 ff. |
|---|---|
| Despite its enormous theoretical contribution, the focus of the earlier literature on valuing individual real options (i.e., one type of option at a time) has nevertheless limited its practical value. [...] Real-life projects are often more complex in that they involve a collection of multiple real options whose values may interact (Trigeorgis 1993). Trigeorgis (1991) presents the valuation of options to defer, abandon, contract or expand investment, and switch use in the context of a generic investment, first with each option in isolation and later in combination. He shows, for example, that the incremental value of an additional option, in the presence of other options, is generally less than its value in isolation and declines as more options are present. More generally, he identifies situations where option interactions can be small or large and negative as well as positive.
Trigeorgis, L. 1991, "A Log-Transformed Binomial Numerical Analysis Method for Valuing Complex Multi-Option Investments," Journal of Financial and Quantitative Analysis, pp. 309-326 (September 1991). Trigeorgis, L. 1993, “Real Options and Interactions with Financial Flexibility”, Financial Management, vol. 22, no. 3, pp. 202-224. |
Despite its enormous theoretical contribution, the focus of the earlier literature on valuing individual real options (i.e., one type of option at a time) has nevertheless limited its practical value. Real-life projects are often more complex in that they involve a collection of multiple real options whose values may interact.
[page 207] Using a numerical analysis method suitable for valuing complex multi-option investments (Trigeorgis [104]), he presents the valuation of options to defer, abandon, contract or expand investment, and switch use in the context of a generic investment, first with each option in isolation and later in combination. He shows, for example, that the incremental value of an additional option, in the presence of other options, is generally less than its value in isolation and declines as more options are present. More generally, he identifies situations where option interactions can be small or large and negative as well as positive. 104. L. Trigeorgis, "A Log-Transformed Binomial Numerical Analysis Method for Valuing Complex Multi-Option Investments," Journal of Financial and Quantitative Analysis (September 1991), pp. 309-326. |
The source is given, but it is not made clear that the text is so extensively copied - no quotation marks. |
| [161.] Svr/Fragment 082 10 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 82, Zeilen: 10-15 |
Quelle: Economist 1999 Seite(n): online, Zeilen: 0 |
|---|---|
| The term of real option, unlike that of financial options, is usually open-ended or indefinable. The volatility of the underlying asset can be difficult to measure or guess, especially since it is not always clear what it is if, for example, it is yet to be invented. How can one define the appropriate benchmark asset class in the case of a new drug for a rare disease? And there may be additional variables to consider, such as the strategic benefit of pre-empting a rival. | Pricing financial options is daunting, but valuing real options is harder still. Their term, unlike that of financial options, is usually open-ended or undefinable. The volatility of the underlying asset can be difficult to measure or guess, especially since it is not always clear what it is — if, for example, it is yet to be invented. How can one define the appropriate benchmark asset-class in the case of a new drug for a rare disease? And there may be additional variables to consider, such as the strategic benefit of pre-empting a rival. |
The source is not given. |
| [162.] Svr/Fragment 082 16 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 82, Zeilen: 16-20 |
Quelle: Trigeorgis 1993 Seite(n): 207, Zeilen: left col., 25 ff. |
|---|---|
| In the more complex real-life option situations, such as those involving multiple interacting real options, analytic solutions may not exist and one may not even be always able to write down the set of partial differential equations describing the underlying stochastic processes. However, the ability to value such complex option situations has been enhanced by computing technology. | In the more complex real-life option situations, such as those involving multiple interacting real options, analytic solutions may not exist and one may not even be always able to write down the set of partial differential equations describing the underlying stochastic processes. The ability to value such complex option situations has been enhanced, however, with various numerical analysis techniques, many of which take advantage of risk-neutral valuation. |
No source is given. |
| [163.] Svr/Fragment 083 01 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 83, Zeilen: 1-21, 101 |
Quelle: Economist 1999 Seite(n): online, Zeilen: 0 |
|---|---|
| Getting the cash flow projections right (or even close) is staggeringly difficult. But it is even trickier to choose the correct discount rate. Conceptually, that rate is the opportunity cost of not investing in another project of similar systematic risk1. So the higher a project's risk, the higher its discount rate and the lower its NPV. The CAPM (Capital Asset Pricing Model) often spits out negative NPVs for many of the most exciting strategic opportunities.
The main reason for this shortcoming is that the model can use only information that is already known. For highly strategic investments that information is typically not much, and the resulting uncertainty tends to be reflected in an excessive discount rate. Combining an NPV calculation with decision trees (which assign numerical probabilities to various possible outcomes) may help, but not much. For each branch of the tree, the analyst still has to pick and apply an appropriate discount rate, and that of course was the problem in the first place. More fundamentally, the flaw in the CAPM is that it implicitly assumes that when firms buy new assets, they hold these passively for the life of the project. But they do not. Instead, they employ managers precisely in order to react to events as they unfold. Obviously, this managerial flexibility must be worth something. As with financial options, the longer the option lasts before it expires and the more volatile the price of the underlying asset the more the option is worth. This is in sharp contrast to the NPV, which deals harshly with both long time horizons and uncertainty. 1 Systematic risk is referred to risk that, in a large portfolio, cannot be diversified away. |
Getting the cash-flow projections right (or even close) is staggeringly difficult. But it is even trickier to choose the correct discount rate. Conceptually, that rate is the opportunity cost of not investing in another project of similar systematic risk (ie, risk that, in a large portfolio, cannot be diversified away). So the higher a project's risk, the higher its discount rate and the lower its NPV. But in practice, setting discount rates at the right level is almost impossible. The CAPM often spits out negative NPVs for many of the most exciting strategic opportunities.
The main reason for this shortcoming is that the model can use only information that is already known. That is typically not much, and the resulting uncertainty tends to be reflected in an excessive discount rate. Combining an NPV calculation with decision trees (which assign numerical probabilities to various possible outcomes) may help, but not much. For each branch of the tree, the analyst still has to pick and apply an appropriate discount rate, and that of course was the problem in the first place. More fundamentally, the flaw in the CAPM is that it implicitly assumes that when firms buy new assets, they hold these passively for the life of the project. But they do not. Instead, they employ managers precisely in order to react to events as they unfold. Obviously, this managerial flexibility must be worth something. [...] […] As with financial options, the longer the option lasts before it expires and the more volatile the price of the underlying asset — in this case, oil — the more the option is worth. This is in sharp contrast to the CAPM, which deals harshly with both long time horizons and uncertainty. |
The source is not given. Note that "NPV" = "Net Present Value" is a different concept than "CAPM" = "Capital Asset Pricing Model". |
| [164.] Svr/Fragment 085 03 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 85, Zeilen: 3-7 |
Quelle: Dixit Pindyck 1994 Seite(n): 28, Zeilen: 24 ff. |
|---|---|
| According to Dixit and Pindyck (1994) two things are needed to introduce an opportunity cost into the NPV calculation: irreversibility and the ability to invest in the future as an alternative to investing today. The less time there is to delay, and the greater the cost of delaying, the less will irreversibility affect the investment decision. | Two things are needed to introduce an opportunity cost into the NPV calculation—irreversibility, and the ability to invest in the future as an alternative to investing today. [...] The less time there is to delay, and the greater the cost of delaying, the less will irreversibility affect the investment decision. |
The source is given, but no quotation marks are used. |
| [165.] Svr/Fragment 085 23 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 85, Zeilen: 23-26 |
Quelle: Coy 1999 Seite(n): online, Zeilen: 0 |
|---|---|
| Options Pricing Models are too complex to be worthwhile for minor decisions. And they are not useful for projects that require a full commitment right away, since the value of an option lies in the ability to spend a little now and decide later whether to forge ahead. | It’s too complex to be worthwhile for minor decisions. And it’s not useful for projects that require a full commitment right away, since the value of an option lies in the ability to spend a little now and decide later whether to forge ahead. |
No source is given. |
| [166.] Svr/Fragment 086 14 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 86, Zeilen: 14-17, 27-31 |
Quelle: Coy 1999 Seite(n): 118, 119, Zeilen: 118: right col. 1 ff., 39 ff.; 119: right col. 1 ff. |
|---|---|
| Experts had developed rules of thumb that simplify the formidable math behind options valuation, while making real options applicable in a broader range of situations. And consulting firms are aware of this technique as the Next Big Thing to sell clients.
[...] A traditional calculation of net present value discounts projected costs and revenues and examines the project as a whole and concludes it is a no-go, in case the NPV is negative. The real-options analysis will break the same project into stages and may conclude that it makes sense to fund at least the first stage. Real options analysis rewards flexibility, and that is what makes it more appropriate for [strategic investments with high levels of uncertainty, than today's standard decision-making tool, the NPV method.] |
[page 118]
Real-options analysis rewards flexibility—and that's what makes it better than today's standard decision-making tool, "net present value." [...] Experts have developed rules of thumb that simplify the formidable math behind options valuation, while making real options applicable in a broader range of situations. And consulting firms have latched on to the technique as the Next Big Thing to sell to clients. [page 119] THE NEW MATH IN ACTION [...] A traditional calculation of net present value, which discounts projected costs and revenues into today’s dollars, examines the project as a whole and concludes it’s a no-go. But a real-options analysis breaks it into stages and concludes it makes sense to fund at least the first stage. |
No source is given. |
| [167.] Svr/Fragment 087 07 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 87, Zeilen: 7-9 |
Quelle: Taudes et al 1999 Seite(n): 5, Zeilen: 101 ff. |
|---|---|
| Researches of IT managers have also shown that IT practitioner [sic] have problems when determining model parameters like the time series of costs and revenues of an IT project, or the appropriate discount rate for the NPV model. [“Consequently, simple, static models are often preferred to the NPV model, and important project decisions are based rather on intuition, experience and rule of thumb than on quantitative analysis." (Tam 1992 cited in Taudes, Feuerstein, Mild 1999).]
Taudes, A., Feurstein, M., & Mild, A. 1999, “How Option Thinking can Improve Software Platform Decision”, Working Paper No.38, [Online]. Available: http://www.wu-wien.ac.at/am Accessed: 11 Oct. 1999. |
2 A similar finding is reported in (Tam 1992): in a survey of IT managers, Tam finds that IT practitioners have problems when determining model parameters like the time series of costs and revenues of an IS [sic] project, or the appropriate discount rate for the NPV model. Consequently, simple, static models are often preferred to the NPV model, and important project decisions are based rather on intuition, experience and rule of thumb than on quantitative analysis. Tam Kar Yan „Capital Budgeting in Information Systems Development“ Information & Management, (23:6), December 1992, pp. 345-357. |
Only part of the literal quotation is marked as such. The reference to Tam (1992) is not listed in the bibliography of the dissertation. |
| [168.] Svr/Fragment 087 20 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 87, Zeilen: 20-27 |
Quelle: Rogers 1983 Seite(n): 1, 13, Zeilen: 1: 16 ff.; 13: 21 ff. |
|---|---|
| In general, a widespread adoption of a new technology like XML, even when it has obvious advantages, often takes a very long time. There is a wide gap in many fields, between what is known and what is actually put in use. According to Rogers (1983) technological innovations require a lengthy period, often of some years, from the time they become available, to the time where they are widely adopted, because they create uncertainty in the minds of potential adopters about the expected consequences.
Rogers, E.M. 1983, Diffusion of Innovations, 3rd ed., Collier Macmillan, London. |
ONE REASON WHY THERE IS SO MUCH INTEREST in the diffusion of innovations is because getting a new idea adopted, even when it has obvious advantages, is often very difficult. There is a wide gap in many fields, between what is known and what is actually put into use. Many innovations require a lengthy period, often of some years, from the time when they become available to the time when they are widely adopted.
[page 13] So a technological innovation creates one kind of uncertainty in the minds of potential adopters (about its expected consequences), as well as representing an opportunity for reduced uncertainty in another sense (that of the information base of the technology). |
The source is given, but the text similarity begins before the reference and continues quite closely after the reference. Thus it is not made clear to what extent the source was copied. |
| [169.] Svr/Fragment 088 18 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 88, Zeilen: 18-23 |
Quelle: Benaroch Kauffman 2000 Seite(n): 209, Zeilen: ricght col., 30 ff. |
|---|---|
| This paper is based on the assumption that every company today facing the XML/EDI investment decision is the holder of an American deferral option on a dividend-paying asset. The asset underlying this option is the potential stream of revenues from an investment opportunity that will materialize only when a company decides to invest in an XML/EDI project at any given future date, where the dividends are the revenues lost during deferral time. | Yankee possessed an American deferral option on a dividend paying asset. The asset underlying this option is the potential stream of revenues from an investment opportunity that will materialize only once Yankee enters the POS debit market any time starting in 1987, where the dividends are the revenues lost during the time Yankee deferred entry into this market. |
On the next page (p. 89, at the end of the second paragraph and after another reference) there is a reference to Benaroch and Kauffman (1999), but this is not listed in the bibliography of the dissertation. |
| [170.] Svr/Fragment 088 28 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 88, Zeilen: 28-30 |
Quelle: Benaroch Kauffman 2000 Seite(n): 210, Zeilen: left col., 25 ff. |
|---|---|
| The option value in this case is embedded in the possibility for any firm today to resolve some of the uncertainties concerning the adoption of the XML/EDI standard. A firm could passively observe the standard evolving and being applied [in the industry, and could actively try to lower the risk of expected revenues by preparing for an XML/EDI investment project at a future time.] | The option value stemmed from Yankee's belief that it could resolve some of the uncertainties concerning acceptance of POS debit services. [...] Yankee could passively observe how the POS debit business evolved in other parts of the country and it could actively try to lower the risk of expected revenues (e.g., lobby for a change in Massachusetts' law). |
The fragment continues on the next page. No source is given here. On the next page (p. 89, at the end of the second paragraph and after another reference) there is a reference to Benaroch and Kauffman (1999), but this is not listed in the bibliography of the dissertation. |
| [171.] Svr/Fragment 089 01 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 89, Zeilen: 1-10 |
Quelle: Benaroch Kauffman 2000 Seite(n): 209, 210, Zeilen: 209: right col., 39 ff.; 210: left col., 3 ff., 15 ff., 32 ff. |
|---|---|
| [A firm could passively observe the standard evolving and being applied] in the industry, and could actively try to lower the risk of expected revenues by preparing for an XML/EDI investment project at a future time.
This deferral option is obtained at no direct cost. Dixit and Pindyck (1994) believe that a company could obtain a deferral option at no cost if it faces no credible competitive threat of loosing the deferred investment opportunity. In the case of monopoly the only cost of deferring is the opportunity cost of delaying the entry. In cases other than monopoly, things are somewhat different. Full benefits of the option, exists for the market leader among two or more competitors. In the case of no market leader, all firms have the option, but only the first mover will enjoy full benefits. [Benaroch and Kauffman (1999) believe that this is the case for duopoly, I would rather extend it to any market structure other than monopoly.] Dixit, A.K. & Pindyck, R.S. 1994, Investment under Uncertainty, Princeton University Press, Princeton, New Jersey. |
[page 210, left col., 32 ff.]
Yankee could passively observe how the POS debit business evolved in other parts of the country and it could actively try to lower the risk of expected revenues (e.g., lobby for a change in Massachusetts' law). [page 209, right col., 39 ff.] Unlike a financial option that is purchased for a cash fee, Yankee obtained its deferral option at no direct cost. Generally, a firm can obtain a deferral option at no cost if it faces no credible competitive threat of losing the deferred investment opportunity (Dixit and Pindyck 1994). This is clearly true in the case of a monopoly. In case of a duopoly, the option exists for the "leader" among two competitors who made [page 210, left col., 3 ff., 15 ff.] indirect investments in building up, over time, managerial competencies, reputation, IT infrastructure, etc.; if there is no clear leader, both firms may have the option, but only the first mover would enjoy its full benefits. [...] Hence, as far as project valuation decision-making is concerned, Yankee's only option cost was the opportunity cost of delaying entry-the revenues lost during the deferral period-and a negligible opportunity cost borne by the slim risk of losing the investment opportunity to NYCE (which, counter to expectations, might act earlier than expected). Dixit, A. K., and Pindyck, R. S. Investment Under Uncertainty, Princeton University Press, Princeton, NJ, 1994. |
This fragment continues from the previous page. The actual source is not given. A short reference Benaroch and Kauffman (1999) can be found at the end of this passage, but is not listed in the bibliography of the dissertation. Despite these shortcomings this can be regarded as some sort of reference to the actual source. The fragment is categorized as a Bauernopfer (pawn sacrifice) because the source refers only to the last sentence in brackets without any indication that the text above it is taken from that source as well. |
| [172.] Svr/Fragment 090 08 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 90, Zeilen: 8-11 |
Quelle: Lucas 1999 Seite(n): 168, Zeilen: 19 ff. |
|---|---|
| Data required for option pricing models is difficult to estimate. This especially applies to the estimation of the variance in the expected return of an IT investment. In the case of a financial option, the variance is the variability of the underlying stock, which the option trader can obtain by option valuation. | From a practical standpoint the data required for options pricing models are just as difficult to develop as for an NPV analysis. You have to estimate the variance in the expected return on the IT investment. In the case of an options trader, the variance is the variability of the underlying stock. The options specialist obtains this information from a firm that clears trades; this firm calculates several measures of variance, or volatility, as it is known in options valuation. |
No source is given. |
| [173.] Svr/Fragment 092 05 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 92, Zeilen: 5-11, 16-18 |
Quelle: Lucas 1999 Seite(n): 31, 32, Zeilen: 31: last paragraph; 32: 1 ff. |
|---|---|
| A late project delays the benefits a company is expecting from investment. In the worst case, the project is too late to meet a competitive challenge or a deadline and ends up being cancelled. An overbudget reduces the return that one expected when deciding to make an investment in information technology. A small budget overrun is probably not a problem, but anything significant could dramatically alter the expected return on investment (Lucas, 1999: 31). [...] For better assessment of this parameter it would be helpful to have statistics on how late projects are on average, and how much they are over budget.
Lucas, H. 1999, Information technology and the productivity paradox: Assessing the value of investing in IT, Oxford University Press, New York. |
It would be helpful to have statistics on how late projects are on average, and how much they are over budget. A late project delays the benefits that you
[page 32] are expecting from your investment. In the worst case, the project is too late to meet a competitive challenge or a deadline and ends up being canceled like the PG&E system above. An over-budget project reduces the return that you expected when deciding to make an investment in information technology. A small overrun is probably not a problem, but anything significant could dramatically alter the expected return on investment (ROI). |
The source is given, but no quotation marks are used. |
| [174.] Svr/Fragment 093 01 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 93, Zeilen: 1-3, 8-10, 13-14, (17-26) |
Quelle: Lucas 1999 Seite(n): 32, 33, 47, Zeilen: 32: 16 ff., 31 ff.; 33: 1 ff.; 47: 4 ff. |
|---|---|
| While not excusing cost and time overruns, the prudent manager should factor their likehood [sic] into any return on investment calculations (Lucas, 1999: 32).
[...] According to Weill (1990) not every IT project is successful because management does not always take advantage of the opportunities that such an investment provides. [...] Conversion effectiveness measures the ability of an organization to convert its IT investments into working applications. [...] [Lucas (1999) stated many variables that determine conversion effectiveness. He believes that a failure on any one of the parameters listed below can doom the projects, even if every other aspect of development is successful. The variables he quotes are: (1) Size and scope of project, (2) Amount of unknown technology involved, (3) Project management, (4) Support and encouragement of managers, sponsorship, (5) The urgency of the problem/opportunity addressed by the technology, (6) Norms in the organization, (7) User commitment and involvement, (8) Technical development environment, (9) Quality IT staff, (10) Strength of project team, (11) Level of expertise of participants, (12) Type of technology employed, (13) Type of application, (14) Amount of custom code written, (15) [Nature of packaged software included, (16) Use of external consultants, (17) Degree of understanding between users and developers, (18) Presence of a project champion, (19) Senior management involvement, (20) Amount of organizational change required, (21) Threat to existing personnel, vested interests, (22) User’s view of the quality of the system.]] Lucas, H. 1999, Information technology and the productivity paradox: Assessing the value of investing in IT, Oxford University Press, New York. Weill, P. 1990, The relationship between investment in Information Technology and Firm Performance: A study of the valve manufacturing sector, University of Melbourne, Graduate School of Management, Parkville, Victoria. |
While not excusing cost and time overruns, the prudent manager should factor their likelihood into any return on investment calculations.
[...]
[page 33]
There are many variables that partially determine conversion effectiveness. A failure on any one of the items listed above can doom a project, even if every other aspect of development is successful. [page 47] Conversion effectiveness measures the ability of an organization to convert its IT investments into working applications. Not every development effort is successful, and management does not always take advantage of the opportunities that an IT initiative provides. Weill chose to measure conversion effectiveness in this study by ratings of top management commitment, experience with IT, user satisfaction, and the turbulence of the internal political environment. |
The source is given twice, but no quotation marks are used. The last paragraph is only documented here, but conservatively not considered in the statistics. |
| [175.] Svr/Fragment 094 23 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 94, Zeilen: 23-26 |
Quelle: Strassmann 1985 Seite(n): 79, Zeilen: 3 ff. |
|---|---|
| Installing Information technology involves much greater expense than just buying the hardware and software. Extensive human resources and business process redesign is required to support an IT System before it can be productive to use. Very often, the most costly elements of such support are not technological but [organizational. This fact has far reaching implications for the ways that information technology investments should be managed (Strassmann 1985: 79).]
Strassmann, P.A. 1985, Information Payoff: Transformation of Work in the electronic age, Free Press, New York. |
Installing information technology in the office environment involves a much greater expense than just buying a workstation to be placed on a desk. Extensive resources are required to support an electronic workstation before it can be put to productive use. The most costly elements of such support are not technological but organizational. This fact has far-reaching implications for the ways that information-technology investments should be managed. |
The source is given, but no quotation marks are used, although the text is mainly copied word-for-word. |
| [176.] Svr/Fragment 095 16 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 95, Zeilen: 16-21 |
Quelle: Lucas 1999 Seite(n): 39, Zeilen: 21 ff., 28 ff. |
|---|---|
| For IT investments that offer a direct return by definition, estimates are not too difficult. When looking at a case of indirect returns, they are much more difficult to define and measure. What is the estimated return for a system that is a competitive necessity? What is the estimated return for technology when it is the only way to do the business? Some experts suggest that one should look at the cost of not investing. | For applications that offer a direct return, by definition estimates are not too difficult. When we look at a case of indirect returns later in the book, we shall see how difficult it is to define and measure these kinds of benefits. [...]
What is the estimated return for a system that is a competitive necessity? What is the estimated return for technology when it is the only way to do the job? Some experts suggest that you should look at the cost of not investing. |
The source is not given. |
| [177.] Svr/Fragment 096 11 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 96, Zeilen: 11-28 |
Quelle: Sassone Schwartz 1986 Seite(n): 83, 84, 86, Zeilen: 83: center col. 3 ff., right col. last paragraph; 84: left col., 1 f.; 86: right col., 3 ff. |
|---|---|
Unlike large data processing systems whose values lie in their capacity to substitute computer power for routine labor, “office automation is a complementary technology” (Sassone and Schwartz 1986: 83).
Office automation tools embody two kinds of benefits: (1) increased efficiency and (2) increased effectiveness. Increased efficiency is referred to shorter time needed to accomplish a given task, or allow more of a given task to be done in the same amount of time. Increased effectiveness results from increased efficiency, which allows restructuring of work. Managers and professionals can spend more time performing activities reflected in their titles and time rather that to support, clerical and non-productive (lower-productive) activities. Quantifying this shift in working profiles uses a two-part procedure. First, a method called the Work Profile Analysis identifies the working profiles of the employees affected by the introduction of a new technology. The results thereof are then build into a computer simulation called the Hedonic Wage Model, which is basically a set of multiple linear equations. The whole model is based on the assumption, that jobs are not monolithic but have identifiable components with different implicit values. Sassone, P.G. & Schwartz, A.P. 1986, “Cost Justifying OA: A straightforward Method for Quantifying the Benefits of Automated Office Systems”, Datamation, pp. 83-88 (February 1986). |
[page 83]
Unlike a large data processing system whose value lies in its capacity to substitute computer power for routine labor, office automation technology is a complementary technology. Its value lies in its power to complement, or enhance, a professional’s performance. Office automation tools embody two kinds of benefits: the first is that they shorten the time needed to accomplish a given task, or allow more of a given task to be done in the same amount of time. This is usually referred to as increased efficiency. The second benefit is that they allow restructuring of work. In other words, managers and professionals can spend more time performing activities reflected in their titles and less time on support, clerical, and nonproductive activites. This is referred to as increased effectiveness. [...] We use a two-part procedure that involves a method of measuring activity called Work Profile Analysis. We then build the results of this into a computer simulation called the He- [page 84] donic Wage Model, which captures what you need to know in dollars and cents. [page 86] Similarly, we recognize that jobs are not monolithic, but have identifiable components with different implicit values. |
The source is only given for a short (and incomplete) literal quote, but it does not become clear that the copying is continued after the reference. |
| [178.] Svr/Fragment 097 01 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 97, Zeilen: 1-11 |
Quelle: Sassone Schwartz 1986 Seite(n): 84, 86, Zeilen: 84: right col., 8 ff.; 86: right col., 11 ff. |
|---|---|
| [Furthermore it is assumed that workers are worth what they cost in company: salaries, fringe] benefits and direct overheads. Their worth can be thought of as the weighted values of their activities that they perform. The weights are the percentages in the Work Profile Matrix. The values of the initial activities are unknown, but are determined through the hedonic wage model. By using the hedonic model to explain the value of the job in terms of the amounts of each component the job entails, interferences about the implicit values of each component can be drawn (Sassone and Schwartz 1986:84).
In cases where a new IT Systems (in particular an XML investment) may induce changes in the composition of a job or work profile, the hedonic values can be used to place a monetary value on that change (Ucomp), and hence on the information system itself. |
First, an assumption: we assume that workers are worth what they cost the company in wages, salaries, benefits, and overhead. Their worth can be thought of as the weighted values of the activites that they perform. The weights are the percentages in the Work Profile Matrix, illustrated in Fig. 3. The values of the activities are initially unknown, but are determined through the Hedonic Wage Model.
[page 86] By using the hedonic model to explain the value of the job (salary plus fringe benefits plus direct overhead) in terms of the amounts of each component the job entails, we can draw inferences about the implicit value of each component. Since office information systems permit changes in the composition of a job or work profile, expressed in percent, the implicit, or hedonic, values can be used to place a dollar value on that change, and hence on the information system itself. |
The source is given, but no quotation marks are used. It is also not clear that the copying is continued after the in-text reference. |
| [179.] Svr/Fragment 097 18 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 97, Zeilen: 18-24 |
Quelle: Lucas 1999 Seite(n): 51, 82, Zeilen: 51: 6 ff.; 82: 19 ff. |
|---|---|
| In general, the greater the distance in business process between where the investment occurs and where benefits appear, the more likely that the benefits are indirect (or strategic) (Lucas, 1999: 82). When IT acts as a substitute for labor, a cost-benefit methodology is quite appropriate. However, when IT enhances the quality of a product by reducing cycling time or by adding value through services of [sic] information content, economic methods of analysis encounter problems (Lucas 1999: 51).
Lucas, H. 1999, Information technology and the productivity paradox: Assessing the value of investing in IT, Oxford University Press, New York. |
[page 82]
In general, the greater the distance in business process terms between where the investment occurs and where benefits appear, the more likely that the benefits are “indirect. ” [page 51] For this kind of study, when IT acts as a substitute for labor, a cost-benefit methodology is quite appropriate. However, when IT enhances the quality of a product by reducing cycle time or by adding value through service or information content, economic methods of analysis encounter problems. |
The source is given, the pages are correctly quoted. The only thing missing is quotation marks. |
| [180.] Svr/Fragment 098 10 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 98, Zeilen: 10-17 |
Quelle: Lucas 1999 Seite(n): 169, Zeilen: 1 ff. |
|---|---|
| For an IT investment, one must estimate the costs required to develop a project at the expiration date of the option, when you might undertake the investment. For an option three years in [sic] future, the analyst has to estimate how much investment would be required. Many parameters influence this cost, including the pace of technological change. In 3 years a package might come along like SAP that dramatically changes the cost of an investment (Lucas 1999: 169).
Lucas, H. 1999, Information technology and the productivity paradox: Assessing the value of investing in IT, Oxford University Press, New York. |
For an IT investment, you must estimate the investment required to develop a project at the expiration date of the option, that is, at the time you might be undertaking the project. For an option three years in the future, the analyst has to estimate how much investment would be required. Many variables influence this cost, including the pace of technological change. In three years, a package might come along like SAP that dramatically changes the cost of an investment. |
The source is given, but no quotation marks are used. |
| [181.] Svr/Fragment 099 08 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 99, Zeilen: 8-11 |
Quelle: Reinganum 1981 Seite(n): 395, Zeilen: 28 ff. |
|---|---|
| Although waiting to invest into XML/EDI costs the firm more in terms of forgone [sic] profits, it may save money on the cost of implementing the new standard. Thus the firm must weight [sic] the costs and benefits of delaying adoption, as well as take account of the rivals’ strategic behavior. | Therefore, although waiting costs the firm more in terms of foregone profits, it may save money on the cost of purchasing the new technology. Thus the firm must weigh the costs and benefits of delaying adoption, as well as take account of its rival's strategic behavior. |
No source is given. No quotation marks. |
| [182.] Svr/Fragment 099 27 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 99, Zeilen: 27-29 |
Quelle: Jaakkola 1996 Seite(n): 65, Zeilen: 22 ff. |
|---|---|
| [6.3.1 Determining Diffusion]
According to Rogers (1983:3) “the diffusion of an innovation is a process, in which the innovation spreads through certain channels in the social system (target population) in time. The diffusion (of a new technology) is the evolutionary process [of replacement of an old technology for solving similar problems or accomplishing similar objectives.”] Rogers, E.M. 1983, Diffusion of Innovations, 3rd ed., Collier Macmillan, London. |
1 INTRODUCTION
The diffusion of an innovation is a process, in which the innovation spreads through certain channels in the social system (target population) in time (Rogers 1983, p.5). According to Ayres (1969, p. xii) diffusion (of a new technology) is the evolutionary process of replacement of an old technology by a newer one for solving similar problems or accomplishing similar objectives. Ayres, Robert U. (1969) Technological Forecasting and Long-Range Forecasting. McGraw-Hill Book Company, New York. Rogers, E. (1983) Diffusion of Innovations. The Free Press, New York. |
This passage feigns being a literal quotation, but it is not. As can be seen, the text is not taken from Rogers 1983 (p. 3 has an entirely different content), but from Jaakkola 1996. At the beginning of the chapter What Is Diffusion? on page 5 of Rogers 1983, only a similiar statement can be found:
|
| [183.] Svr/Fragment 100 18 |
| KeineWertung |
|---|
| Untersuchte Arbeit: Seite: 100, Zeilen: 18-23, 24-28 |
Quelle: Rogers 1962? / Rogers 1983? / Arledge 1986? / Rogers/Scott 1997? Seite(n): -, Zeilen: - |
|---|---|
| Rogers (1962) classifies adopters of innovation into 5 categories: (1) Innovators are hazardous, rash, daring, and risky. (2) Early Adopters have the role of decreasing uncertainty about an innovation. (3) Early Majority adopts new ideas just before the average member of the social system. They follow with deliberate willingness in adopting innovations, but seldom lead. (4) Late majority adopt new ideas just after the average member of a social system. [...] Innovations are approached with a skeptical and cautious air. Their relatively scarce resources mean that almost all of the uncertainty about a new idea must be removed before the late majority feels that it is safe to adopt. (5) Laggards are the last in the social system to adopt an innovation.
Rogers, E.M. 1962, Diffusion of Innovations, Freepress of Glencoe, New York. |
tja ... |
...
|
| [184.] Svr/Fragment 101 01 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 101, Zeilen: 1-8 |
Quelle: Bass 1969 Seite(n): 215, 216, 226, Zeilen: 215: 8 ff.; 216: 1 f.; 226: 23 ff. |
|---|---|
| Bass (1969) developed a growth model for the timing of initial purchase of new products and empirically tested it against data of eleven consumer durables. The basic assumption of his model is that the probability of purchase at any time is related linearly to the number of previous buyers. The model implies exponential growth of initial purchases to a peak and then exponential decay. Innovative and imitative behavior is the underlying behavioral rationale for the model. According to Bass Innovators are individuals who decide to adopt an innovation independently of the decision of other individuals in a social system.
Bass, F.M. 1969, “A new Product Growth for Model Consumer Durables”, Management Science, vol.15, no 5, pp. 215-227 (January 1969). |
[page 215, Abstract]
[page 216] Some individuals decide to adopt an innovation independently of the decisions of other individuals in a social system. [page 226] Conclusion The growth model developed in this paper for the timing of initial purchase of new products is based upon an assumption that the probability of purchase at any time is related linearly to the number of previous buyers. There is a behavioral rationale for this assumption. The model implies exponential growth of initial purchases to a peak and then exponential decay. |
The source is given, but no quotation marks are used. It does not become clear to the reader that the author uses Bass' words almost completely without adding any own content. |
| [185.] Svr/Fragment 102 01 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 102, Zeilen: 1-7 |
Quelle: Mansfield 1961 Seite(n): 763, Zeilen: 4 ff. |
|---|---|
| [6.3.3 Parameters that Influence Diffusion
Mansfields (1961) model builds largely around one hypothesis – “that the probability that a firm will introduce a new technique is an increasing function of the proportion of firms already using it and the profitability of doing so, but a decreasing function of the size of investment required” (1961: 762-763).] His studies showed that the rate of imitation tended to be faster for innovations that were more profitable and that required relatively small investments. Several other factors showed very low statistical significance: There was some apparent tendency for the rate of imitation to be higher when the innovation did not replace very durable equipment, and when the firms’ output was growing rapidly, and when the innovation was introduced in the more recent past. Mansfield, E. 1961, “Technical Change and the Rate of Imitation”, Econometrica, vol. 29, no. 4, pp. 741-765. |
As expected, the rate of imitation tended to be faster for innovations that were more profitable and that required relatively small investments. [...]
[...] When several other factors are included in the model, the empirical results are largely inconclusive. There was some apparent tendency for the rate of imitation to be higher when the innovation did not replace very durable equipment, when the firms’ output was growing rapidly, and when the innovation was introduced in the more recent past. |
Quotation marks are given for a literal quote at the beginning, but quotation marks would have also been appropriate for the following text which is copied from the same source as well. |
| [186.] Svr/Fragment 102 08 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 102, Zeilen: 8-19 |
Quelle: Rogers 1983 Seite(n): 15, 16, Zeilen: 15: 6 f., 15 ff., 24 f., 33 f.; 16: 3 ff. |
|---|---|
| Rogers (1962) explains the different rates of adoption by introducing 5 characteristics of Innovation: (1) Relative advantage: is the degree to which an innovation is perceived as better than the idea it supersedes. (as opposed to objective advantage) (the greater strategic advantage the faster it will be adopted); (2) Compatibility: is the degree to which an innovation is perceived as being consistent with the existing values, past experiences, and needs of potential adopters. (if not compatible, not adopted as fast); (3) Complexity: is the degree to which an innovation is perceived as difficult to understand and use. ( the simpler the faster the adoption); (4) Triability: is the degree to which an innovation may be experimented with on a limited basis (triability-> less uncertainty -> faster adoption); (5) Observability: is the degree to which the result of an innovation are visible to others ( the more visible, the more likely that they will adopt.
Rogers, E.M. 1962, Diffusion of Innovations, Freepress of Glencoe, New York. Rogers, E.M. 1983, Diffusion of Innovations, 3rd ed., Collier Macmillan, London. |
[page 15]
1. Relative advantage is the degree to which an innovation is perceived as better than the idea it supersedes. [...] It does not matter so much whether an innovation has a great deal of “objective” advantage. [...] The greater the perceived relative advantage of an innovation, the more rapid its rate of adoption is going to be. 2. Compatibility is the degree to which an innovation is perceived as being consistent with the existing values, past experiences, and needs of potential adopters. An idea that is not compatible with the prevalent values and norms of a social system will not be adopted as rapidly as an innovation that is compatible. [...] 3. Complexity is the degree to which an innovation is perceived as difficult to understand and use. [...] In general, new ideas that are simpler to understand will be adopted more rapidly [...] 4. Trialability is the degree to which an innovation may be experimented with on a limited basis. [...] An innovation that is trialable represents less uncertainty [...] [page 16] 5. Observability is the degree to which the results of an innovation are visible to others. The easier it is for individuals to see the results of an innovation, the more likely they are to adopt. |
Svr includes two versions of Rogers' book, the first and the third edition, in the reference section. On this page the source is given as the first edition, however the text is quite close to the definitions given in the improved and extended third edition. The definitions from the first edition are as follows: Rogers (1962):
Still, since the author is named although the wrong edition is noted, this fragment will be classified as a pawn sacrifice. |
| [187.] Svr/Fragment 102 25 |
| KeineWertung |
|---|
| Untersuchte Arbeit: Seite: 102, Zeilen: 25-30 |
Quelle: Fisher Pry 1971 Seite(n): 75, Zeilen: 30 ff. |
|---|---|
| Fisher and Pry (1971) developed a substitutional model of technological change based on three assumptions: (a) many technological advances can be considered as competitive substitutions of one method of satisfying a need for another. (b) If a substitution has progressed as far as a few percent, it will proceed to completion. (c) The fractional rate of fractional substitution of new for old is proportional to the remaining amount of the old left to be substituted.
Fisher, J.C. & Pry, R.H. 1971, “A Simple Substitution Model of Technological Change”, Technological Forecasting and Social Change, vol.3, pp. 75-88. |
The model is based on three assumptions: (1) Many technological advances can be considered as competitive substitutions of one method of satisfying a need for another. (2) If a substitution has progressed as far as a few percent, it will proceed to completion. (3) The fractional rate of fractional substitution of new for old is proportional to the remaining amount of the old left to be substituted.1
1 A special form of Pearl's law; cf. Raymond Pearl, The Biology of Population Growth (New York: Alfred A. Knopf, 1925). |
Source is given. No quotation marks, however. |
| [188.] Svr/Fragment 103 18 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 103, Zeilen: 18-28 |
Quelle: Reinganum 1981 Seite(n): 395, Zeilen: 21 ff., 31 ff. |
|---|---|
| These results are based on a previous paper, Reinganum (1981a), where she assumes that firms are operating at Nash Equilibrium1 output levels, generating a market price and profit allocations. When a cost-reducing innovation is announced, each firm must determine when (if ever) to adopt it, based in part upon the behavior of the rival firm. If either firm adopts before the other, it can expect to make substantial profits on the expense of the other firm. On the other hand the discounted sum of purchase price and adjustment costs may decline with the lengthening of the adjustment period as various quasi-fixed factors become more easily variable. Reinganum analyzes the case of identical firms, and non-identical firms. She shows that there exist two asymmetric1 Nash equilibria in pure strategies. In both cases, at Nash equilibrium, one firm will adopt the innovation at [a relatively early date, the other relatively later.]
1 A Nash equilibrium is a situation in which each firm is doing the best it can given the behaviour of its rivals (applied to Oligopoly and Duoploy situations, where interdependece of market price and output levels between market players is big). Reinganum, J. F. 1981a, “On the Diffusion of New Technology: A game Theoretic apprach”, Review of Economic Studies, Vol. 48, 1981, pp. 395 – 405. |
Nash equilibrium output levels, generating a market price (given demand) and profit allocations. When a cost-reducing innovation is announced, each firm must determine when (if ever) to adopt it, based in part upon the discounted cost of implementing the new technology, and in part upon the behavior of the rival firm. If either firm adopts before the other, it can expect to make substantial profits at the expense of the other firm. On the other hand, the discounted sum of purchase price and adjustment costs may decline with the lengthening of the adjustment period as various quasi-fixed factors become more easily variable. [...] In Section 3 it is shown that there exist two asymmetric Nash equilibria in pure strategies. That is, at a Nash equilibrium, one firm will adopt the innovation at a relatively early date, the other relatively later. Thus even in the case of identical firms and complete certainty, there is a "diffusion" of innovation over time. |
The source is given, but no quotation marks are used. |
| [189.] Svr/Fragment 104 01 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 104, Zeilen: 1-2 |
Quelle: Reinganum 1981 Seite(n): 395, Zeilen: 34 f. |
|---|---|
| Thus even in the case of identical firms and complete certainty, there is a diffusion of innovation over time. | Thus even in the case of identical firms and complete certainty, there is a "diffusion" of innovation over time. |
The source is given on the previous page. No quotation marks are used. |
| [190.] Svr/Fragment 104 03 |
| BauernOpfer |
|---|
| Untersuchte Arbeit: Seite: 104, Zeilen: 3-6, 8-11, 13-18, 21-27 |
Quelle: Quirmbach 1986 Seite(n): 33, 34, Zeilen: 33: abstract, 21 ff.; 34: 9 ff., 29 ff. |
|---|---|
| Quirmbach (1986) shows that the diffusion of capital embodies process innovation results from a pattern of decreasing incremental benefits and decreasing adoption costs for later adoptions. He develops a method for comparing diffusion rates for different market structures in the capital equipment market. [...] For all market structures compared, he establishes that if the incremental benefits resulting from the kth adoption are larger under market structure A than under market structure B, then the kth adoption will occur sooner under A than under B. [...] In his studies he concludes that market power makes a difference in diffusion rates, and on which side of the market that power lies makes a considerable difference. Adapting the model of Reinganum (1981a, b) he concludes that contrary to Reinganums assumption, strategic behavior is inessential to the result of a diffusion process. Solely the patterns of incremental benefits and adoption costs are the key to the difference in diffusion rates. [...]
The explanation for the paradox between Reinganum and Quirmbachs findings is that Reinganum analyzes increases in structural concentration in the user industry while continuing to assume non-cooperative behavior of the market players, whereas Quirmbach analyzes collusive conduct of market players. Reinganum studies the increases in market share of each firm and thus the profits to a given firm’s adoption. Quirmbach (1986) criticizes that she fails to internalize the negative externalities that new adoptions visit on existing investments. Quirmbach, H.C. 1986, “The Diffusion of New Technology and the Market for an Innovation”, Rand Journal of Economics, Vol.17, No.1, Spring 1986, pp. 33–47. Reinganum, J. F. 1981a, “On the Diffusion of New Technology: A game Theoretic apprach [sic]”, Review of Economic Studies, Vol. 48, 1981, pp. 395 – 405. Reinganum, J. F. 1981B [sic], “Market Structure and the Diffusion of New Technology”, Bell Journal of Economics, Vol. 12, Autumn, 1981, Issue 2, pp. 618 – 624. |
[page 33, abstract]
This article shows that the diffusion of a capital-embodied process innovation results from a pattern of decreasing incremental benefits and adoption costs for later adoptions. Strategic behavior is inessential to this finding. We develop a method for comparing diffusion rates for different market structures in the capital equipment market. [...] Market power thus makes a difference in diffusion rates, and on which side of the market that power lies makes a considerable difference. [...] Adapting the model of Reinganum (1981a, 1981b), we first examine the factors that cause the diffusion of a capital-embodied, cost-reducing innovation. [page 34] Our results indicate that, to the contrary, strategic behavior is inessential to the result; the patterns of incremental benefits and adoption costs are the key, with or without strategic behavior.2 [...] First we establish that, for all structures compared, if the incremental benefits resulting from the kth adoption are larger under market structure A than under market structure B, then the kth adoption will occur sooner under A than under B. [...] In contrast, Reinganum (1981b) finds that greater concentration in the user industry increases the diffusion rate, the reverse of the buyer-side market power effect. The explanation for this paradox lies in distinguishing between structural concentration and collusive conduct. Reinganum analyzes increases in structural concentration in the user industry while continuing to assume noncooperative behavior. This increases the market share of each firm—and thus the profits to a given firm's adoption—but fails to internalize the negative externalities that new adoptions visit on existing investments. 2 Note that it is only Reinganum's interpretation and not her results themselves that are at issue. Reinganum, J.F. “On the Diffusion of New Technology: A Game-Theoretic Approach." Review of Economic Studies, Vol. 48 (1981a). pp. 395-405. —————, “Market Structure and the Diffusion of New Technology.” Bell Journal of Economics, Vol. 12 (1981b), pp. 618-624. |
The source is given, but no quotation marks are used. |
| [191.] Svr/Fragment 106 10 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 106, Zeilen: 10-16 |
Quelle: Götz 1999 Seite(n): 679, 680, Zeilen: 679: 22 ff.; 680: 1 f. |
|---|---|
| Underlying assumption of this diffusion matrix is that adoption costs of XML/EDI are assumed to be falling over time. Diffusion is assumed to be sequential rather than simultaneous. There are two reasons for this assumption. Potential users of a new technology may differ in a way that the expected returns from adoption are different due to firm size, market share, R&D expenditure, etc. Differences in prior believes [sic] about the ‘true’ profitability of a new technology [may result in different expected benefits from adoption and therefore in distinct adoption dates.] | Adoption costs are assumed to be falling over time. Diffusion, i.e., sequential rather than simultaneous adoption by individual firms, may result for two reasons.
(i) Rank effects: the potential users differ with respect to the (expected) returns from adoption. The reasons arc differences in firm size, R&D expenditures, market [page 680] shares (see Karshenas and Stoneman, 1993, 1995), or even the prior beliefs about the profitability of a new technology (see Jensen, 1982). JENSEN, R. "Adoption and Diffusion of an Innovation of Uncertain Profitability," Journal of Economic Theory, Vol. 27 (1982), pp. 182-193. KARSHENAS, M. AND STOREMAN, P.L. "Rank, Stock, Order, and Epidemic Effects in the Diffusion of New Process Technologies: An Empirical Model", RAND Journal of Economics, Vol. 24 (1993), pp. 503-528. ______ AND ______ "Technological Diffusion." In P. Stoneman, ed., Handbook of the Economics of Innovation and Technological Change. Cambridge, Mass.: Blackwell, 1995. |
The source is not given. Two pages earlier there is a reference to Götz (1996), however there is no entry in the reference list for such a paper. |
| [192.] Svr/Fragment 109 21 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 109, Zeilen: 21-30 |
Quelle: Shankar 1999 Seite(n): 47, 48, Zeilen: 47: left col., 22 ff.; 48: last paragraph |
|---|---|
| Momentum is clearly with XML as a portable data mechanism. The immediate benefit of XML-based e-commerce is that it will allow new and smaller businesses to participate in e-commerce. XML promises simple implementation, wide availability, and lower costs. Even enterprises using traditional batch EDI will be able to use XML data interchange to include more partners and profit from resulting efficiencies.
Though EDI has been standardized through international EDI-standards bodies, high implementation and operational costs, per-partner customization requirements, and the need for value-added network providers have halted its widespread adoption. |
[page 48]
Momentum is clearly with XML as a portable data mechanism. The immediate benefit of XML-based e-commerce is that it will allow new and smaller businesses to participate; it’s an easy sell, with its promise of simple implementation, wide availability, and lower costs. Even enterprises using traditional batch EDI should start looking at XML data interchange to include more partners and profit from resulting efficiencies. [page 47] Though EDI has been standardized through ANSI and EDIFACT (standards bodies), high implementation and operational costs, per-partner customization requirements, and the need for value-added network providers have halted its widespread adoption. |
The source is not given. |
| [193.] Svr/Fragment 109 30 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 109, Zeilen: 30 |
Quelle: Webber 1998 Seite(n): 38, Zeilen: 2 ff. |
|---|---|
| Extensible Markup Language is providing Internet [developers with new tools for implementing e-commerce and EDI Solutions.] | BACKGROUND
XML (extensible Markup Language) is providing Internet developers with new tools for implementing E-Commerce and EDI solutions. |
No source is given. |
| [194.] Svr/Fragment 110 02 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 110, Zeilen: 2-5 |
Quelle: Ritz 1995 Seite(n): 1, Zeilen: 20 ff. |
|---|---|
| Electronic Data Interchange has been used for over 30 Years and represents a particular class of inter-organizational systems that automate routine tasks in the context of trading partner communication by replacing physical mailing or transportation with electronic transportation. | Electronic data interchange (EDI) represents a particular class of interorganizational systems that automate routine tasks in the context of trading partner communication by replacing the mailing or transportation of business documents with the electronic communication of that information (Swatman and Swatman 1992).
Swatman, P.M.C. and Swatman, P.A. (1992) EDI system integration. A definition and literature survey, in: The Information Science, Vol. 8, 1992, pp. 169-205. |
No source is given. |
| [195.] Svr/Fragment 110 05 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 110, Zeilen: 5-9 |
Quelle: Murch Johnson 1999 Seite(n): 73, Zeilen: 30 ff. |
|---|---|
| Due to cost and complexity, small and medium sized businesses find it difficult to implement and maintain traditional ecommerce systems such as EDI. For these reasons, most small businesses today do not enjoy the operating efficiencies that an automated electronic information routing system proposes. But that is changing with the advent of XML. | Because of the cost and complexity, small and medium-sized businesses find it difficult to implement and maintain a traditional EDI system. For these reasons, most businesses do not enjoy the operating efficiencies that an automated electronic information routing system proposes. (See the accompanying figure "EDI Today.") The obstacles that businesses must overcome to start their EDI/EC implementation seem insurmountable, but that situation is changing with the advent of XML/EDI. |
No source is given. |
| [196.] Svr/Fragment 110 10 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 110, Zeilen: 10-14 |
Quelle: Carroll 2000 Seite(n): online, Zeilen: 0 |
|---|---|
| The main challenge in using XML is not with document structure and syntax, but with semantics. Each application domain needs to have both specific document structure and agreed-upon semantics to make effective use of XML-defined documents. Various vertical industry segments have to agree on the meaning of their domain-specific XML/EDI tags. | The main challenge in using XML is not with document structure and syntax, but with semantics. [...] Each application domain needs to have both specific document structure and agreed-upon semantics to make effective use of XML-defined documents. Various vertical industry segments have to agree on the meaning of their domain-specific XML tags. |
No source is given. Page 110 is part of the "Conclusion" section. See also p. 64. |
| [197.] Svr/Fragment 110 27 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 110, Zeilen: 27-32 |
Quelle: Bakos 1991 Seite(n): online, Zeilen: 0 |
|---|---|
| Thus, potential participants in electronic markets based on XML/EDI standards face substantial uncertainties regarding the actual benefits of implementing such a system. This uncertainty can affect the strategic behavior of buyers, sellers and potential intermediaries, by inducing them to adopt a wait-and-see strategy where they delay introducing or joining a system in the hope that they will learn from the experience of other organizations. | 5. Potential participants in electronic markets face substantial uncertainty regarding the actual benefits of joining such a system. [...]
This uncertainty can affect the strategic behavior of buyers, sellers, and potential intermediaries, by inducing them to adopt a “wait and see” strategy where they delay introducing or joining a system in the hope that they will learn from the experiences of other organizations. |
No source is given. Page 110 is part of the "Conclusion" section. |
| [198.] Svr/Fragment 111 09 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 111, Zeilen: 9-14 |
Quelle: Benaroch Kauffman 2000 Seite(n): 209, Zeilen: right col., 30 ff. |
|---|---|
| I supposed that every company today facing the XML/EDI investment decision is the holder of an American deferral option on a dividend-paying asset. The asset underlying this option is the potential stream of revenues from an investment opportunity that will materialize only when a company decides to invest in an XML/EDI project at any given future date, where the dividends are the revenues lost during deferral time. | Yankee possessed an American deferral option on a dividend paying asset. The asset underlying this option is the potential stream of revenues from an investment opportunity that will materialize only once Yankee enters the POS debit market any time starting in 1987, where the dividends are the revenues lost during the time Yankee deferred entry into this market. |
No source is given. Final page of the "Conclusion"-section. See also p. 89. |
| [199.] Svr/Fragment 123 20 |
| Verschleierung |
|---|
| Untersuchte Arbeit: Seite: 123, Zeilen: 20-26 |
Quelle: Walsh 1998 Seite(n): online, Zeilen: 0 |
|---|---|
| A large percentage of XML specifications deal with various sorts of declarations that are allowed in XML. One of the greatest strengths of XML is that it allows the user to create own tag names. But for any given application, it is probably not meaningful for tags to occur in a completely arbitrary order. If the document is to have meaning, there must be some constraint on the sequence and nesting of tags. Declarations are where these constraints can be expressed. | A large percentage of the XML specification deals with various sorts of declarations that are allowed in XML. […]
One of the greatest strengths of XML is that it allows you to create your own tag names. But for any given application, it is probably not meaningful for tags to occur in a completely arbitrary order. […] […] […] So, if the document is to have meaning, and certainly if you're writing a stylesheet to present it, there must be some constraint on the sequence and nesting of tags. Declarations are where these constraints can be expressed. |
The source is not mentioned. |
| [200.] Svr/Fragment 124 01 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 124, Zeilen: 1-6 |
Quelle: Walsh 1998 Seite(n): online, Zeilen: 0 |
|---|---|
| More generally, declarations allow a document to communicate meta-information to the parser about its content. Meta-information includes the allowed sequence and nesting of tags, attribute values and their types and defaults, the names of external files that may be referenced and whether or not they contain XML, the formats of some external (non-XML) data that may be included, and entities that may be encountered. | More generally, declarations allow a document to communicate meta-information to the parser about its content. Meta-information includes the allowed sequence and nesting of tags, attribute values and their types and defaults, the names of external files that may be referenced and whether or not they contain XML, the formats of some external (non-XML) data that may be included, and entities that may be encountered. |
The source is not mentioned. |
| [201.] Svr/Fragment 128 27 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 128, Zeilen: 27-31 |
Quelle: Walsh 1998 Seite(n): online, Zeilen: 0 |
|---|---|
| Two other content models are possible: EMPTY indicates that the element has no content (and consequently no end-tag), and ANY indicates that any content is allowed. The ANY content model is sometimes useful during document conversion, but should be avoided at almost any cost in a production environment because it disables all content checking in that element. | Two other content models are possible: EMPTY indicates that the element has no content (and consequently no end-tag), and ANY indicates that any content is allowed. The ANY content model is sometimes useful during document conversion, but should be avoided at almost any cost in a production environment because it disables all content checking in that element. |
The source is not given. |
| [202.] Svr/Fragment 130 24 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 130, Zeilen: 24-26 |
Quelle: Walsh 1998 Seite(n): online, Zeilen: 0 |
|---|---|
| Attribute declarations identify which elements may have attributes, what types of attributes they may have, what values the attributes may hold, and what default value each attribute has. | Attribute declarations [Section 3.3] identify which elements may have attributes, what attributes they may have, what values the attributes may hold, and what default value each attribute has. |
The source is not given. |
| [203.] Svr/Fragment 131 14 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 131, Zeilen: 14-20, 26-29 |
Quelle: Walsh 1998 Seite(n): online, Zeilen: 0 |
|---|---|
An attribute declaration may specify that an attribute has a fixed value. In this case, the attribute is not required, but if it occurs, it must have the specified value. One use for fixed attributes is to associate semantics with an element.
The attribute value is not required, and no default value is provided. If a value is not specified, the XML processor must proceed without one. [...]
An attribute can be given any legal value as a default. The attribute value is not required on each element in the document, but if it is not present, it will appear to be the specified default. |
#IMPLIED
The attribute value is not required, and no default value is provided. If a value is not specified, the XML processor must proceed without one. […] An attribute declaration may specify that an attribute has a fixed value. In this case, the attribute is not required, but if it occurs, it must have the specified value. One use for fixed attributes is to associate semantics with an element. "value" An attribute can be given any legal value as a default. The attribute value is not required on each element in the document, but if it is not present, it will appear to be the specified default. |
The source is not given. |
| [204.] Svr/Fragment 132 16 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 132, Zeilen: 16-18 |
Quelle: Walsh 1998 Seite(n): online, Zeilen: 0 |
|---|---|
| CDATA attributes are strings where any text is allowed. Don't confuse CDATA attributes with CDATA sections. In CDATA attributes, markup is recognized. | CDATA attributes are strings, any text is allowed. Don't confuse CDATA attributes with CDATA sections. In CDATA attributes, markup is recognized; specifically, entity references are expanded. |
The source is not given. |
| [205.] Svr/Fragment 133 05 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 133, Zeilen: 5-7 |
Quelle: Walsh 1998 Seite(n): online, Zeilen: 0 |
|---|---|
| All ID values used in a document must be different. IDs uniquely identify individual elements in a document. Elements can have only one single ID attribute | All of the ID values used in a document must be different. IDs uniquely identify individual elements in a document. Elements can have only a single ID attribute. |
The source is not given. |
| [206.] Svr/Fragment 136 25 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 136, Zeilen: 25-27 |
Quelle: Walsh 1998 Seite(n): online, Zeilen: 0 |
|---|---|
| Internal entities allow you to define shortcuts for frequently typed text or text that is expected to change, such as the revision status of a document. | Internal entities allow you to define shortcuts for frequently typed text or text that is expected to change, such as the revision status of a document. |
The source is not given. |
| [207.] Svr/Fragment 137 04 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 137, Zeilen: 4-5, 10-15, 24-28 |
Quelle: Walsh 1998 Seite(n): online, Zeilen: 0 |
|---|---|
| Internal entities can include references to other internal entities, but it is an error for them to be recursive.
[...] External entities allow an XML document to refer to an external file. External entities contain either text or binary data. If they contain text, the content of the external file is inserted at the point of reference and parsed as part of the referring document. Binary data is not parsed and may only be referenced in an attribute. Binary data is used to reference figures and other non-XML content in the document. [...] In this case, the XML processor will parse the content of that file as if its content had been typed at the location of the entity reference. The entity is also an external entity, but its content is binary. The LOGO entity can only be used as the value of an ENTITY (or ENTITIES) attribute (on a graphic element, perhaps). The XML processor will pass this information along to an [application, but it does not attempt to process the content of /standard/logo.gif.] |
Internal entities can include references to other internal entities, but it is an error for them to be recursive.
[...] External entities allow an XML document to refer to an external file. External entities contain either text or binary data. If they contain text, the content of the external file is inserted at the point of reference and parsed as part of the referring document. Binary data is not parsed and may only be referenced in an attribute. Binary data is used to reference figures and other non-XML content in the document. [...] The XML processor will parse the content of that file as if its content had been typed at the location of the entity reference. The entity ATIlogo is also an external entity, but its content is binary. The ATIlogo entity can only be used as the value of an ENTITY (or ENTITIES) attribute (on a graphic element, perhaps). The XML processor will pass this information along to an application, but it does not attempt to process the content of /standard/logo.gif. |
The source is not given. |
| [208.] Svr/Fragment 139 24 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 139, Zeilen: 24-27 |
Quelle: Walsh 1998 Seite(n): online, Zeilen: 0 |
|---|---|
| Between the start of the section, <![CDATA[ and the end of the section, ]]>, all character data is passed directly to the application. The only string that cannot occur in a CDATA section is ]]>. Comments are not recognized in a CDATA section. If present, the literal text <!--comment--> will be passed directly to the [application.] | Between the start of the section, “<![CDATA[” and the end of the section, “]]>”, all character data is passed directly to the application.
The only string that cannot occur in a CDATA section is “]]>”. Note: comments are not recognized in a CDATA section. If present, the literal text “<!--comment-->” will be passed directly to the application. |
The source is not given. |
| [209.] Svr/Fragment 140 20 |
| KomplettPlagiat |
|---|
| Untersuchte Arbeit: Seite: 140, Zeilen: 20-21 |
Quelle: Walsh 1998 Seite(n): online, Zeilen: 0 |
|---|---|
| The rule for XML processors is that in the absence of a declaration that identifies the content model of an element, all white space is significant. | The rule for XML processors is that in the absence of a declaration that identifies the content model of an element, all white space is significant. |
The source is not given. |
Quellen[]
| [1.] Quelle:Svr/Berners-Lee et al 2001 |
| Autor | Tim Berners-Lee / James Hendler / Ora Lassila |
| Titel | The Semantic Web. A new form of Web content that is meaningful to computers will unleash a revolution of new possibilities |
| Zeitschrift | Scientific American |
| Datum | 17. May 2001 |
| Seiten | 34-43 |
| URL | https://www.jstor.org/stable/26059207 |
Literaturverz. |
yes |
| Fußnoten | yes |
| [2.] Quelle:Svr/Carroll 2000 |
| Autor | Michael Carroll |
| Titel | Beneath the Vortals - The Lowdown on XML-Based B2B Standards |
| Datum | February 2000 |
| URL | https://people.apache.org/~jim/NewArchitect/webtech/2000/02/carroll/index.html |
Literaturverz. |
no |
| Fußnoten | no |
| [3.] Quelle:Svr/Walsh 1998 |
| Autor | Norman Walsh |
| Titel | A Technical Introduction to XML |
| Datum | 18. February 1998 |
| URL | https://web.archive.org/web/20000817031942/http://nwalsh.com/docs/articles/xml/ |
Literaturverz. |
no |
| Fußnoten | no |
| [4.] Quelle:Svr/Coy 1999 |
| Autor | Peter Coy |
| Titel | Exploiting Uncertainty - The "real-options" revolution in decision-making |
| Zeitschrift | Business Week |
| Datum | 7. June 1999 |
| URL | https://www.bloomberg.com/news/articles/1999-06-06/exploiting-uncertainty, https://www.simon.rochester.edu/fac/raith/Smith-Teaching/Fin%20413/Article%20Handouts%20in%20class/1-Expoiting%20Uncertainty%20-%20BusinessWeek%201999.pdf |
Literaturverz. |
no |
| Fußnoten | no |
| [5.] Quelle:Svr/Kobielus 2000 |
| Autor | James Kobielus |
| Titel | EDI and Workflow Converge in E-Business Tools |
| Zeitschrift | Network World |
| Datum | 7. February 2000 |
| Jahrgang | Volume 17 |
| Nummer | 6 |
| Seiten | 57 |
| URL | https://books.google.de/books?id=EhcEAAAAMBAJ&pg=PA57&lpg=PA57#v=onepage&q&f=false |
Literaturverz. |
no |
| Fußnoten | no |
| [6.] Quelle:Svr/Bailey Bakos 1997 |
| Autor | Joseph P. Bailey / Yannis Bakos |
| Titel | An Exploratory Study of the Emerging Role of Electronic Intermediaries. |
| Zeitschrift | International Journal of Electronic Commerce |
| Jahr | 1997 |
| DOI | https://doi.org/10.1080/10864415.1997.11518287. |
Literaturverz. |
no |
| Fußnoten | no |
| [7.] Quelle:Svr/Bakos 1997 |
| Autor | J. Yannis Bakos |
| Titel | Reducing Buyer Search Costs: Implications for Electronic Marketplaces |
| Zeitschrift | Management Science |
| Herausgeber | The Institute of Management Sciences |
| Ausgabe | 43 |
| Datum | December 1997 |
| Nummer | 12 |
| URL | http://people.stern.nyu.edu/bakos/emkts.pdf |
Literaturverz. |
yes |
| Fußnoten | yes |
| [8.] Quelle:Svr/Shankar 1999 |
| Autor | Gess Shankar |
| Titel | The XML Standards landscape |
| Zeitschrift | Infoworld |
| Datum | 19. July 1999 |
| Jahrgang | Vol. 21 |
| Nummer | Issue 29 |
| Seiten | 47-48 |
| URL | https://books.google.de/books?id=OFAEAAAAMBAJ&lpg=PA47&hl=de&pg=PA47#v=onepage&q&f=false |
Literaturverz. |
no |
| Fußnoten | no |
| [9.] Quelle:Svr/Luehrman 1998 |
| Autor | Timothy A. Luehrman |
| Titel | Investment Opportunities as Real Options: Getting Started on the Numbers |
| Zeitschrift | Harvard Business Review |
| Datum | July / August 1998 |
| URL | https://hbr.org/1998/07/investment-opportunities-as-real-options-getting-started-on-the-numbers |
Literaturverz. |
yes |
| Fußnoten | yes |
| [10.] Quelle:Svr/Weitzel et al 1999 |
| Autor | Tim Weitzel / Peter Buxmann / Ralf Kronenberg / Frank Ladner |
| Titel | XML/EDI - the (r)evolution of EDI - |
| Ort | Frankfurt am Main |
| Jahr | 1999 |
| URL | https://web.archive.org/web/20110111105322/http://www.wiwi.uni-frankfurt.de/~tweitzel/XMLEDI.doc |
Literaturverz. |
yes |
| Fußnoten | yes |
| [11.] Quelle:Svr/Economist 1999 |
| Titel | Keeping all options open |
| Zeitschrift | The Economist |
| Datum | 12. August 1999 |
| URL | https://www.economist.com/finance-and-economics/1999/08/12/keeping-all-options-open |
Literaturverz. |
no |
| Fußnoten | no |
| [12.] Quelle:Svr/Pindyck 1989 |
| Autor | Robert Pindyck |
| Titel | Irreversibility, Uncertainty and Investment |
| Sammlung | Working Papers |
| Herausgeber | The World Bank |
| Datum | October 1989 |
| Anmerkung | In the dissertation a different version of the source is cited. |
| URL | Google Books |
Literaturverz. |
yes |
| Fußnoten | yes |
| [13.] Quelle:Svr/Taudes et al 1999 |
| Autor | Alfred Taudes / Markus Feurstein / Andreas Mild |
| Titel | How option thinking can improve software platform decisions |
| Sammlung | "Adaptive Information Systems and Modelling in Economics and Management Science", Working Paper No. 38 |
| Datum | May 1999 |
| URL | https://epub.wu.ac.at/1134/1/document.pdf |
Literaturverz. |
yes |
| Fußnoten | yes |
| [14.] Quelle:Svr/Bass 1969 |
| Autor | Frank M. Bass |
| Titel | A New Product Growth for Model Consumer Durables |
| Zeitschrift | Management Science |
| Datum | January 1969 |
| Jahrgang | Vol. 15 |
| Nummer | No. 5 |
| Seiten | 215-227 |
| URL | https://www.jstor.org/stable/2628128 - https://math.la.asu.edu/~dieter/courses/APM_598/Bass_69.pdf |
Literaturverz. |
yes |
| Fußnoten | yes |
| [15.] Quelle:Svr/Wong 1998 |
| Autor | W. Wong |
| Titel | XML to "revolutionize" info exchange |
| Sammlung | CNet news |
| Datum | 31. December 1998 |
| Anmerkung | The link leads to an article now dating January 2, 2002. According to https://www.cnet.com/sitemaps/articles/1998/ the article was first published December 31, 1998. |
| URL | https://www.cnet.com/news/xml-to-revolutionize-info-exchange/ |
Literaturverz. |
yes |
| Fußnoten | yes (as Cnet News 1998) |
| [16.] Quelle:Svr/Dumbill 2001 |
| Autor | Edd Dumbill |
| Titel | XML Hype Down But Not Out In New York |
| Datum | 11. April 2001 |
| URL | https://www.xml.com/pub/a/2001/04/11/xmldevcon.html |
Literaturverz. |
yes |
| Fußnoten | yes |
| [17.] Quelle:Svr/Raman 1998 |
| Autor | Dick Raman |
| Titel | AD HOC WORKING GROUP ON SIMPL-EDI AND FORMS AND WEB BASED EDI (SIMAC) - Proposal for a UN Repository for XML/EDI |
| Datum | 5. June 1998 |
| URL | http://www.unece.org/trade/untdid/download/si98004.rtf |
Literaturverz. |
no |
| Fußnoten | no |
| [18.] Quelle:Svr/Bakos 1991 |
| Autor | J. Yannis Bakos |
| Titel | A Strategic Analysis of Electronic Marketplaces |
| Zeitschrift | MIS Quarterly |
| Jahr | 1991 |
| Seiten | pp. 295-310 |
| URL | http://people.stern.nyu.edu/bakos/stratemkts.pdf |
Literaturverz. |
yes |
| Fußnoten | yes |
| [19.] Quelle:Svr/Bakos 1998 |
| Autor | Yannis Bakos |
| Titel | The Emerging Role of Electronic Marketplaces on the Internet |
| Zeitschrift | Communications of the ACM |
| Jahr | 1998 |
| Seiten | 35-46 |
| URL | https://archive.nyu.edu/handle/2451/27839 |
Literaturverz. |
yes |
| Fußnoten | yes |
| [20.] Quelle:Svr/Spider's Apprentice 2000 |
| Titel | The Spider's Apprentice. A Helpful Guide to Web Search Engines. How to get the most from search engines like AltaVista, Infoseek, Excite, Webcrawler, Lycos, HotBot, and the Yahoo Directory.
Page 4 - How Search Engines Work |
| Datum | 18. October 2000 |
| URL | https://web.archive.org/web/20001018071847/https://www.monash.com/spidap4.html |
Literaturverz. |
no |
| Fußnoten | no |
| [21.] Quelle:Svr/Lee 1998 |
| Autor | Ronald M. Lee |
| Titel | Towards open electronic contracting |
| Zeitschrift | Electronic Markets |
| Jahr | 1998 |
| Seiten | 3-8 |
| URL | https://www.researchgate.net/publication/220505447_Towards_Open_Electronic_Contracting |
Literaturverz. |
yes |
| Fußnoten | yes |
| [22.] Quelle:Svr/Lucas 1999 |
| Autor | Henry C. Lucas |
| Titel | Information technology and the productivity paradox: Assessing the value of investing in IT |
| Verlag | Oxford University Press |
| Jahr | 1999 |
Literaturverz. |
yes |
| Fußnoten | yes |
| [23.] Quelle:Svr/Peat Webber 1997 |
| Autor | Bruce Peat / David Webber |
| Titel | XML/EDI: The E-business Framework |
| Datum | August 1997 |
| URL | https://www.xmledi-group.org/start.html |
Literaturverz. |
yes |
| Fußnoten | yes |
| [24.] Quelle:Svr/W3C 1999 |
| Autor | World Wide Web Consortium 14-January-1999 |
| Titel | Namespaces in XML |
| Datum | 14. January 1999 |
| URL | https://www.w3.org/TR/1999/REC-xml-names-19990114/ |
Literaturverz. |
yes |
| Fußnoten | yes |
| [25.] Quelle:Svr/Erdmann Studer 1999 |
| Autor | Michael Erdmann / Rudi Studer |
| Titel | Ontologies as Conceptual Models for XML Documents |
| Datum | October 1999 |
| URL | https://www.aifb.kit.edu/web/Inproceedings537 |
Literaturverz. |
yes |
| Fußnoten | no |
| [26.] Quelle:Svr/Fisher Pry 1971 |
| Autor | J. C. Fisher / R. H. Pry |
| Titel | A Simple Substitution Model of Technological Change |
| Zeitschrift | Technological Forecasting and Social Change |
| Jahr | 1971 |
| Seiten | 75-88 |
| URL | http://newmaeweb.ucsd.edu/courses/MAE119/WI_2018/ewExternalFiles/Simple%20Substitution%20Model%20of%20Technological%20Change%20-%20Fischer%20Pry%201971.pdf |
Literaturverz. |
yes |
| Fußnoten | yes |
| [27.] Quelle:Svr/Trigeorgis 1993 |
| Autor | Lenos Trigeorgis |
| Titel | Real Options and Interactions with Financial Flexibility |
| Zeitschrift | Financial Management |
| Jahr | 1993 |
| Jahrgang | Vol. 22 |
| Nummer | No. 3 |
| Seiten | 202-224 |
| URL | https://www.jstor.org/stable/3665939 |
Literaturverz. |
yes |
| Fußnoten | yes |
| [28.] Quelle:Svr/Reinganum 1981 |
| Autor | Jennifer F. Reinganum |
| Titel | On the Diffusion of New Technology: A game Theoretic approach |
| Zeitschrift | Review of Economic Studies |
| Jahr | 1981 |
| Seiten | 395-408 |
| URL | http://blog.rchss.sinica.edu.tw/FCLai/wp-content/uploads/2016/11/20160822_Sun_Reinganum-1981_On-the-Diffusion-of-New-Technology-A-Game-Theoretic-Approch_Review-of-Economic-Studies-408-395-405.pdf |
Literaturverz. |
yes |
| Fußnoten | yes |
| [29.] Quelle:Svr/Benaroch Kauffman 2000 |
| Autor | Michel Benaroch / Robert J. Kauffman |
| Titel | Justifying Electronic Banking Network Expansion Using REal Options Analysis |
| Zeitschrift | MIS Quarterly |
| Jahr | 2000 |
| Seiten | 197-225 |
| URL | https://www.jstor.org/stable/3250936?seq=1, http://faculty.ndhu.edu.tw/~sywang/P6.pdf |
Literaturverz. |
no |
| Fußnoten | no |
| [30.] Quelle:Svr/Dixit Pindyck 1994 |
| Autor | Avinash K. Dixit / Robert S. Pindyck |
| Titel | Investment under Uncertainty |
| Ort | Princeton, New Jersey |
| Verlag | Princeton University Press |
| Jahr | 1994 |
Literaturverz. |
yes |
| Fußnoten | yes |
| [31.] Quelle:Svr/Pitts-Moultis Kirk 1999 |
| Autor | Natanya Pitts-Moultis / Cheryl Kirk |
| Titel | XML Black Book |
| Ort | Boston |
| Jahr | 1999 |
Literaturverz. |
yes |
| Fußnoten | yes |
| [32.] Quelle:Svr/O'Callaghan Turner 1995 |
| Autor | Ramon O'Callaghan / Jon Turner |
| Titel | Electronic Data Interchange Concepts and Issues |
| Sammlung | EDI in Europe: How It Works in Practice |
| Herausgeber | Helmut Krcmar / Niels Bjørn-Andersen / Ramón O'Callaghan |
| Verlag | Wiley |
| Jahr | 1995 |
| Seiten | 1-20 |
| URL | https://papers.ssrn.com/sol3/papers.cfm?abstract_id=1284839 |
Literaturverz. |
yes |
| Fußnoten | yes |
| [33.] Quelle:Svr/Kotok 1999 |
| Autor | Alan Kotok |
| Titel | XML and EDI Lessons Learned and Baggage to Leave Behind |
| Datum | 4. August 1999 |
| URL | https://www.xml.com/pub/a/1999/08/edi/index.html |
Literaturverz. |
no |
| Fußnoten | no |
| [34.] Quelle:Svr/Kotok 2000 |
| Autor | Alan Kotok |
| Titel | Even More Extensible |
| Datum | 2. August 2000 |
| URL | https://www.xml.com/pub/a/ws/2000/08/02/ebiz/extensible.html |
Literaturverz. |
yes |
| Fußnoten | yes |
| [35.] Quelle:Svr/Kotok 2000a |
| Autor | Alan Kotok |
| Titel | A Survey of XML Business Data Exchange Vocabularies |
| Datum | 23. February 2000 |
| URL | https://www.xml.com/pub/a/2000/02/23/ebiz/index.html |
Literaturverz. |
no |
| Fußnoten | no |
| [36.] Quelle:Svr/Funke 1998 |
| Autor | Susan Funke |
| Titel | XML Content Finally Arrives on the Web! |
| Zeitschrift | Searcher |
| Datum | October 1998 |
| Seiten | 63 ff. |
| URL | https://www.researchgate.net/publication/234658571_XML_Content_Finally_Arrives_on_the_Web |
Literaturverz. |
no |
| Fußnoten | no |
| [37.] Quelle:Svr/Lee 1998a |
| Autor | Ook Lee |
| Titel | Negotiation and Contract through E-Mail |
| Zeitschrift | Electronic Markets |
| Jahr | 1998 |
| Seiten | 17-20 |
Literaturverz. |
yes |
| Fußnoten | yes |
| [38.] Quelle:Svr/Ritz 1995 |
| Autor | Daniel Ritz |
| Titel | The start-up of an EDI network - A comparative case study in the air cargo industry |
| Jahr | 1995 |
| Anmerkung | Dissertation der Hochschule St. Gallen; Dissertation Nr. 1675 |
Literaturverz. |
yes |
| Fußnoten | yes |
| [39.] Quelle:Svr/Mansfield 1961 |
| Autor | Edwin Mansfield |
| Titel | Technical Change and the Rate of Imitation |
| Zeitschrift | Econometrica |
| Datum | October 1961 |
| Jahrgang | Vol. 29 |
| Nummer | 4 |
| Seiten | 741-765 |
| URL | https://www.jstor.org/stable/1911817 |
Literaturverz. |
yes |
| Fußnoten | yes |
| [40.] Quelle:Svr/Quirmbach 1986 |
| Autor | Herman C. Quirmbach |
| Titel | The diffusion of new technology and the market for an innovation |
| Zeitschrift | Rand Journal of Economics |
| Datum | Spring 1986 |
| Jahrgang | Vol. 17 |
| Nummer | 1 |
| Seiten | 33-47 |
| URL | https://www.jstor.org/stable/2555626 |
Literaturverz. |
yes |
| Fußnoten | yes |
| [41.] Quelle:Svr/Strassmann 1985 |
| Autor | Paul A. Strassmann |
| Titel | Information Payoff - Transformation of Work in the electronic age |
| Jahr | 1985 |
Literaturverz. |
yes |
| Fußnoten | yes |
| [42.] Quelle:Svr/Copeland Weston 1992 |
| Autor | Thomas E. Copeland / Thomas E. Weston |
| Titel | Financial Theory and Corporate Policy |
| Ort | Reading |
| Verlag | Addison Wesley |
| Ausgabe | 3rd edition, reprinted with corrections, May 1992 |
| Jahr | 1992 |
Literaturverz. |
yes |
| Fußnoten | yes |
| [43.] Quelle:Svr/Webber 1998 |
| Autor | David R.R. Webber |
| Titel | Introducing XML/EDI Frameworks |
| Zeitschrift | Electronic Markets |
| Jahr | 1998 |
| Jahrgang | Vol. 8 |
| Nummer | 1 |
| Seiten | 38-41 |
| URL | http://www.electronicmarkets.org/archive/issues/volume-8/volume-8-issue-1/ - http://www.electronicmarkets.org/fileadmin/user_upload/doc/Issues/Volume_08/Issue_01/V08I1_Introducing_XML-EDI_Frameworks.pdf |
Literaturverz. |
yes |
| Fußnoten | yes |
| [44.] Quelle:Svr/Weitzel et al 2000 |
| Autor | Tim Weitzel / Peter Buxmann / Falk v. Westarp |
| Titel | A Communication Architecture for the Digital Economy 21st century EDI |
| Sammlung | Proceedings of the 33rd Annual Hawaii International Conference on System Sciences |
| Jahr | 2000 |
| URL | https://ieeexplore.ieee.org/document/926841 - https://ieeexplore.ieee.org/xpl/conhome/6709/proceeding |
Literaturverz. |
yes (Weitzel, T. & Buxmann, P. 1999, A communication architecture for the digital economy: 21st century EDI) |
| Fußnoten | yes |
| [45.] Quelle:Svr/Zimmermann 1998 |
| Autor | Hans-Dieter Zimmermann |
| Titel | Business Media: A New Approach to Overcome Current Problems of Electronic Commerce |
| Sammlung | AMCIS 1998 Proceedings |
| Jahr | 1998 |
| URL | https://aisel.aisnet.org/cgi/viewcontent.cgi?article=1555&context=amcis1998 |
Literaturverz. |
yes |
| Fußnoten | yes |
| [46.] Quelle:Svr/Schmid 1993 |
| Autor | Beat F. Schmid |
| Titel | Electronic Markets |
| Zeitschrift | Electronic Markets |
| Datum | October 1993 |
| Jahrgang | Vol. 3 |
| Nummer | 9-10 |
| Seiten | 3-4 |
| URL | http://www.electronicmarkets.org/archive/issues/volume-3/volume-3-issue-3/ - http://www.electronicmarkets.org/fileadmin/user_upload/doc/Issues/Volume_03/Issue_03/Electronic_Markets.pdf |
Literaturverz. |
yes (as Schmidt) |
| Fußnoten | yes (as Schmidt) |
| [47.] Quelle:Svr/Houser et al 1996 |
| Autor | W. Houser / J. Friffin / C. Hage |
| Titel | EDI Meets the Internet - Frequently Asked Questions about Electronic Data Interchange (EDI) on the Internet |
| Jahr | 1996 |
| URL | https://getrfc.com/rfc1865 |
Literaturverz. |
no |
| Fußnoten | no |
| [48.] Quelle:Svr/Johnson 1999 |
| Autor | Amy Helen Johnson |
| Titel | XML is Xtending its reach |
| Zeitschrift | Computerworld |
| Datum | 18. October 1999 |
| Jahrgang | Vol. 33 |
| Nummer | 42 |
| Seiten | 76-81 |
| URL | http://faculty.bus.olemiss.edu/breithel/final%20backup%20of%20bus620%20summer%202000%20from%20mba%20server/frankie_gulledge/xml/xml_xtends_its_reach.htm - https://books.google.de/books?id=EE9uNPV85VgC&lpg=PA81&hl=de&pg=PA76 |
Literaturverz. |
no |
| Fußnoten | no |
| [49.] Quelle:Svr/Sanborn Lattig 2000 |
| Autor | Stephanie Sanborn / Michael Lattig |
| Titel | Internet standards. HTML-XML combo finalized |
| Zeitschrift | InfoWorld |
| Datum | 31. January 2000 |
| Jahrgang | Vol. 22 |
| Nummer | 5 |
| Seiten | 16 |
| URL | http://faculty.bus.olemiss.edu/breithel/final%20backup%20of%20bus620%20summer%202000%20from%20mba%20server/frankie_gulledge/xml/html_xml_combo_finalized.htm - https://books.google.de/books?id=dzkEAAAAMBAJ&pg=PA16&lpg=PA16&dq |
Literaturverz. |
no |
| Fußnoten | no |
| [50.] Quelle:Svr/Murch Johnson 1999 |
| Autor | Richard Murch / Tony Johnson |
| Titel | Intelligent Software Agents |
| Jahr | 1999 |
Literaturverz. |
no |
| Fußnoten | no |
| [51.] Quelle:Svr/Edwards 1999 |
| Autor | Morris Edwards |
| Titel | An EDI whose time has come |
| Zeitschrift | Communications News |
| Datum | September 1999 |
| Seiten | 104 |
| URL | https://www.thefreelibrary.com/An+EDI+whose+time+has+come.-a057769332 |
Literaturverz. |
yes |
| Fußnoten | yes |
| [52.] Quelle:Svr/Bryan 1998 |
| Autor | Martin Bryan |
| Titel | European XML/EDI Pilot Project - Terms of Reference |
| Jahr | 1998 |
| URL | http://xml.coverpages.org/ec-xmlediTR.html |
Literaturverz. |
yes |
| Fußnoten | yes |
| [53.] Quelle:Svr/XML EDI Group 2001 |
| Autor | The XML/EDI Group |
| Titel | The Future of Electronic Business |
| Datum | January 2001 |
| URL | https://www.xmledi-group.org/executive.html |
Literaturverz. |
yes |
| Fußnoten | yes |
| [54.] Quelle:Svr/Walsh Nelson 1998 |
| Autor | Jeff Walsh / Matthew Nelson |
| Titel | Business to get XML repository |
| Zeitschrift | InfoWorld |
| Datum | 3. August 1998 |
| Jahrgang | 20 |
| Nummer | 31 |
| Seiten | 5 |
| URL | http://xml.coverpages.org/walshBusiness9808.html - https://books.google.de/books?id=jlIEAAAAMBAJ&pg=PA5 |
Literaturverz. |
no |
| Fußnoten | no |
| [55.] Quelle:Svr/Parfett 1992 |
| Autor | Martin Parfett |
| Titel | What is EDI? A Guide to Electronic Data Interchange |
| Ausgabe | 2nd edition |
| Jahr | 1992 |
Literaturverz. |
yes |
| Fußnoten | yes |
| [56.] Quelle:Svr/Sassone Schwartz 1986 |
| Autor | Peter G. Sassone / A. Perry Schwartz |
| Titel | Cost-Justifying OA: A straightforward method for quantifying the benefits of automated office systems |
| Zeitschrift | Datamation |
| Datum | 15. February 1986 |
| Jahrgang | 32 |
| Nummer | 4 |
| Seiten | 83-88 |
Literaturverz. |
yes |
| Fußnoten | yes |
| [57.] Quelle:Svr/Emmelhainz 1990 |
| Autor | Margaret A. Emmelhainz |
| Titel | Electronic Data Interchange: A Total Management Guide |
| Ort | New York |
| Verlag | Van Nostrand Reinhold |
| Jahr | 1990 |
Literaturverz. |
yes |
| Fußnoten | yes |
| [58.] Quelle:Svr/Schwartz 2001 |
| Autor | Richard Schwartz |
| Titel | Web Site Construction Tips & Tricks |
| Verlag | OnWord Press (imprint of Thomson Learning) |
| Jahr | 2001 |
Literaturverz. |
no |
| Fußnoten | no |
| [59.] Quelle:Svr/Brealey Myers 1981 |
| Autor | Richard Brealey / Stewart Myers |
| Titel | Principles of Corporate Finance |
| Ort | New York et al. |
| Verlag | McGraw-Hill |
| Jahr | 1981 |
| Reihe | McGraw-Hill series in finance |
Literaturverz. |
yes |
| Fußnoten | yes |
| [60.] Quelle:Svr/ECOOP 2001 |
| Titel | Mechanisms for Enterprise Integration: From Objects to Ontologies. 15th European Conference on Object-Oriented Programming, June 18-22, 2001 |
| Herausgeber | University Eötvös Loránd, Budapest, Hungary; Department of General Computer Science |
| Datum | 4. March 2001 |
| URL | https://web.archive.org/web/20010304162956/http://ecoop2001.inf.elte.hu/workshop/O2O-ws.html |
Literaturverz. |
no |
| Fußnoten | no |
| [61.] Quelle:Svr/Schuyler 1992 |
| Autor | John R. Schuyler |
| Titel | Credible Projections Now Require Decision Analysis |
| Zeitschrift | Cost Engineering |
| Datum | March 1992 |
| Jahrgang | 34 |
| Nummer | 3 |
| Seiten | 15-19 |
Literaturverz. |
no |
| Fußnoten | no |
| [62.] Quelle:Svr/Götz 1999 |
| Autor | Georg Götz |
| Titel | Monopolistic competition and the diffusion of new technology |
| Zeitschrift | The RAND Journal of Economics |
| Datum | Winter 1999 |
| Jahrgang | Vol. 30 |
| Nummer | 4 |
| Seiten | 679-693 |
| Anmerkung | p. 679, footnote: "Earlier versions of this article were presented at the 1996 Econometric Society European Meeting in Istanbul, at the 1996 FAKIR conference in Vienna, and at the 1996 N1RTROR conference in Maastricht." |
| URL | https://www.jstor.org/stable/2556070 |
Literaturverz. |
no |
| Fußnoten | yes |
| [63.] Quelle:Svr/Rogers 1983 |
| Autor | Everett M. Rogers |
| Titel | Diffusion of Innovations |
| Ort | New York / London |
| Verlag | The Free Press |
| Ausgabe | 3rd edition |
| Jahr | 1983 |
Literaturverz. |
yes |
| Fußnoten | yes |
| [64.] Quelle:Svr/Jaakkola 1996 |
| Autor | Hannu Jaakkola |
| Titel | Comparison and Analysis of Diffusion Models |
| Sammlung | Diffusion and Adoption of Information Technology. Proceedings of the first IFIP WG 8.6 working conference on the diffusion and adoption of information technology, Oslo, Norway, October 1995 |
| Herausgeber | Karlheinz Kautz / Jan-Pries Heye |
| Ort | Boston |
| Verlag | Springer |
| Jahr | 1996 |
| Seiten | 65-83 |
| URL | https://link.springer.com/content/pdf/10.1007/978-0-387-34982-4_6.pdf |
Literaturverz. |
no |
| Fußnoten | no |
| [65.] Quelle:Svr/James 1990 |
| Autor | David James |
| Titel | Counting the real costs of new technology |
| Zeitschrift | Financial Review |
| Datum | 7. December 1990 |
| URL | https://www.afr.com/companies/counting-the-real-costs-of-new-technology-19901207-kanv9 |
Literaturverz. |
no |
| Fußnoten | no |
| [66.] Quelle:Svr/Norman 1999 |
| Autor | Pontus Norman |
| Titel | a study of eXtensible Markup Language (XML) |
| Datum | 25. February 1999 |
| Anmerkung | "This thesis is a part of the requirements for my (Pontus Norman’s) Master of Science degree in Computer Science at the Department of Teleinformatics, Royal Institute of Technology in Sweden." (p. 6) |
| URL | https://pdfs.semanticscholar.org/daae/6251759fc247ca60e4adf8598012c68df93f.pdf ; https://web.archive.org/web/20200225140015/https://pdfs.semanticscholar.org/daae/6251759fc247ca60e4adf8598012c68df93f.pdf |
Literaturverz. |
no |
| Fußnoten | no |
| [67.] Quelle:Svr/DeRose 1999 |
| Autor | Steven J. DeRose |
| Titel | XML Linking: An introduction |
| Datum | 27. September 1999 |
| URL | http://xml.coverpages.org/xlinkIntroDeRose199909.html |
Literaturverz. |
no |
| Fußnoten | no |
| [68.] Quelle:Svr/Ricciuti Wong 1999 |
| Autor | Mike Ricciuti / Wylie Wong |
| Titel | XML: New way to do business |
| Sammlung | CNet news |
| Datum | 3. May 1999 |
| URL | https://web.archive.org/web/20000901055305/http://cnet.com/news/0-1003-200-341987.html |
Literaturverz. |
no |
| Fußnoten | no |
| [69.] Quelle:Svr/Balogh 1999 |
| Autor | N. Balogh |
| Titel | Recommendations for medical structured data transmission in CEC/NIS countries. Analysis of structured data transmission standards for CEC/NIS usage in cardiology |
| Datum | 25. January 1999 |
| URL | http://citeseerx.ist.psu.edu/viewdoc/download?doi=10.1.1.201.4527&rep=rep1&type=pdf |
Literaturverz. |
no |
| Fußnoten | no |
| [70.] Quelle:Svr/Arbortext 1999 |
| Titel | XML for Managers. Evaluating SGML vs. XML from a Manager's Perspective |
| Herausgeber | Arbortext |
| Datum | 27. November 1999 |
| URL | https://web.archive.org/web/19991127171437/http://www.arbortext.com/Think_Tank/XML_Resources/XML_for_Managers/xml_for_managers.html |
Literaturverz. |
no |
| Fußnoten | no |
| [71.] Quelle:Svr/Enigma 1999 |
| Autor | Enigma Inc. |
| Titel | XML Adoption for Document-Based Applications |
| Jahr | 1999 |
| URL | https://web.archive.org/web/19990505003959/http://www.enigmainc.com/xml/XML-Adoption-WhitePaper.html |
Literaturverz. |
no |
| Fußnoten | no |
| [72.] Quelle:Svr/Seybold report on internet publishing 1997 |
| Autor | Seybold report on internet publishing |
| Titel | Microsoft, Inso, ArborText propose style sheet language for XML |
| Zeitschrift | Seybold report on internet publishing |
| Ort | Media, Pa. |
| Verlag | Seybold Publications Incorporated |
| Datum | 20. October 1997 |
| Jahrgang | 2 |
| Nummer | 2 |
| Anmerkung | See https://zdb-katalog.de/title.xhtml?idn=018403425 |
| URL | Copy of article is at https://www.xml.com/pub/a/SeyboldReport/ip020209.html |
Literaturverz. |
no |
| Fußnoten | no |
| [73.] Quelle:Svr/Heflin 2000 |
| Autor | Jeff Heflin |
| Titel | The SHOE FAQ |
| Herausgeber | Parallel Understanding Systems Group, Department of Computer Science, University of Maryland at College Park |
| Jahr | 2000 |
| Anmerkung | The FAQ is first recorded at the Internet Archives in 1997. The section on problems with XML is first found in this version saved to the Internet Archive on June 10, 2000. |
| URL | https://web.archive.org/web/20000610223931/http://www.cs.umd.edu/projects/plus/SHOE/faq.html |
Literaturverz. |
no |
| Fußnoten | no |
| [74.] Quelle:Svr/Bartlett 1997 |
| Autor | Bartlett, PG |
| Titel | XML - What HTML Always Wanted to Be [Abstract] |
| Sammlung | Proceedings of the SGML/XML '97, "SGML is Alive, Growing, Evolving!", Washington, D.C., USA. December 7 - 12, 1997 |
| Ort | Alexandria, VA |
| Verlag | Graphic Communications Association |
| Jahr | 1997 |
| Seiten | 527-532 |
| Anmerkung | This paper was delivered by the Vice President of Marketing, ArborText, Inc., as part of the "Business Management" track in the SGML/XML '97 Conference. |
| URL | http://xml.coverpages.org/gcaSGMLXML97bib.html |
Literaturverz. |
no |
| Fußnoten | no |
| [75.] Quelle:Svr/XML EDI Group 1999 |
| Autor | XML/EDI Group |
| Titel | Repository Focus |
| Jahr | 1999 |
| Anmerkung | This document is from a repository for documents working on the submission of a standard for XML/EDI. The authors are a collection of people from many companies: https://web.archive.org/web/19991111120951/http://www.xmledi.com/xmledigroup.htm . The working group is described in the thesis in Appendix 2 (p. 146ff) |
| URL | https://web.archive.org/web/19991118230529/http://www.xmledi.com/repository/repository.htm, linked from https://web.archive.org/web/19991009055853/http://www.xmledi.com/repository/ |
Literaturverz. |
yes |
| Fußnoten | no |